At Axeploit, we view the modern software supply chain as a massive, distributed house of cards built on a foundation of implicit trust. We trust our package managers (npm, pip, RubyGems) to fetch exactly what we asked for, and we trust our private registries to keep our internal code secret. But what happens when the package manager acting with perfect technical accuracy decides that an attacker's public package is "better" than your private one?
This is the essence of Dependency Confusion (also known as a namespace confusion attack). It isn’t a bug in the code; it’s a flaw in the fundamental logic of how package managers resolve dependencies across multiple, often conflicting, sources.
1. The "Default-to-Public" Logic Flaw
To understand why this is a nightmare for enterprise security, we must look at the "heuristics" of a typical build server. Most large organizations use a hybrid approach to dependencies, utilizing both public packages from registries like npmjs.org and private internal libraries hosted on a private registry.
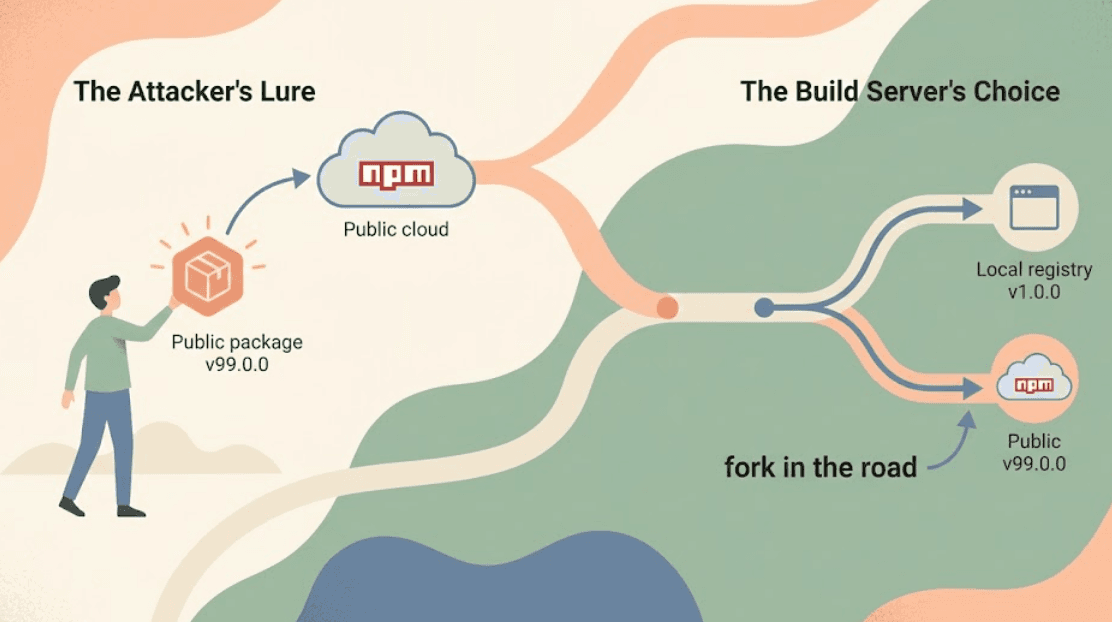
When an install command is executed, the package manager searches all configured registries for the specified package. Many package managers are designed to be "helpful" by prioritizing the most recent version available. If an internal package (e.g., v1.2.0) also exists on a public registry with a higher version number (e.g., v99.1.0), the manager assumes the public one is the "latest" and fetches it.
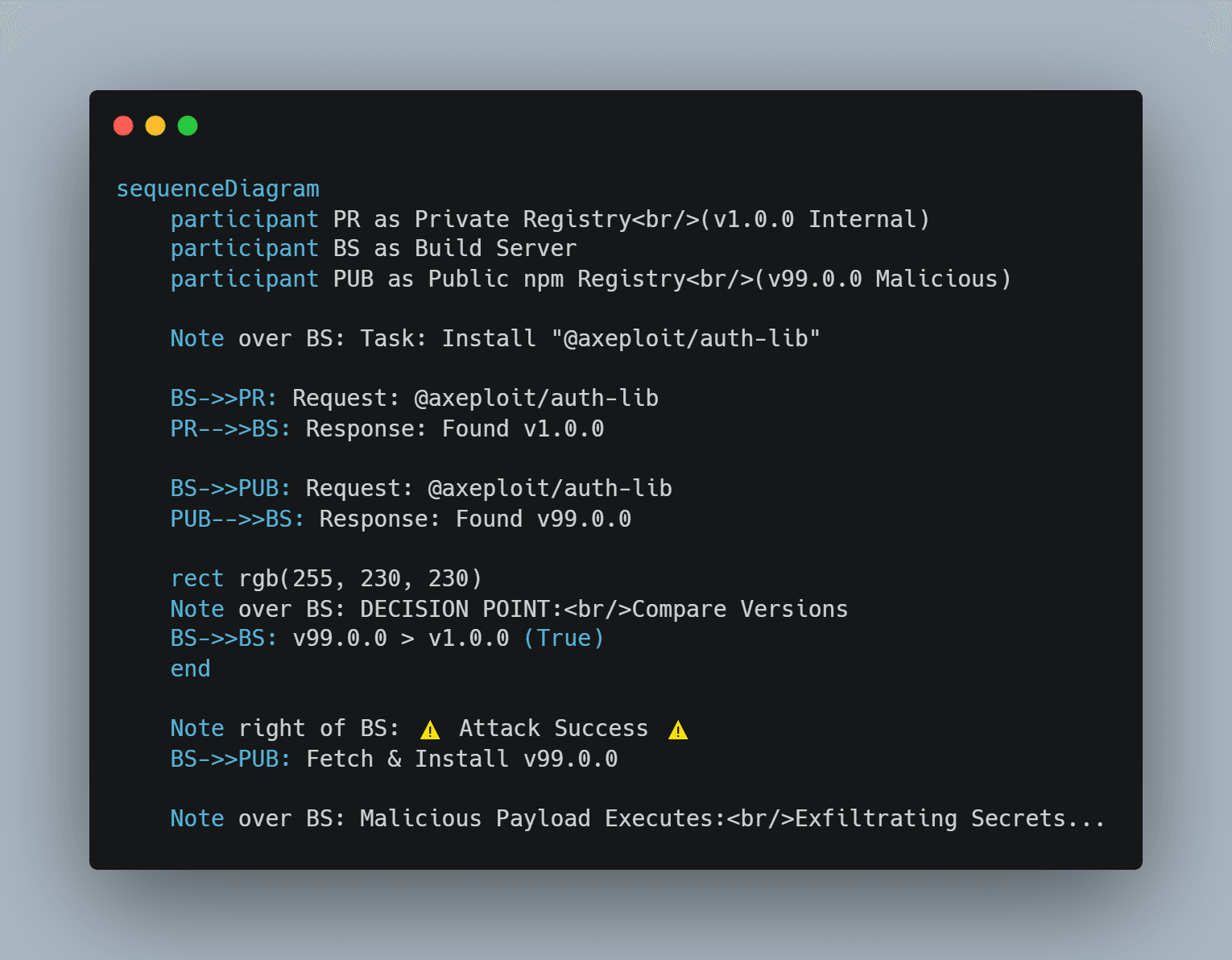
An attacker simply needs to discover the name of your internal package and upload a dummy version to the public registry with an absurdly high version number. Your build server will see the update and convinced it’s doing the right thing pull down the attacker's code.
2. Anatomy of a Supply Chain Poisoning
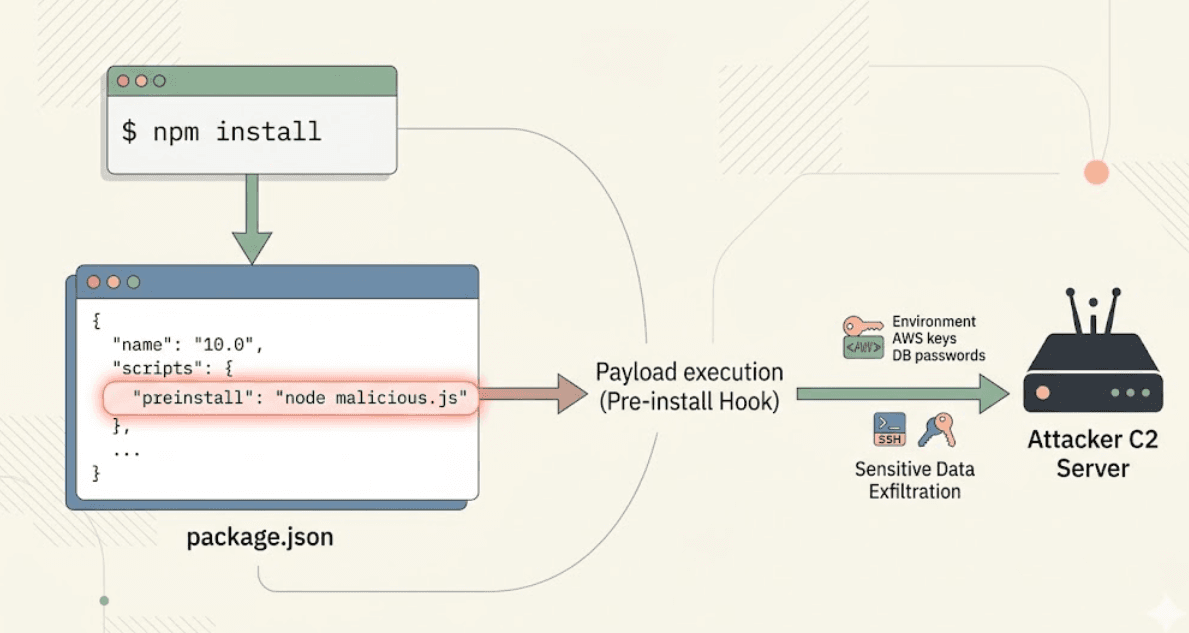
Dependency confusion is particularly lethal because it leverages Pre-install Code Execution. Most package managers support "hooks" scripts that run automatically during installation. An attacker can include a preinstall hook in their malicious package that executes immediately upon download.
When a developer or build agent runs the installation, the malicious payload executes with the same privileges as that user. This script can exfiltrate environment variables containing AWS keys or database passwords, establish a reverse shell for persistent access, or even modify source code to inject backdoors before compilation.
3. The Discovery Phase: Mapping Your Internals
You might think internal package names are secret, but attackers use several "leakage points" to find them:
- Public Source Maps: Production JavaScript bundles often include source maps that reveal the names of all imported modules.
- Accidental Commits: Developers occasionally push
package.jsonfiles to public GitHub repositories. - Recruitment Postings: Detailed job descriptions often list the specific internal technologies and library names used by engineering teams.
- Docker Images: Publicly available Docker images may contain build logs or manifest files.
Once a name is known, the poisoning begins.
4. Why Standard Firewalls Fail
This is a "Private Investigator" problem, not a "Bouncer" problem. A firewall acts as a bouncer; it sees a legitimate request from a trusted build server to a trusted public registry. Because the traffic is encrypted (HTTPS) and the destination is known, the bouncer lets it through.
The firewall lacks the context to know that your internal library should only ever come from your internal server. To the network layer, it is just another legitimate library download.
5. The Axeploit Defense Strategy: Immunizing Your Registry
At Axeploit, we help organizations implement a "Zero Trust" approach to dependencies. You cannot prevent attackers from uploading packages to public registries, but you can prevent your tools from looking for them there.
A. Namespace Scoping (The Primary Defense)
Most modern package managers support "scopes" or "namespaces." You should officially claim your organization's scope (e.g., @axeploit/) on public registries, even if you never intend to publish there. This prevents an attacker from registering that namespace first.
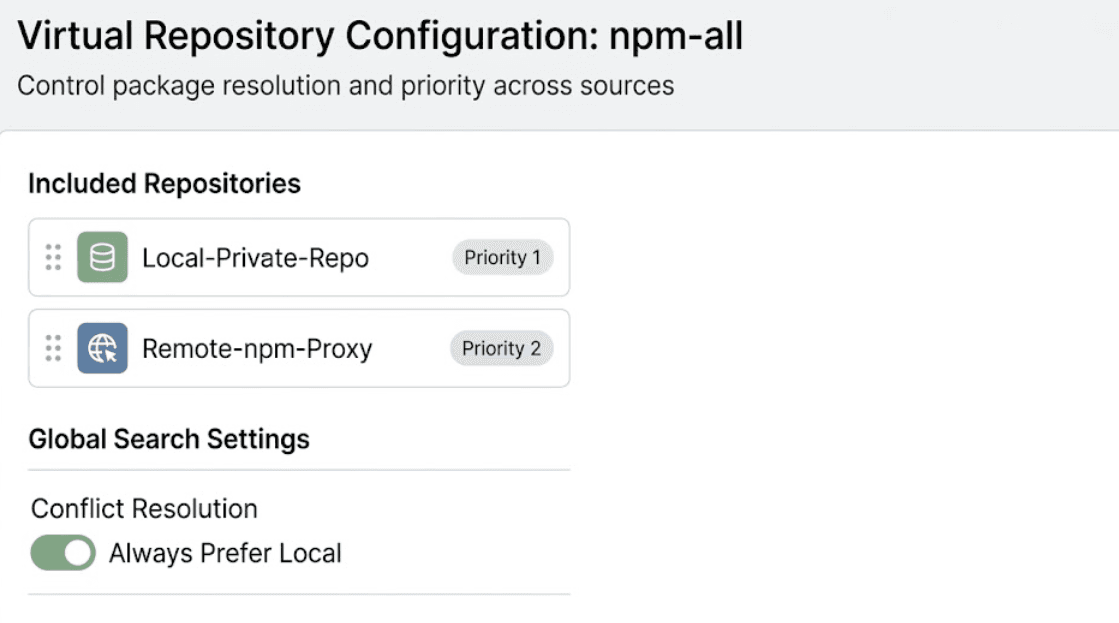
B. Upstream Configuration and Virtual Repositories
Configure your private registry (like Artifactory or Nexus) to prioritize local repositories over remote proxies. Use virtual repositories that explicitly define the search order: local first, then remote. This ensures the registry never even queries the public internet for a "newer" version of a local package.
C. Lockfiles and Integrity Hashes
Always commit package-lock.json, yarn.lock, or poetry.lock to your version control. These files record the specific version and the cryptographic hash of the package originally installed. If an attacker tries to swap the package, the build will fail because the integrity hashes won't match.
Conclusion: Don't Let Your Tools Betray You
Dependency confusion is a stark reminder that software security is about more than just fixing bugs in your own code; it's about understanding the behavior of your entire ecosystem. Your package manager is a powerful tool, but without explicit configuration, it is a tool that can be turned against you.
Is your registry poisoned? Axeploit can help you audit your supply chain before the next install becomes a security event.





