If you are a modern developer, a cybersecurity engineer, or a CISO navigating the fast-moving tech landscape of early 2026, you already have enough on your plate. You are shipping microservices, securing APIs, mitigating AI-generated vulnerabilities, and trying to stay ahead of the next zero-day exploit. To many builders, “quantum computing” still sounds like an abstract buzzword, a sci-fi concept reserved for university research labs and distant corporate roadmaps.
But while you are entirely focused on today’s fires, advanced threat actors are quietly preparing for tomorrow. They aren't waiting for quantum computers to hit the mainstream market to start their attacks. They are already executing them right now.
If you assume that quantum computing threats are a “2030s problem,” you are leaving your application fundamentally exposed. Here is why the post-quantum countdown has already started, how hackers are exploiting current encryption algorithms today, and how you can ensure the future-proofing of your infrastructure before the clock runs out.
The Illusion of Infinite Time: The Fall of RSA and ECC
To understand the threat, we have to look at how we currently secure the internet. For decades, our data security has heavily relied on asymmetric encryption algorithms, primarily RSA (Rivest-Shamir-Adleman) and ECC (Elliptic Curve Cryptography).
These cryptographic systems are built on complex mathematical problems, such as factoring massive prime numbers or calculating discrete logarithms over elliptic curves. For a classical, traditional computer, solving these equations to derive a private key from a public key would take millions of years. For all intents and purposes, it’s an impenetrable mathematical fortress.
But a Cryptographically Relevant Quantum Computer (CRQC) doesn't work like a traditional machine. By leveraging the bizarre, mind-bending properties of quantum mechanics, specifically superposition and entanglement, alongside specialized formulas like Shor's Algorithm, a quantum computer can slice through these math problems in a matter of hours, if not minutes.
Once a CRQC comes online, the underlying math of RSA and ECC collapses. Every secure API connection, every VPN tunnel, every encrypted database, and every digital signature will be instantly readable. The fortress walls simply vanish.
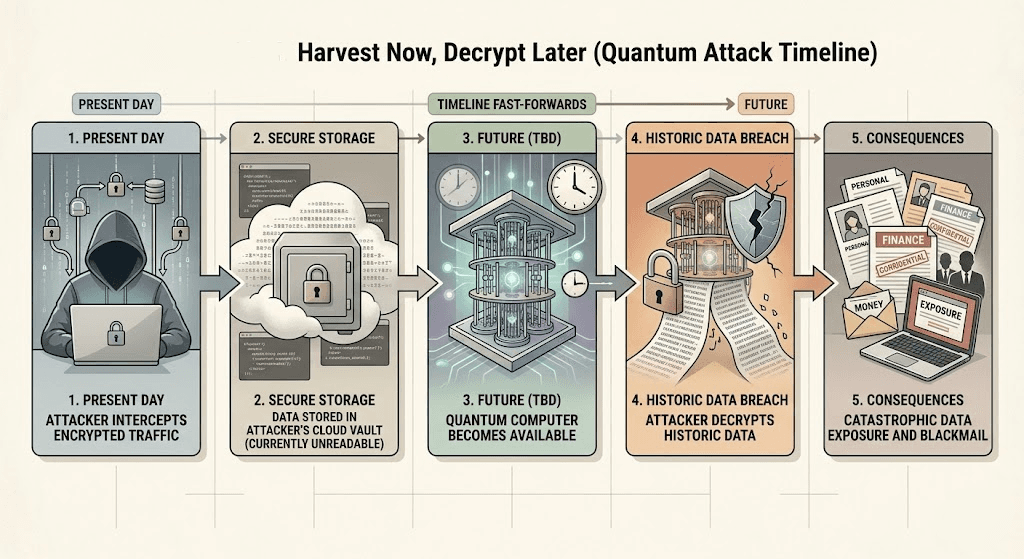
The Ticking Time Bomb: “Store Now, Decrypt Later” (SNDL)
You might be thinking: “Okay, but a CRQC capable of breaking RSA doesn't exist yet, right? I have plenty of time to upgrade my encryption.”
This is the single most dangerous misconception in modern cybersecurity. Enter the “Store Now, Decrypt Later” (SNDL) attack.
Hackers, particularly state-sponsored actors and highly funded cybercriminal syndicates, know exactly what is on the horizon. So, rather than expending resources trying to break your 256-bit encryption today, they are simply stealing your encrypted data and hoarding it on massive, dirt-cheap cloud storage servers.
They are scraping encrypted database dumps, capturing encrypted network traffic, and stealing locked password vaults. They can't read the data right now, but they don't need to. They are just putting it in a vault and waiting. The moment a viable quantum computer becomes available, they will unlock the vault.
If you are handling proprietary source code, classified government data, long-term financial records, or critical healthcare information, an SNDL attack means your data is effectively already breached. You just haven't felt the impact yet.
Demystifying Post-Quantum Cryptography (PQC)
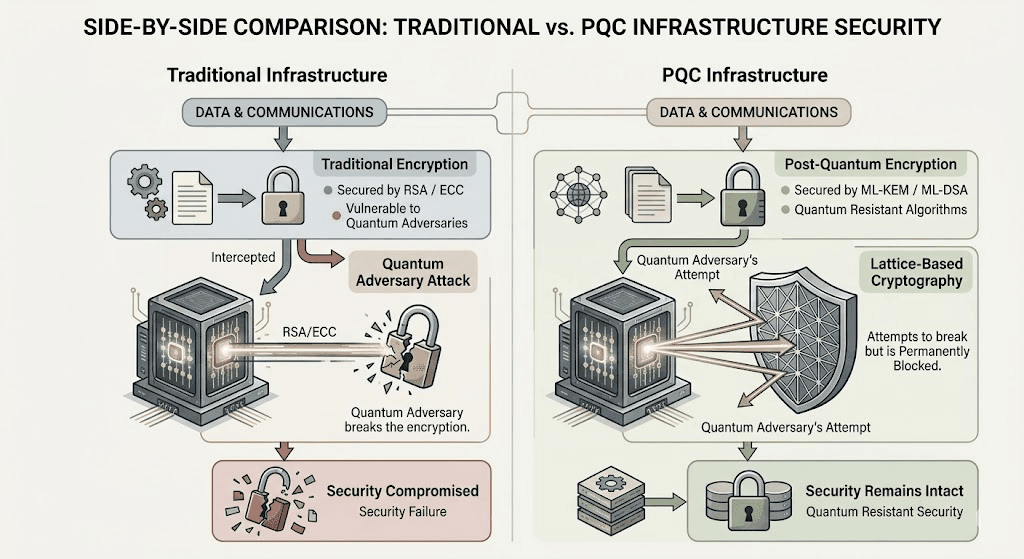
The good news? You don't need a quantum computer to defend against a quantum computer. The solution lies in Post-Quantum Cryptography (PQC).
PQC refers to a new generation of cryptographic algorithms that run flawlessly on our standard, classical computers but are built on entirely different mathematical foundations (like lattice-based math) that even quantum computers struggle to solve.
The cybersecurity world has been racing to establish these new rules. After years of rigorous testing, the National Institute of Standards and Technology (NIST) officially finalized the first PQC standards:
- FIPS 203 (ML-KEM): The Module-Lattice-Based Key-Encapsulation Mechanism. This is designed for secure key exchange, protecting data as it moves across the network (think: a quantum-safe replacement for your TLS handshakes).
- FIPS 204 (ML-DSA) & FIPS 205 (SLH-DSA): These are specifically focused on digital signatures. They ensure that an identity can be verified and that data hasn't been tampered with crucial for software updates, authenticating APIs, and securing digital identities.
Future-Proofing Your App: A Pragmatic DevSecOps Guide
Transitioning an entire software architecture to PQC is a massive undertaking, but as a developer or CISO, you need to start laying the groundwork immediately. Here is how you can begin future-proofing your applications today:
1. Embrace Crypto-Agility
If you hardcode specific encryption algorithms (like AES-256-GCM or RSA-2048) directly into your application's business logic, you are setting yourself up for a painful, code-breaking migration. Crypto-agility means designing your systems so that cryptographic algorithms can be swapped out easily via configuration files, without rewriting the core application code. If a vulnerability is found in a current algorithm, your architecture should allow you to pivot to a PQC standard seamlessly.
2. Inventory Your Cryptographic Assets
You cannot protect what you cannot see. Most organizations have no idea where all their encryption keys live, which internal microservices use deprecated algorithms, or what third-party libraries rely on legacy cryptography. You need to map out your entire cryptographic landscape. Identify the protocols at highest risk (TLS endpoints, VPNs, code signing) and plan their exact migration paths.
3. Adopt a Hybrid Cryptography Approach
Because PQC algorithms are relatively new, the industry consensus for 2026 is to use a “hybrid” approach. This means wrapping your data in both a traditional, battle-tested algorithm (like ECC) and a new PQC algorithm (like ML-KEM). If a theoretical mathematical flaw is unexpectedly discovered in the new PQC algorithm, the classical encryption still protects you against standard hackers. If a quantum computer attacks, the PQC layer holds the line.
How Axeploit Fits into Your Post-Quantum Strategy
Migrating to Post-Quantum Cryptography is a complex engineering challenge, and complex migrations inevitably lead to human error. A developer might accidentally leave a legacy API endpoint running with outdated RSA certificates, or misconfigure a new ML-KEM integration, punching a hole straight through your DevSecOps pipeline.
This is where traditional static code analysis falls short, and where the Axeploit API Security Checker becomes your ultimate safety net. While you work on upgrading your architecture, you need continuous visibility into how your live applications are behaving.
Our automated vulnerability scanner doesn't just read your code; it actively attacks your live, running application from the outside, mimicking the exact behavior of a malicious hacker. If you have an internal API that is inadvertently exposing sensitive data due to weak or deprecated encryption protocols, Axeploit’s dynamic scanner will catch it. It flags the vulnerability and shows you exactly how to patch it before you go live.
Conclusion: The Clock is Ticking
The transition to post-quantum security isn't just an IT compliance checkbox; it is a fundamental shift in how we protect the internet's most sensitive information. The encrypted data you confidently ship today could be decrypted and weaponized by adversaries tomorrow.
Don't wait for quantum computers to hit the evening news before you start caring about cryptography. Adopt a crypto-agile mindset, begin mapping your migration to the new NIST standards, and let Axeploit continuously scan your blind spots.





