If you are a modern developer or a “vibe coder” moving at the speed of thought, your workflow in 2026 is likely all about agility. You spin up microservices, deploy fresh code, and connect complex architectures faster than ever before. Your application relies on APIs to stitch everything together, the frontend talking to the backend, mobile apps pulling data, and third-party integrations running smoothly in the background.
But in this race to ship features, we often leave things behind.
Old code versions, testing endpoints, and half-finished integrations get buried beneath new commits. You might assume that if an endpoint isn't documented or linked anywhere in your frontend, no one can find it. Unfortunately, hackers are counting on exactly that assumption.
Welcome to the hidden danger of shadow APIs, the invisible side doors into your application that hackers are quietly exploiting, completely bypassing your traditional defenses.
What Are Shadow APIs? (The Ghosts in Your Code)
To put it simply, shadow APIs are active, operational endpoints in your infrastructure that your IT and security teams don't know about. They are completely undocumented.
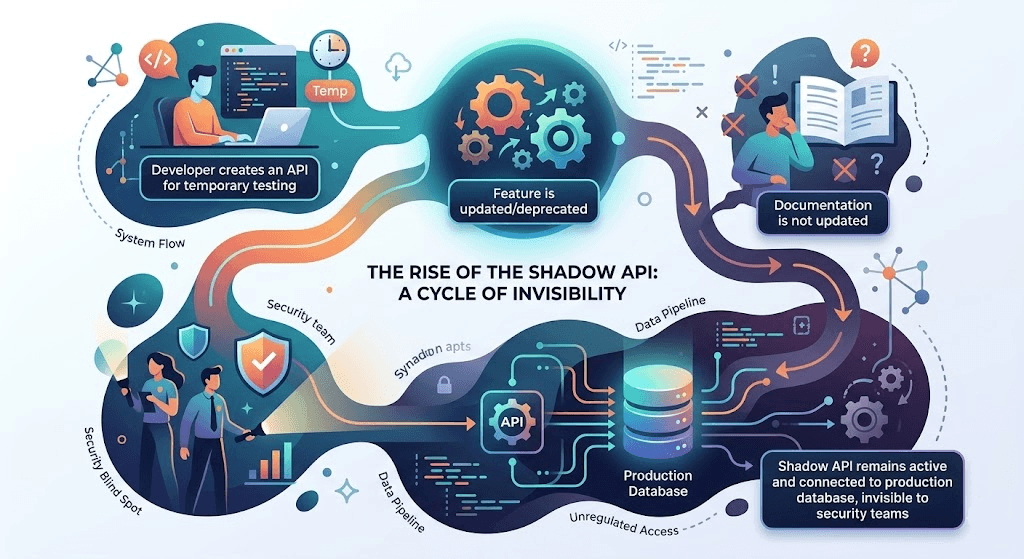
How do they happen? Nobody intentionally builds a shadow API. They are born out of rapid development and standard human error.
Common Sources of Undocumented Endpoints
- The “Version 1” Relic: You just migrated your app to api.myapp.com/v2/. It's faster, more secure, and perfectly documented. But api.myapp.com/v1/ was never actually turned off. It’s still connected to your production database, running outdated code with missing security patches.
- The Staging Leak: A developer creates a temporary endpoint to test a new payment gateway or bypass authentication for local testing (/api/test_auth_bypass). When the massive pull request gets merged into production, that testing endpoint accidentally goes with it.
- The Mobile App Leftovers: Mobile applications are notorious for communicating with hidden backend endpoints that developers assume users will never interact with directly.
Think of a shadow API like a hidden basement door in a highly secure fortress. You put a biometric lock on the front door, but you completely forgot the basement door exists, and its hinges are rusted open.
Why Traditional Security Misses Them (The WAF Bypass)
If you have a Web Application Firewall (WAF) in place, you might be thinking, “Shouldn't my WAF catch someone trying to hack an old API?”
The short answer is: no. This is where a devastating WAF bypass occurs.
WAFs are essentially digital bouncers looking for known bad behavior. They analyze incoming traffic for classic, recognizable attack signatures, things like malicious SQL code (SQL Injection) or malicious scripts (Cross-Site Scripting).
But a shadow API is a legitimate part of your application’s infrastructure. When a hacker discovers a shadow API, they don't necessarily need to throw a complex, messy exploit at it. Instead, they simply send normal-looking API requests.
If your forgotten /v1/users/export endpoint doesn't require an authentication token because it was an internal testing tool, the WAF will let the traffic right through. The WAF sees a standard GET or POST request that looks like perfectly normal web traffic. Because the WAF doesn't understand the business logic of your application, it just reads the packets, and the hacker walks right past the bouncer.
How Attackers Hunt for Undocumented Endpoints
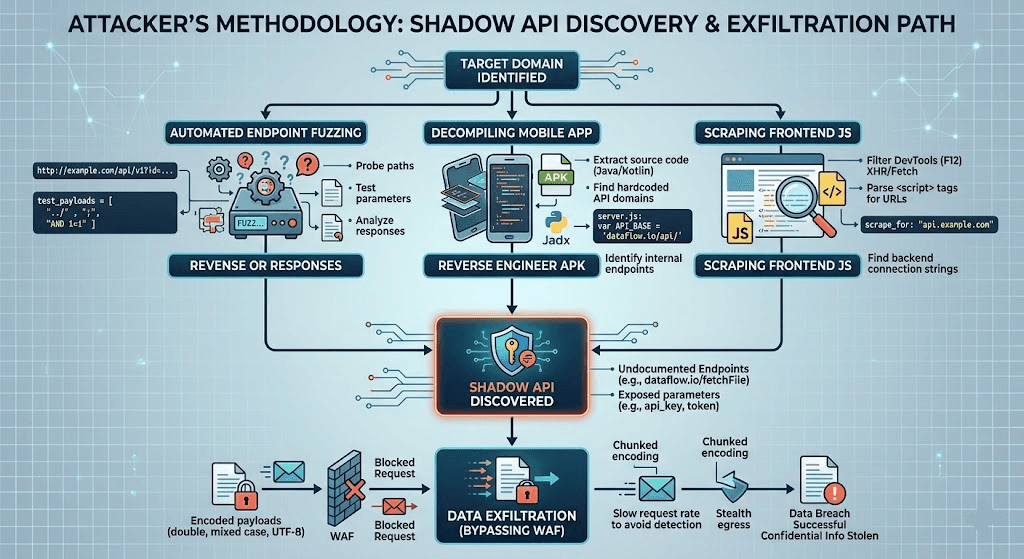
You might wonder how an attacker finds a shadow API if it isn't documented in your Swagger file or linked on your website. Attackers use sophisticated API discovery techniques to map out your infrastructure.
1. Fuzzing and Brute-Forcing
Hackers use automated scripts to rapidly guess thousands of potential directory names and endpoints. They will take your root domain (api.yourcompany.com) and throw dictionaries of common API names at it (/v1, /v2, /staging, /test, /admin, /users). Because shadow APIs often lack basic protections like rate-limiting—a common entry in the list of REST API vulnerabilities—the attacker can guess freely until they get a 200 OK response instead of a 404 Not Found.
2. Reverse Engineering Mobile Apps
If your company has a mobile app, it’s a goldmine for hackers. Attackers will download your Android APK or iOS app, decompile the code, and extract hardcoded API endpoints that the app uses to talk to your servers. Often, these endpoints are completely undocumented and lack the strict authentication required on your main web application.
3. Analyzing JavaScript Files
Even if an endpoint is no longer used, a reference to it might still exist in an old, minimized JavaScript file served to your users. Attackers scrape these files, pull out the URLs, and test them to see if they are still alive.
Defending the Unseen: Complete API Discovery and Security
You cannot protect what you cannot see.
Because shadow APIs are inherently unknown to your security team, traditional passive defenses are practically useless. Relying on manual code reviews is also a losing battle; modern codebases are simply too massive and change too frequently. To secure your infrastructure, you have to transition from passive defense to active discovery.
Implement Continuous API Discovery
Your first step in API security must be mapping your actual, living attack surface. This means deploying tools that analyze your network traffic and code repositories to build an automated, real-time inventory of every single API endpoint that is actively receiving traffic, not just the ones listed in your official documentation.
Embrace Active Vulnerability Scanning with Axeploit
Once you know where your endpoints are, you need to test them relentlessly. Static analysis (reading your code) is a good start, but it won't catch logic flaws in an active environment.
This is where the Axeploit API Security Checker becomes critical. By adopting a DevSecOps mindset and arming yourself with powerful, automated security tools like Axeploit, you can proactively find these forgotten doors. Our automated scanner actively tests your live, running application.
Instead of waiting for a breach, Axeploit safely attacks your app from the outside, exactly how a malicious hacker would. If you have a forgotten /v1 endpoint lingering in the background, or a REST API vulnerability allowing unauthorized access, Axeploit’s dynamic scanner will catch it, flag it, and show you exactly how to fix it before you go live.
Deprecate with Discipline
Finally, make API deprecation a core part of your developer culture. When you roll out a v2 endpoint, there must be a strict, calendar-driven deadline to sunset v1. Monitor traffic to the old endpoint, migrate any remaining internal services, and then physically tear down the route.
Conclusion: Shine a Light on Your Shadows
The era of the “vibe coder” means we are building incredible software at unprecedented speeds. But speed without visibility is a recipe for disaster. Shadow APIs are the quiet, ticking time bombs of modern web architecture. Because they bypass your WAF and evade manual review, they require a dedicated, active approach to API security.
You don't need to slow down your development cycle. You just need the right tools to illuminate the dark corners of your codebase by letting Axeploit discover and secure your APIs before the hackers do.





