If you are a cloud engineer, a developer, or a CISO in early 2026, your infrastructure looks radically different than it did just a few years ago. We are fully entrenched in the era of serverless architectures, automated microservices, and AI-driven deployments. The modern “vibe coder” is shipping features at breakneck speeds, leaning heavily on the scalability of cloud providers like Amazon Web Services (AWS).
But in the race to build faster and scale infinitely, an invisible threat has taken root in our cloud environments. When we think of major corporate data breaches, Hollywood has conditioned us to imagine sophisticated hackers launching complex, million-dollar “zero-day” exploits.
The reality is far less cinematic, but far more dangerous. The vast majority of modern cloud breaches do not stem from elite, unpatchable software flaws. They stem from simple, easily preventable cloud misconfigurations. And at the very center of this vulnerability epidemic is AWS IAM (Identity and Access Management).
Here is exactly why AWS IAM misconfigurations have become the silent killers of cloud security, how attackers exploit them to tear through your infrastructure, and what you can do to lock down your cloud before your data is exfiltrated.
The Keys to the Kingdom: Understanding AWS IAM
To understand the threat, we first need to strip away the jargon. AWS IAM is essentially the digital bouncer for your entire cloud infrastructure. It dictates who (a user, a developer, or an application) can do what (read a database, delete a server, change a password) and where (in which specific part of your cloud environment).
Think of IAM like a keycard system in a highly secure hotel. A guest should only have a keycard that opens their specific room. A housekeeper might have a keycard that opens all rooms on a specific floor. The hotel manager has a master keycard that opens everything.
In AWS, these “keycards” are called IAM Policies, and they are attached to IAM Roles or Users. When perfectly configured, everyone and everything operates on the Principle of Least Privilege, having only the exact access they need, and nothing more. But when developers are rushing to get a new app deployed, perfect configuration is often the first casualty.
The Most Common (and Deadly) Developer Errors
Nobody intentionally leaves their cloud infrastructure exposed. Cloud misconfigurations are born out of friction, tight deadlines, and the sheer complexity of modern cloud environments.
1. The Danger of Overly Permissive Roles (The “Wildcard” Trap)
Imagine a developer is building a new application that needs to read a few files from an AWS S3 bucket (a digital storage folder). The developer tries to connect the app, but they get an “Access Denied” error. After thirty minutes of frustrating debugging, they decide to take a shortcut.
Instead of writing a strict IAM policy that only grants s3:GetObject (read access) to one specific bucket, they use a “wildcard” (*). They grant the application s3:* (the ability to do anything to any storage bucket in the account) or worse, AdministratorAccess.
The app works! The developer closes the ticket and moves on. But they just handed a master hotel keycard to a single application. If a hacker finds even a minor flaw in that application, they don't just compromise the app, they inherit that master keycard and gain full control over your cloud storage.
2. Hardcoded Access Keys
Sometimes, applications need to talk to AWS from outside the AWS network. To do this, developers generate long, complex passwords called IAM Access Keys.
A fatal, yet incredibly common mistake is “hardcoding” these keys directly into the application's source code for convenience. When that code is pushed to a repository like GitHub or GitLab, those keys are exposed. Attackers deploy automated bots that scan public and private repositories 24/7. The moment a developer accidentally pushes an AWS Access Key, a bot steals it, and the attacker is inside your cloud environment in a matter of seconds.
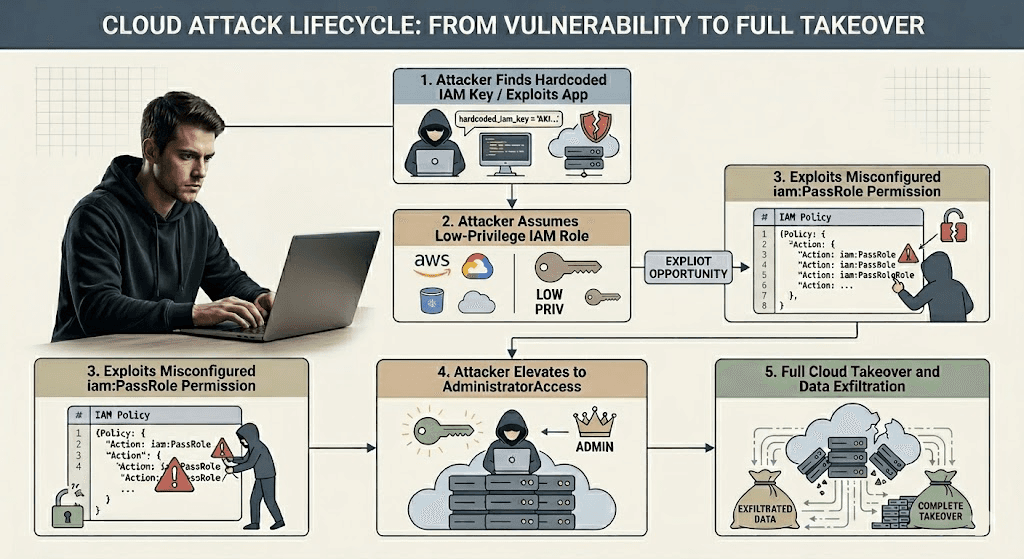
How Attackers Pivot: The Art of Privilege Escalation
When an attacker successfully breaches your environment, perhaps by finding a hardcoded key or exploiting a minor bug in an application with a wildcard policy, they rarely land exactly where the sensitive data is stored. They usually start with low-level access.
This is where the nightmare of privilege escalation begins.
Privilege escalation is the hacker technique of turning low-level access into high-level, administrative control. In a traditional on-premise network, hackers pivot by jumping from server to server. In the cloud, they pivot by jumping from identity to identity.
If an attacker compromises an application running on an EC2 instance (a virtual server), they will immediately query the server's internal metadata to steal its temporary IAM credentials. If that IAM role has the permission to create new policies (iam:CreatePolicy) or attach policies to users (iam:AttachUserPolicy), the attacker will simply rewrite their own permissions. They will magically grant themselves AdministratorAccess, locking your team out and holding your infrastructure hostage.
Securing Your Cloud: Moving Beyond Passive Checks
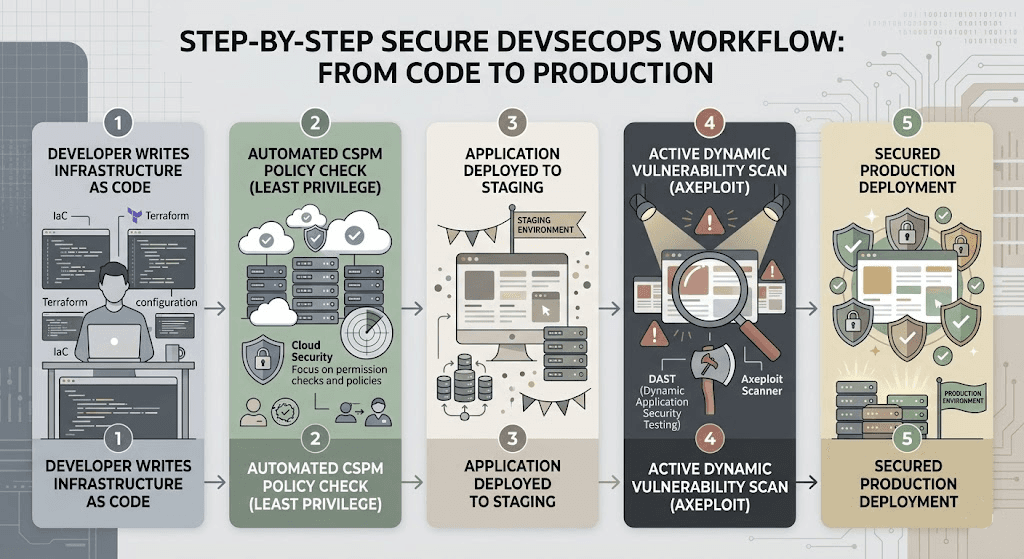
As cloud environments grow, relying on manual reviews to catch a single misplaced wildcard character in thousands of JSON files is mathematically impossible. This is why the industry has shifted toward CSPM (Cloud Security Posture Management).
CSPM tools automatically continuously monitor your cloud environments, comparing your actual configurations against strict security best practices. However, passive monitoring is only half the battle. You need to know how an attacker can actually chain these misconfigurations together.
Defusing the Threat with Axeploit
You cannot fix what you cannot see, and you cannot secure a modern cloud environment with outdated, static tools. This is where Axeploit bridges the gap between cloud architecture and application security.
While your DevOps team works to tighten IAM roles, the Axeploit automated vulnerability scanner acts as your active, final line of defense. Axeploit doesn’t just passively read your configuration files; it safely and actively attacks your live, running applications exactly how a malicious hacker would.
If a developer accidentally deploys an API endpoint that is tied to an overly permissive IAM role, or if a Server-Side Request Forgery (SSRF) vulnerability allows an attacker to steal your cloud metadata credentials, Axeploit’s dynamic scanner will catch it. We flag the exact exploit path and show you precisely how to lock down your permissions before you go live.
Conclusion: Build Fast, But Verify
The shift to cloud computing in 2026 has given us unprecedented power and agility. But with that power comes the immense responsibility of managing identity. AWS IAM misconfigurations are the silent killers of cloud security precisely because they don't look like malware; they look like normal, functioning code right up until the moment they are exploited.
By enforcing the principle of least privilege, eliminating hardcoded secrets, and integrating active, automated security testing into your deployment pipeline, you can neutralize these silent threats.





