Ease completely defines modern software development stacks across the entire industry. Low-code platforms provide intuitive drag-and-drop canvases for rapid prototyping. AI-powered code completion suggests entire functions with perfect syntax. Serverless functions eliminate infrastructure management entirely. One-click deploy buttons handle complex orchestration automatically. Software emerges completely frictionless from concept to production. Prototypes transform into revenue-generating products overnight through unprecedented velocity.
Ease actively conceals risk throughout every layer of the stack. The simplest development paths systematically skip essential validations and security checks. Pre-built templates inherit hidden flaws from their creators. Blazing velocity completely buries comprehensive security audits under feature momentum. Easiest builds ship to production fastest because they require minimal configuration. However, they also prove most vulnerable to real-world attacks.
Anatomy of Easy Builds
Easy development approaches prioritize rapid iteration cycles above all other considerations. Bubble enables sophisticated workflows through visual programming interfaces. Firebase rules control data access through simple JSON declarations. Vercel serverless functions deploy with zero infrastructure configuration required. No boilerplate code slows progress. No complex configurations demand expertise.
Risk hides deliberately within sensible-sounding defaults throughout every layer. Public read access control lists expose data unnecessarily. Unlimited function invocations enable cost-based attacks. Client-side secrets embedded in JavaScript become immediately visible to attackers.
To visualize this dangerous tradeoff clearly, picture a comprehensive pipeline breakdown structured as a flowchart that traces easy builds from initial template selection through to live production deployment, breaking down each transformation step visually for complete analysis. The green zones highlight exactly where ease wins decisively, enabling rapid cycles with minimal friction across every phase. The red layers stack progressively throughout the pipeline, showing exactly how risk accrues silently with each step that skips proper scrutiny and validation.
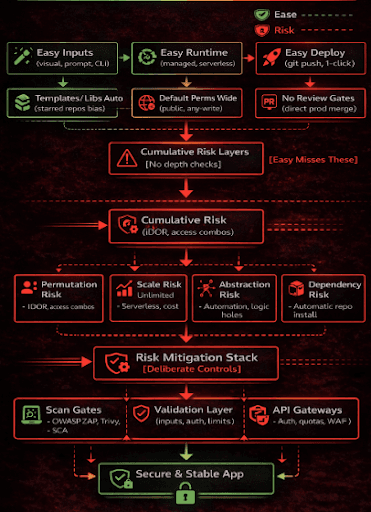
Ease flows smoothly through all the green zones of the flowchart, delivering unprecedented velocity from template selection through one-click deployments that require zero infrastructure knowledge. However, red layers stack relentlessly throughout the entire pipeline, demonstrating how each successive step that prioritizes ease over scrutiny compounds risk exposure exponentially without developers ever noticing during rapid iteration cycles.
How Ease Multiplies Risk Exposure
Templates gain popularity specifically because they earn GitHub stars through impressive demos. The riskiest templates proliferate fastest through viral sharing. So-called "Quick auth kits" embed production JWT secrets directly in example code that developers copy blindly.
Managed runtimes deliberately abstract infrastructure complexity away from developers. This abstraction forfeits essential control over runtime behavior completely. Lambda cold starts leak environment variables through verbose logging. App Engine scales functions unbounded without cost controls or rate limits.
CLI deployments bypass traditional safety gates entirely. No staging environments validate behavior first. Production becomes the first real contact with live traffic and attacks.
Quantified analysis reveals troubling patterns: easy stacks experience breaches 3x faster according to Snyk data analogs across similar ecosystems. The root cause proves simple: defaults remain permissive by design to maximize developer adoption.
Case A: Notification service built following the easy path used Twilio SDK boilerplate code directly. The critical miss involved complete lack of sender domain verification, enabling attackers to spoof legitimate numbers and systematically drain monthly quotas through fraudulent usage.
Risk Categories in Easy Paths
Permutation Risk: Easy CRUD interfaces handle basic create/read/update/delete operations smoothly. The miss involves missing permission combinations that enable guest users to delete records through classic IDOR Insecure Direct Object Reference vulnerabilities.
Scale Risk: Serverless platforms auto-scale functions automatically based on demand. The miss creates cost-based DDoS attack vectors where malicious invokers flood endpoints consuming massive compute budgets.
Abstraction Risk: Visual database rules appear simple and intuitive during development. The miss reveals logic holes where Role A unexpectedly reads Role B data through clever JOIN operations that bypass intended segregation.
Dependency Risk: Automatic npm/yarn package installation handles transitive dependencies seamlessly. The miss exposes supply chain compromise vectors where malicious packages infiltrate through trusted upstream dependencies.
Deep example: Easy e-commerce checkout implementation follows familiar patterns:
Easy path:
- Stripe Elements copy-paste integration for payments
- Firebase Functions webhook handler for events
- Deploy vercel --prod for instant production rollout
Code smells in easy webhook:
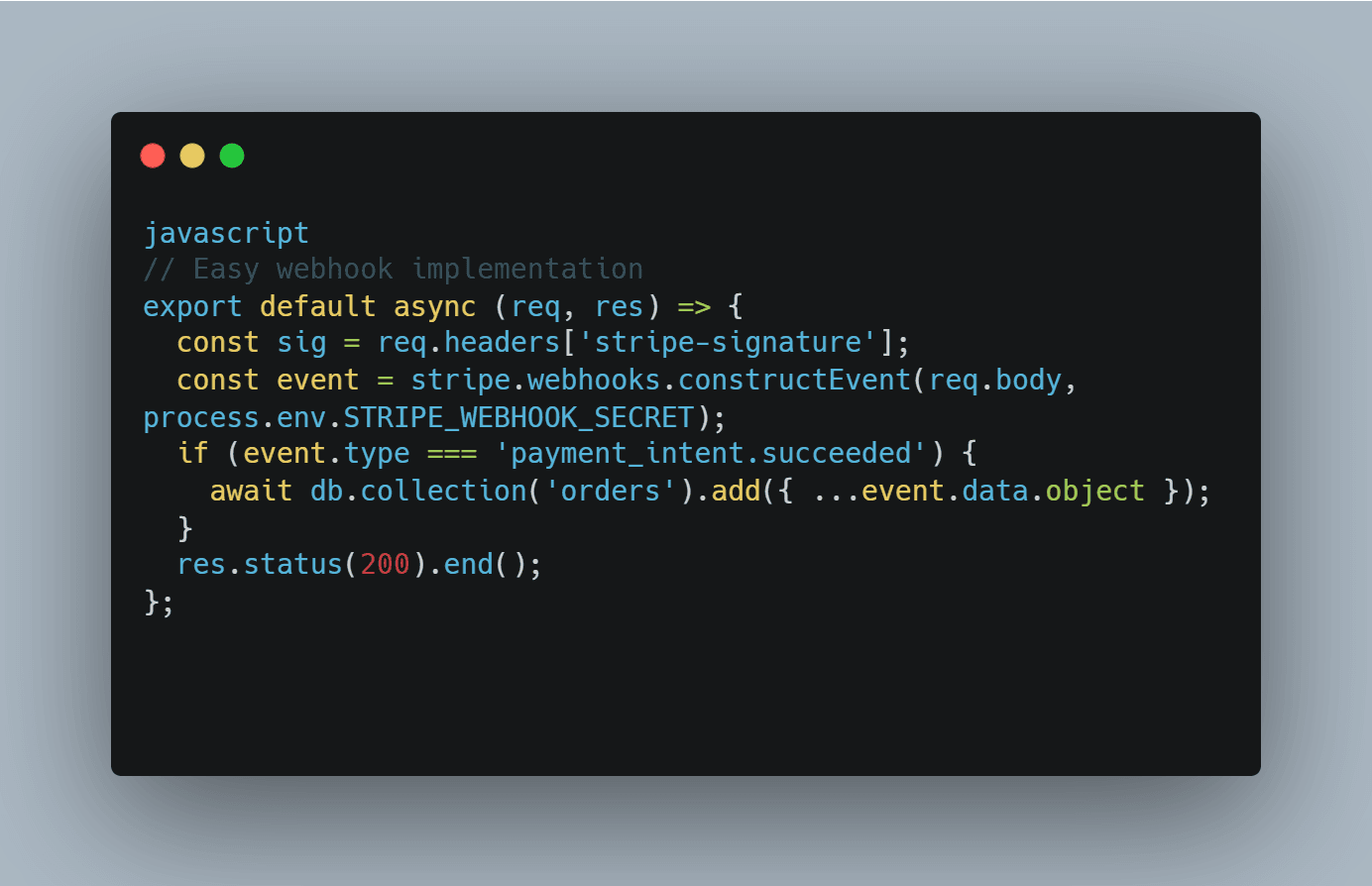
Risks missed completely:
- No signature verification timeout protection
- Database writes accept unvalidated payment amounts
- Environment secret rotation breaks webhook silently
- Production immediately hit with replay attacks double-charging customers
Case Studies: Easy Gone Wrong
Study 1: Lead Generation Landing Page. Easy implementation used Carrd form builder connected through Make.com workflows directly to Google Sheets. Critical miss involved forms accepting any email address without validation while sheets remained publicly accessible through shared links. Scrapers systematically filled sheets with junk data. Cost included complete quota exhaustion plus 20 hours manual cleanup.
Study 2: MVP Analytics Dashboard. Easy deployment used Plausible self-hosted analytics through simple Docker-compose up command. Critical miss exposed /api/keys endpoint without authentication protection. All API tokens became immediately visible to internet scanners. Cost included complete token revocation cascade plus re-authentication across 5k users simultaneously.
Study 3: Internal Chatbot Implementation. Easy Slack app connected directly to OpenAI Functions API. Critical miss allowed channel history queries for any user without authorization checks. Complete data exfiltration occurred silently. Cost included $50k compliance fine plus audit remediation.
Key pattern: Easy approaches deliver 80% of features through visual tools but ignore 20% plumbing critical for security. All risk concentrates in that ignored 20%.
Deliberate Paths: Ease + Risk Control
Balance requires calibrated friction intentionally reintroduced at critical gates. Three proven paths emerge:
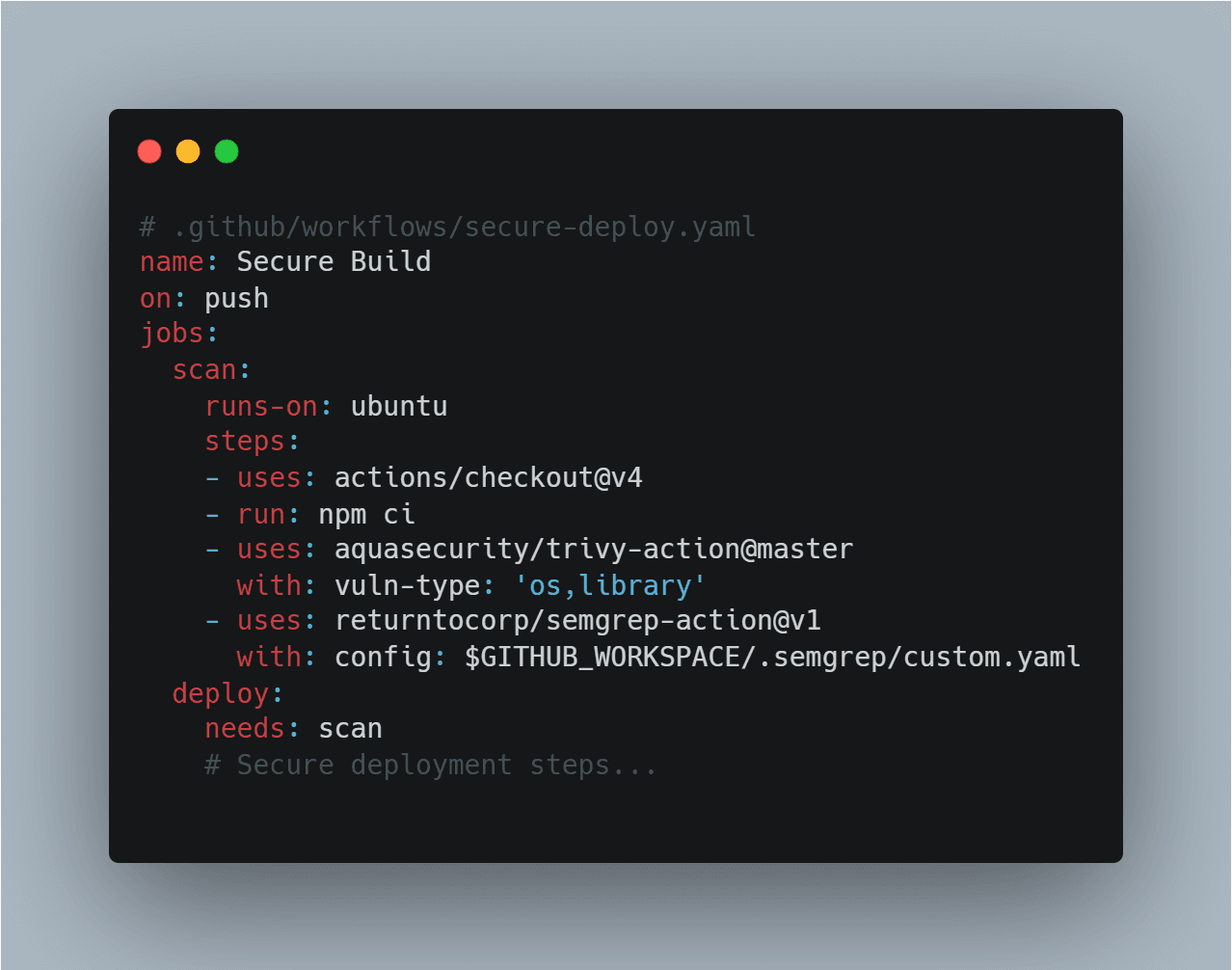
Path 1: Templated + Gates
Curate safe starter templates with security boundaries baked directly into Git repositories:
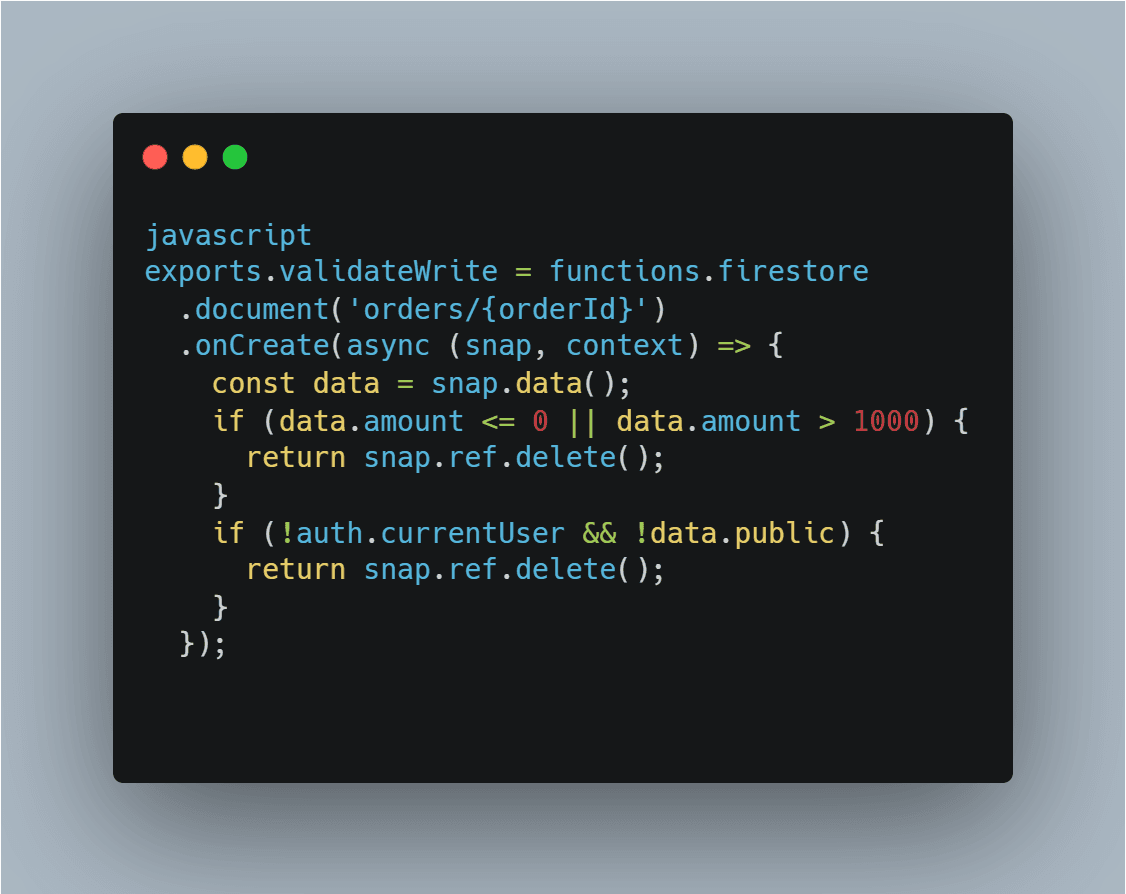
Path 2: Abstraction Wrappers
Easy visual platforms require thin code rims for protection. Firebase rules plus Cloud Functions validator pattern:
Path 3: Managed + Policies
Serverless deployments require gateway prefixes for control. AWS API Gateway + Lambda pattern includes Cognito authorizer with custom claims, strict usage plans limited to 1000 calls per month, and 10% canary deployments monitoring anomalies continuously.
Advanced Risk Patterns for Easy Stacks
Economic Risk: Easy metering configurations disabled by default enable attackers invoking 1M Lambda functions simultaneously. Bill shock arrives instantly. Mitigation includes budget alarms plus dead letter queues with throttling.
Temporal Risk: Secrets remain static across easy deployments. Rotation gets completely forgotten. Mitigation uses SSM Parameter Store with automatic TTL plus function re-fetching patterns.
Composability Risk: Easy Zapier-style chains propagate failures. One weak integration poisons entire workflows. Mitigation requires signed payloads between services plus 5-minute TTL enforcement.
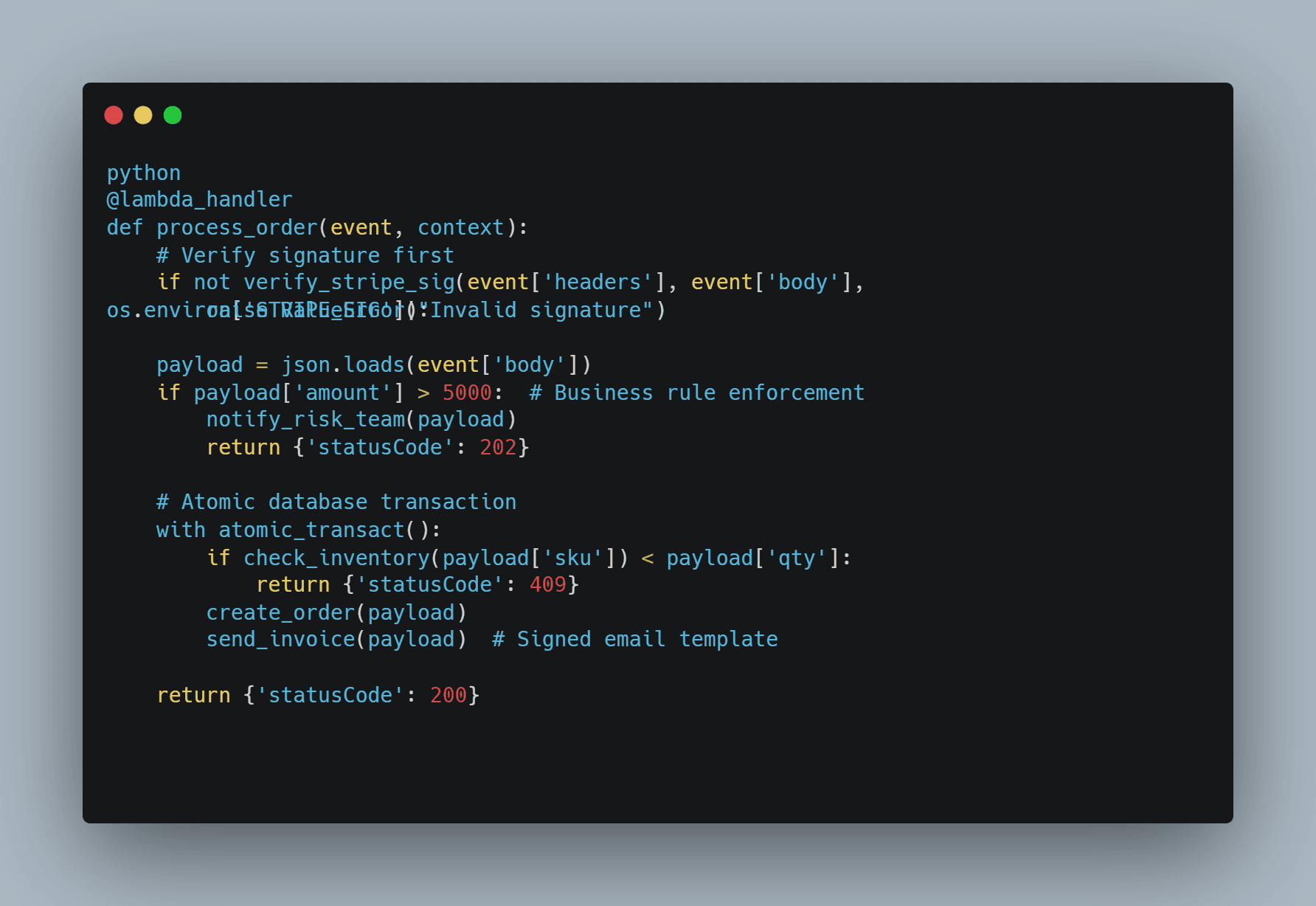
Deep mitigation example: Order processor combining Stripe payments plus SendGrid emails hardened properly:
Operational Risk Hygiene
Ease demands rigorous operational practices to compensate for missing security.
Shadow Deploy: Mirror production traffic patterns to canary environments catching issues pre-impact.
Synthetic Probes: Cron-scheduled fuzzing targets endpoints continuously simulating attacks.
Drift Detection: Weekly terraform plan --diff prevents configuration divergence silently.
Incident Postmortems: Root cause analysis required for every security alert regardless of impact.
Metrics suite:
- Risk score calculated as vulnerabilities open multiplied by severity weight
- Mean time to remediate MTTR breaches maintained under 4 hours maximum
- Cost variance constrained below 10% monthly threshold
Team ritual: Friday risk walkthrough sessions asking specifically "What easy corner did we cut this week?"
Scale story: Agency building 20 client applications per month using easy stacks implemented gates during week 1 onboarding. Zero production incidents recorded year-to-date across entire portfolio.
Cost math: Security gates consume 15% of total cycle time only. Saved 10x rebuild effort from avoiding breaches completely.
Reframed: Calibrated Friction Wins
Easiest builds tempt developers with irresistible velocity promises. Riskiest deliveries create maximum pain through predictable breach patterns. Infuse deliberate friction strategically through gates positioned immediately post-ease implementation. Features continue flying forward rapidly. Perimeters hold firm against attacks. Sustainable software tempers raw speed deliberately with comprehensive scrutiny.





