The barrier to entry for building software has collapsed twice. First, No-Code platforms (Bubble, Adalo, Airtable) democratized creation through visual drag-and-drop interfaces. Now, Vibe Coding using LLMs to generate entire codebases via "vibes" and natural language prompts has made it possible to ship sophisticated apps without ever typing a semicolon.
This speed enables MVPs to ship in hours. The hype delivers on the promise: Syntax is no longer a requirement. But security offers a firm counterpoint. Applications built via "vibes" or "clicks" often expose more vulnerabilities than traditional apps because the builder is farther away from the underlying logic. Securing them demands deliberate, intentional thought. Whether you are dragging a button or prompting an AI, the fundamental invariants of security remain supreme.
The Modern "Build-Without-Syntax" Stack
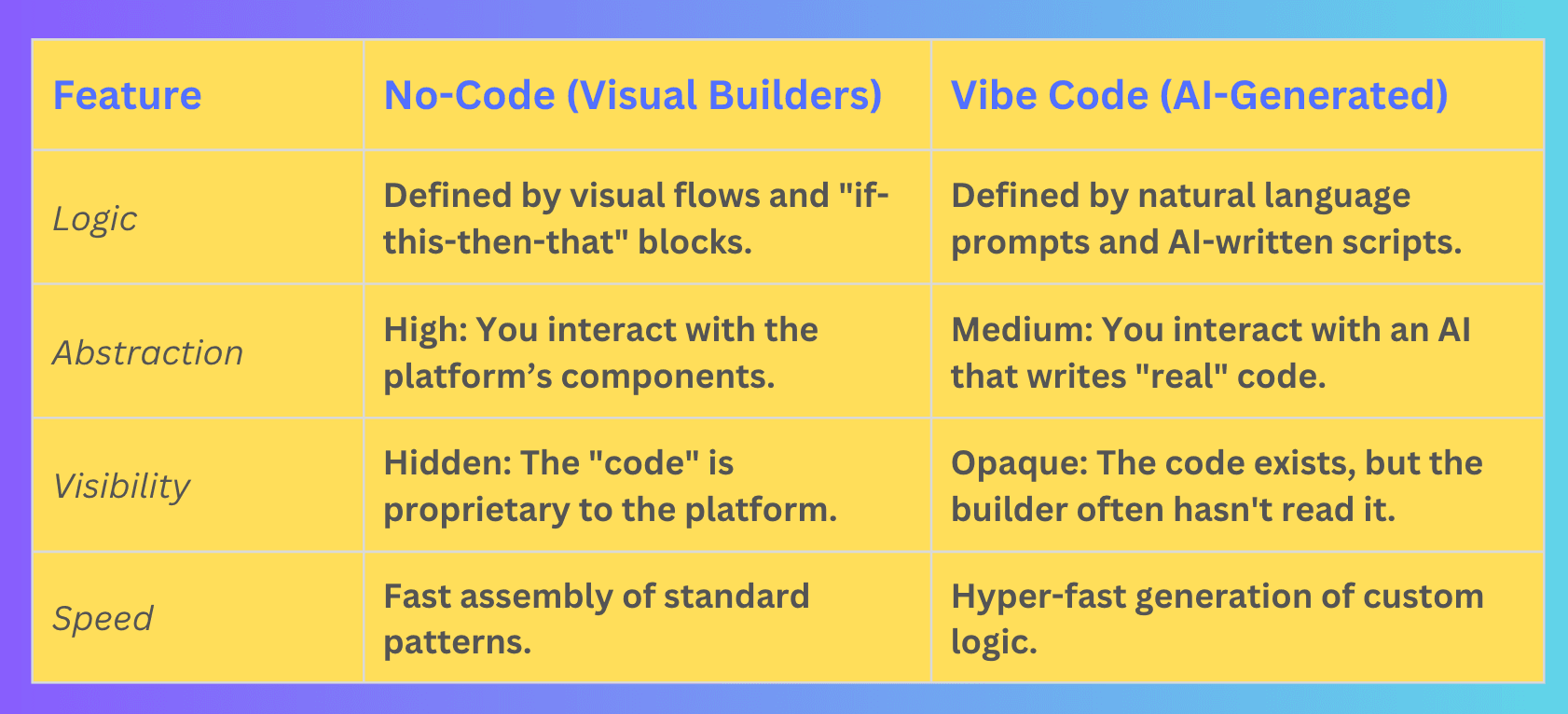
To understand the risks, we have to look at how these two movements differ in architecture:
In No-Code, the "green zones" of strength are the platform-managed auth and auto-scaling. In Vibe Code, the strength is the ability to generate complex, bespoke features instantly. However, the "red zones" are expanded: Vibe Coding introduces "Shadow Logic" code the AI wrote that you don't fully understand, which might contain "hallucinated" security practices or deprecated, vulnerable libraries.
Why the New Stack Amplifies Security Blind Spots
- The "Vibe" Overhang: In Vibe Coding, if you prompt "Make a login page," the AI might prioritize a beautiful UI over secure password hashing or session management. If you don't explicitly "vibe" for security, the AI might take the path of least resistance.
- Insecure Direct Object References (IDOR):
- No-Code: A Bubble workflow might say "Update row where email = input."
- Vibe Code: The AI might write
app.post('/update', (req, res) => { User.update(req.body.id) })without checking if the current user owns that ID.
- Prompt Injection & AI Logic Flaws: Vibe-coded apps often rely on LLMs to process user input. A clever attacker can use prompt injection to trick the app’s internal logic into revealing data or bypassing permissions.
- The Template Trap: Just as No-Code users clone "leaky" CRM templates, Vibe Coders often copy-paste prompts from "Top 10 SaaS Prompts" threads. These prompts rarely include instructions for rate limiting, CSRF protection, or input sanitization.
The Thought Gap: In traditional coding, security is often caught during code reviews. In No-Code/Vibe Code, there is no "review" because there is no "writing" there is only "generating." This hides vulnerabilities deep within UI configurations or 5,000 lines of AI-generated TypeScript that the builder never intended to read.
Pitfalls That "Just Vibes" Overlook
- Prompt-Generated Secrets: AI agents often "helpfully" hardcode mock API keys or suggest insecure environment variable setups. If the builder just hits "Deploy," those secrets are live.
- The "It Works" Fallacy: Because the app looks and functions perfectly, the builder assumes it is secure. Security is a non-functional requirement; you can't see a lack of encryption just by looking at the "vibes."
- Recursive Dependencies: Vibe-coding agents often pull in dozens of npm packages to solve simple problems. This creates a massive, unmanaged attack surface of third-party vulnerabilities.
Securing the Stack: The Policy Layer
Securing an app you didn't manually type requires shifting your focus from syntax to policy.
1. Data Policies (The "Hard" Perimeter)
Don't rely on the UI to hide data. Use Row-Level Security (RLS) in your database (like Supabase or Xano). Even if your Vibe-Coded frontend has a bug, the database should say: "I don't care what the 'vibes' are; User A cannot see User B's data."
2. Explicit Prompting (For Vibe Coders)
When using AI agents, your prompts must include a security persona.
- Bad Prompt: "Build me a checkout page."
- Good Prompt: "Build me a checkout page. Use server-side validation for all prices, implement rate limiting on the API endpoint, and ensure no PII is logged in plain text."
3. Integration Locks
Use scoped API keys. If your "Make.com" automation only needs to add a row to Airtable, don't give it a key that can delete the whole base.
4. The "Vibe" Audit
If an AI agent writes your code, you are now a Code Reviewer, not just a builder. Use a second, different AI (like a "Security Analyst" GPT) to audit the code generated by the first one. Ask it: "Find the OWASP Top 10 vulnerabilities in this generated file."
Scaling Thoughtful Development
The goal isn't to slow down. The goal is to ensure your speed doesn't lead to a crash.
Checklist for the "Modern Builder":
- Identity: Is authentication handled by a trusted provider (Clerk, Auth0, Stytch) or just a "vibe" login?
- Validation: If I enter
<script>alert('xss')</script>into a form, does the app break? - Exposure: Are my database API keys visible in the browser's "Network" tab?
- Logging: If a breach happens, do I have a trail of who accessed what?
Final Thought: The Real Stack
No-code and Vibe Code provide the pixels, the logic, and the speed. But the human mind provides the perimeter. Truly secure apps are not the ones with the most complex syntax; they are the ones where the builder took 15 minutes to think about :





