If you are navigating the world of cryptocurrency in 2026, you already know that security is everything. You likely use hardware wallets, employ two-factor authentication, and double-check every transaction address. But what if the very tool you use to organize your thoughts, draft your strategies, or store your notes is quietly holding the door open for cybercriminals?
Recently, cybersecurity researchers uncovered a highly sophisticated, completely novel attack method targeting individuals in the financial and cryptocurrency sectors. Instead of relying on traditional email attachments or shady download links, hackers are now abusing Obsidian, a popular, widely trusted note-taking application. They are using it to deliver a vicious piece of malware known as the PhantomPulse RAT.
If the terms "RAT" or "Obsidian plugins" sound like a foreign language to you, don't worry. In this guide, we are going to break down exactly what this attack is, how these modern digital heists work, and, most importantly, how you can bulletproof your digital life against them.
What is Obsidian, and Why Are Hackers Using It?
To understand the attack, you first need to understand the tool. Obsidian is a powerful, cross-platform note-taking app. Millions of people use it as a "second brain" to store their ideas, write journals, or collaborate on projects. It organizes notes into a localized folder known as a "Vault."
One of Obsidian’s best features is its community plugins, mini-applications created by other users that add new features to your notes. Think of plugins like browser extensions; they are highly useful but possess deep access to the application itself.
Hackers realized that because Obsidian is a trusted, highly reputable application, antivirus software often ignores what happens inside it. By hiding malicious code inside a shared Obsidian Vault and exploiting legitimate plugins, attackers can bypass traditional security alarms entirely.
The PhantomPulse RAT: A Ghost in Your Machine
In this latest campaign (dubbed REF6598 by security experts), the end goal of the hackers is to install the PhantomPulse RAT.
But what exactly is a RAT? It stands for Remote Access Trojan. In simple terms, it is a hidden digital backdoor. Once it is on your computer, the hacker has the keys to your house. They can record your keystrokes (stealing your passwords), take screenshots of your crypto wallets, inject malicious code, and securely send all your private data back to their own servers.
What makes PhantomPulse terrifyingly modern in 2026 is that it is AI-generated and uses the Ethereum blockchain to communicate. Instead of using a standard, easily blockable web address to receive commands from the hacker, PhantomPulse searches for a specific Ethereum wallet address and reads the blockchain transaction history to find its instructions. This makes it incredibly difficult for security researchers to track or take down.
How the Attack Unfolds: A Step-by-Step Breakdown
Hackers don't just hack systems anymore; they hack human psychology. This attack doesn't start with a virus alert; it starts with a friendly chat.
Here is a visual flowchart of how this sophisticated attack works:
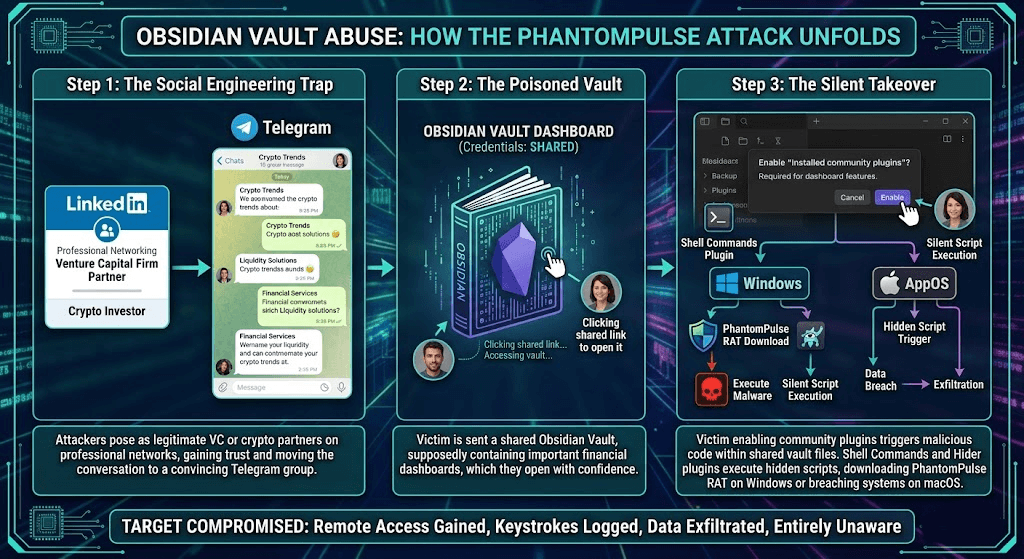
Step 1: The Social Engineering Trap
The attackers approach a target on LinkedIn, posing as a prominent venture capital firm or a cryptocurrency liquidity partner. After gaining the target's trust through professional networking, the conversation is moved to a Telegram group. To make it look legitimate, the group is filled with fake "partners" discussing complex financial services and crypto trends.
Step 2: The Poisoned Vault
Once the victim feels comfortable, the "investors" share an Obsidian Vault, claiming it contains a shared dashboard of important financial documents or investment strategies. The victim opens the vault using the credentials provided.
Step 3: The Silent Takeover
The moment the victim opens the shared vault, Obsidian throws up a prompt asking them to enable "Installed community plugins" so the dashboard can load properly.
Because the victim trusts the fake investors, they click Enable.
Instantly, two specific plugins, Shell Commands and Hider go to work. The Hider plugin covers up user interface elements so the victim doesn't see anything suspicious. Meanwhile, the Shell Commands plugin silently runs a script in the background. On Windows, it downloads and launches PhantomPulse. On Macs, it triggers a different hidden script to breach the system. The trap is sprung, and the victim is entirely unaware.
How to Stay Safe: A Step-by-Step Guide to Bulletproof Your System
The scary part of the PhantomPulse attack is that it doesn't rely on broken software—it relies on the software working exactly as intended, just in the wrong hands. Detecting and stopping these modern AI-driven malware requires strict personal vigilance and the right automated tools.
Here is your step-by-step guide to staying safe:
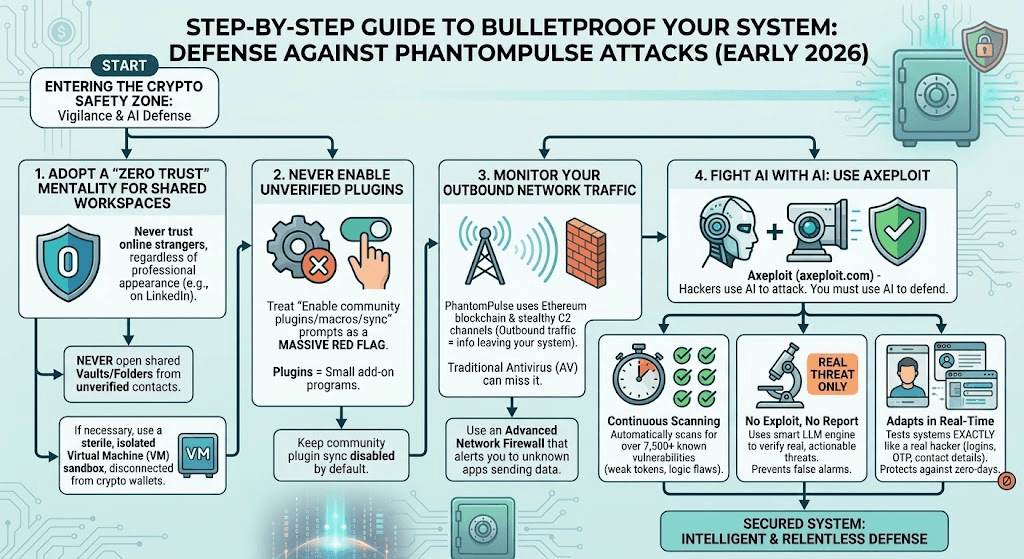
1. Adopt a "Zero Trust" Mentality for Shared Workspaces
Never open a shared workspace, cloud folder, or Obsidian Vault from someone you have only met online, no matter how professional their LinkedIn profile looks. If you must open a shared file, use a sterile, isolated environment (like a Virtual Machine) that isn't connected to your main crypto wallets.
2. Never Enable Unverified Plugins
If an application asks you to enable "Community Plugins," "Macros," or "Sync features" to view a document, treat it as a massive red flag. Keep community plugin sync disabled by default.
3. Monitor Your Outbound Network Traffic
Since PhantomPulse communicates through the Ethereum blockchain and uses stealthy C2 (Command and Control) channels, traditional antivirus might miss it. Use a network firewall tool that alerts you when unknown applications try to send data out to the internet.
4. Fight AI with AI: Use Advanced Vulnerability Scanners like Axeploit
As hackers use AI to write malware and automate attacks, manual security checks are no longer enough. If you are building crypto applications or running web platforms, you must secure your own infrastructure. This is where Axeploit becomes essential.
Axeploit is a zero-configuration, AI-powered vulnerability scanner that acts like an autonomous cybersecurity agent.
- Continuous Scanning: Axeploit automatically scans for over 7,500+ known vulnerabilities, testing everything from weak authentication tokens to advanced business logic flaws.
- No Exploit, No Report: Unlike older tools that bombard you with false alarms, Axeploit uses a smart LLM engine to verify threats. As highlighted on their blog, their philosophy ensures that if a vulnerability is reported, it is a real, verified threat.
- Adapts in Real-Time: Axeploit operates with real contact details, independent logins, and OTP verifications to test your systems exactly how a real hacker would, ensuring your endpoints are not an easy target for attackers leveraging the latest zero-days.
By integrating automated defense mechanisms like Axeploit, you ensure that your security posture is just as intelligent and relentless as the hackers trying to breach it.
Conclusion
The PhantomPulse RAT campaign is a harsh reminder of how cybersecurity is evolving in 2026. Attackers are moving away from traditional hacking and heavily leaning into social engineering, using the trusted apps we rely on every day against us.
By understanding the mechanics of how these attacks happen, from the initial LinkedIn message to the hidden Obsidian plugin, you strip the hackers of their greatest weapon: the element of surprise. Keep your guard up, strictly monitor what permissions you grant to your applications, and rely on modern, AI-driven security tools to keep your digital vaults locked tight. In the fast-paced world of cryptocurrency, a healthy dose of skepticism is your best investment.





