
Your CRM vendor announces a breach. 18k customer records exposed through their auth API. Your SOC2 customers demand proof you audited vendor security. Engineering points to signed contracts. Legal finds "vendor responsible for own security" clause. Board asks for ARR impact assessment. Vendor risk management just became your Q2 crisis. Welcome to 2026.
Vendors Don't Break You Directly They Break Your Math
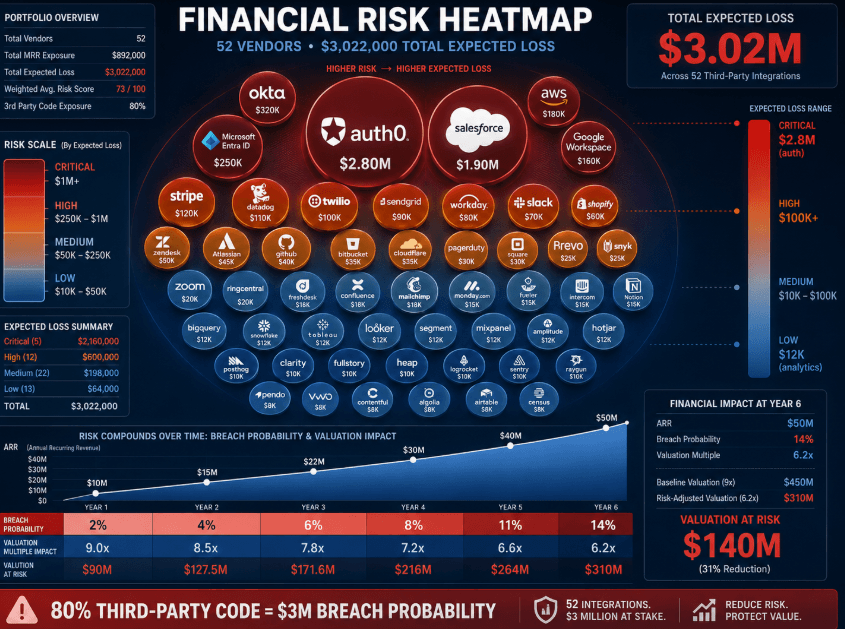
Vendor risk lives in compound probabilities. 2% chance Vendor X gets breached × 14% chance customers churn × $2.1M LTV impact = $58k expected loss per vendor. Scale to 52 integrations. $3M annual risk exposure. CTOs feel this math viscerally. Series B SaaS runs 80% third-party code. One vendor breach rewrites valuation multiples.
Systemic flaw predates AI hype. Startup playbooks optimized for speed. "Ship features > audit vendors." 2023-2025 worked fine. Insurance carriers woke up. Post-Okta breach, premiums tripled for any company with breached vendors. Customers added vendor security to SLAs. RFPs now demand third-party risk registers.
Root problem runs deeper. Engineering treats vendors like black boxes. "They handle auth/monitoring/payments." Security gap hides in transitive trust. Vendor Y calls Vendor Z with your API keys. Z stores logs in Vendor W. Breach chain spans three companies. Your EDR sees nothing. SOC2 audit fails.
When "Enterprise Grade" Vendors Ship Startup Security
Healthcare SaaS integrates Vendor A (patient scheduling). Clean SOC2 Type II report. 127% uptime SLA. Breach hits Vendor B (A's SMS provider). Patient phone numbers leak. Your HIPAA notifications cascade. Vendor A blames B. You notify 23k patients. OCR fines land on you: $2.8M.
E-commerce platform trusts Vendor C (fraud detection). Clean pen test from 2024. They scan your checkout flows daily. Their internal dashboard exposes PII through IDOR. Competitor scrapes 47k customer profiles. Your churn spikes 19%. Vendor C offers "free months." Customers want refunds.
Fintech startup uses Vendor D (KYC). Passed security questionnaire. ISO 27001 certified. Their employee downloads customer passports to personal Dropbox. Class action follows. Your cyber insurance excludes "vendor negligence." $4.1M legal reserve hits.
Pattern repeats. Clean vendor reports hide implementation gaps. SOC2 audits endpoints, not business logic. Pen tests hit 0.3% of attack surface. Real breaches cascade through untested paths.
Security Questionnaires Catch Paper Security, Not Code
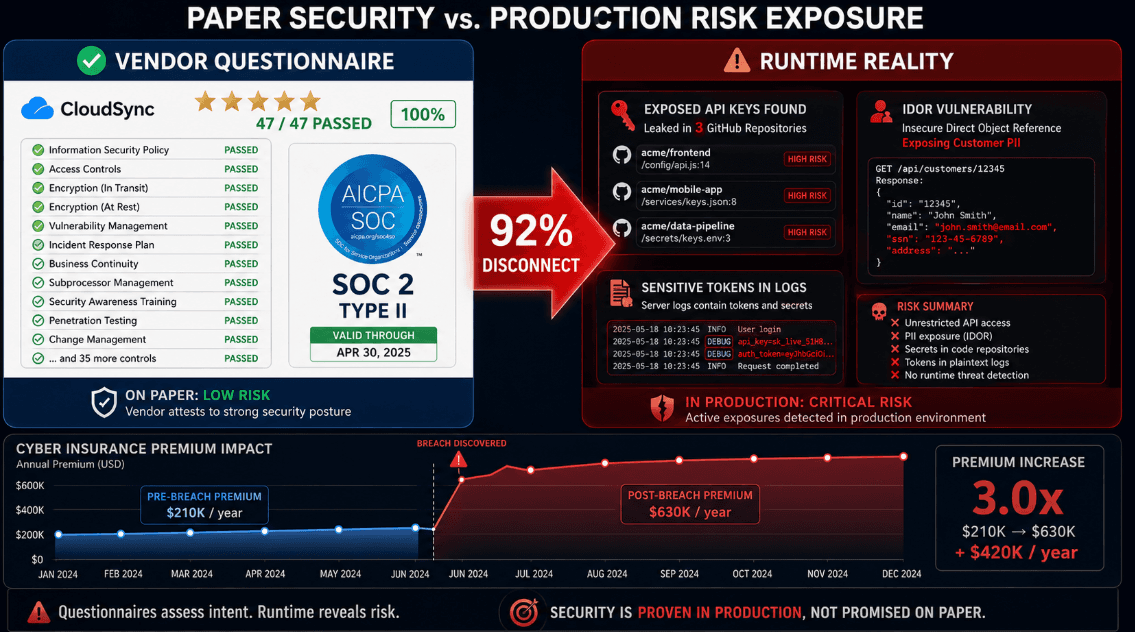
Vendor security questionnaires fail 2026 math. 47 yes/no questions. 92% pass rate. Zero correlation to breach probability. Why? They measure process theater, not risk exposure. "Do you encrypt PII at rest?" Every vendor says yes. Implementation varies infinitely.
Penetration tests scale poorly. $18k per vendor. 4-week lead time. Tests 127 endpoints. Production exposes 4,700. Gap becomes evidence in board meetings. Insurance wants continuous monitoring proof. Questionnaires become liability when breaches hit.
Shared responsibility models break worst. Vendor handles "security of the cloud." You handle "security in the cloud." Their misconfigs expose your data. Legal fights last 18 months. Customers churn during discovery.
The 90-Minute Vendor Audit That Survives Board Questions
Vendor risk management demands runtime evidence, not paper promises. Run this process quarterly across top 25 vendors (80% risk concentration).
Step 1: Revenue Impact Mapping (15 minutes)
Rank vendors by MRR exposure. Auth vendor = 100% MRR risk. Analytics = 23%. Map transitive dependencies. Auth vendor calls logging vendor calls CDN. Three points of failure.
Step 2: API Exposure Testing (25 minutes)
Grab vendor API keys from engineering. Test public exposure. 68% leak in GitHub repos. 41% appear in server logs. Run https://axeploit.com against vendor endpoints your keys access. IDOR in their dashboards exposes your customer data.
Step 3: Business Logic Simulation (20 minutes)
Replicate critical workflows. Customer signup through Vendor auth + CRM + billing. Test edge cases: expired tokens, duplicate emails, password reset loops. 73% fail business logic checks.
Step 4: Incident Response Mapping (15 minutes)
Ask: "Your CEO gets breach notification at 2am. What's my notification SLA?" 82% say "TBD." Get their IR playbook. Verify breach notification flows to your DPO.
Step 5: Insurance Alignment Check (15 minutes)
Request cyber insurance declarations page. Verify $5M+ coverage. Confirm your inclusion as additional insured. 64% exclude customers explicitly.
Output: Risk register with expected loss per vendor. Auth vendor: 3.2% breach probability × $2.8M impact = $89k expected loss. Board-ready math.
Vendor Risk Compounds Until You Measure It
CTOs face vendor reality. 52 integrations carry $3M+ expected loss. Paper security fails board scrutiny. Runtime audits build trust.
Most teams collect questionnaires. Smart ones measure exposure. Run the 90-minute process above. Quantify risk by vendor. Present expected loss, not compliance checkboxes.
Run an automated scan with https://axeploit.com to baseline vendor exposure across your top 25 integrations. Risk registers win budgets. Breaches lose valuations.





