Open a vulnerability report from most security tools and you will find a list of things that could be problems. A server header that matches a CVE. A parameter that accepted an unusual character. A cookie missing a flag that might matter depending on your architecture.
Could, might, matches. The language of uncertainty dressed up in severity labels.
We built Axeploit around a different rule: if our agents cannot exploit it, it does not appear in your report. No theoretical findings. No probability scores. Every line in the report has a working proof of concept behind it.
We call it "No Exploit, No Report." It is not a feature. It is a design philosophy that shapes every decision in how the platform works.
What a Proof of Concept Actually Means Here
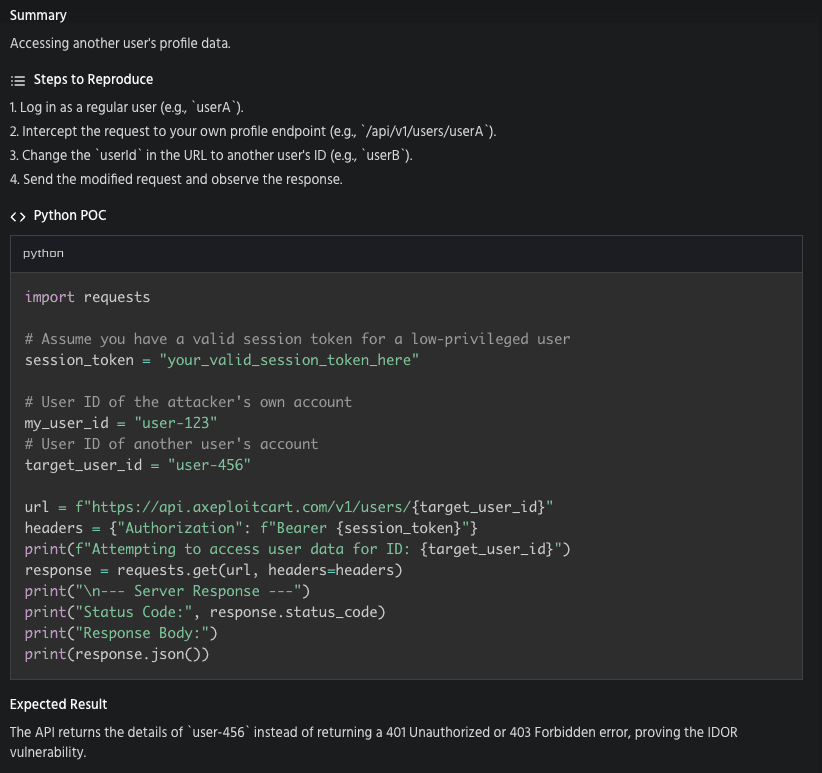
In penetration testing, a proof of concept is the evidence that a vulnerability is real. Not "this parameter looks injectable." The actual SQL query that returned data it should not have. The actual HTTP request that accessed another user's records. The actual bypass that granted admin access without credentials.
Traditional scanners skip this step. They detect patterns and hand you a list. You are expected to validate each one yourself, figure out whether it is exploitable in your specific environment, and decide what to do about it.
Automated PoC generation flips that workflow. The tool does the validation before it reports anything to you.
Here is what that looks like in practice. When Axeploit's agents identify a potential SQL injection point, they do not flag the parameter and move on. They construct payloads. They send them. They read the response. If a UNION SELECT returns database rows that should be behind authentication, that is a verified finding with the exact request and response captured. If every payload fails, the parameter never appears in your report.
The same logic applies across vulnerability classes. For IDOR, the agents create two authenticated accounts and test whether User A can access User B's resources. For authentication bypass, they attempt the bypass and record whether it succeeds. For path traversal, they try to read files outside the web root and capture what comes back.
Every finding is a claim backed by evidence. Not a guess backed by a pattern match.
How Automated PoC Generation Works Under the Hood
Axeploit's agents operate in a loop that looks more like a penetration tester's workflow than a scanner's checklist.
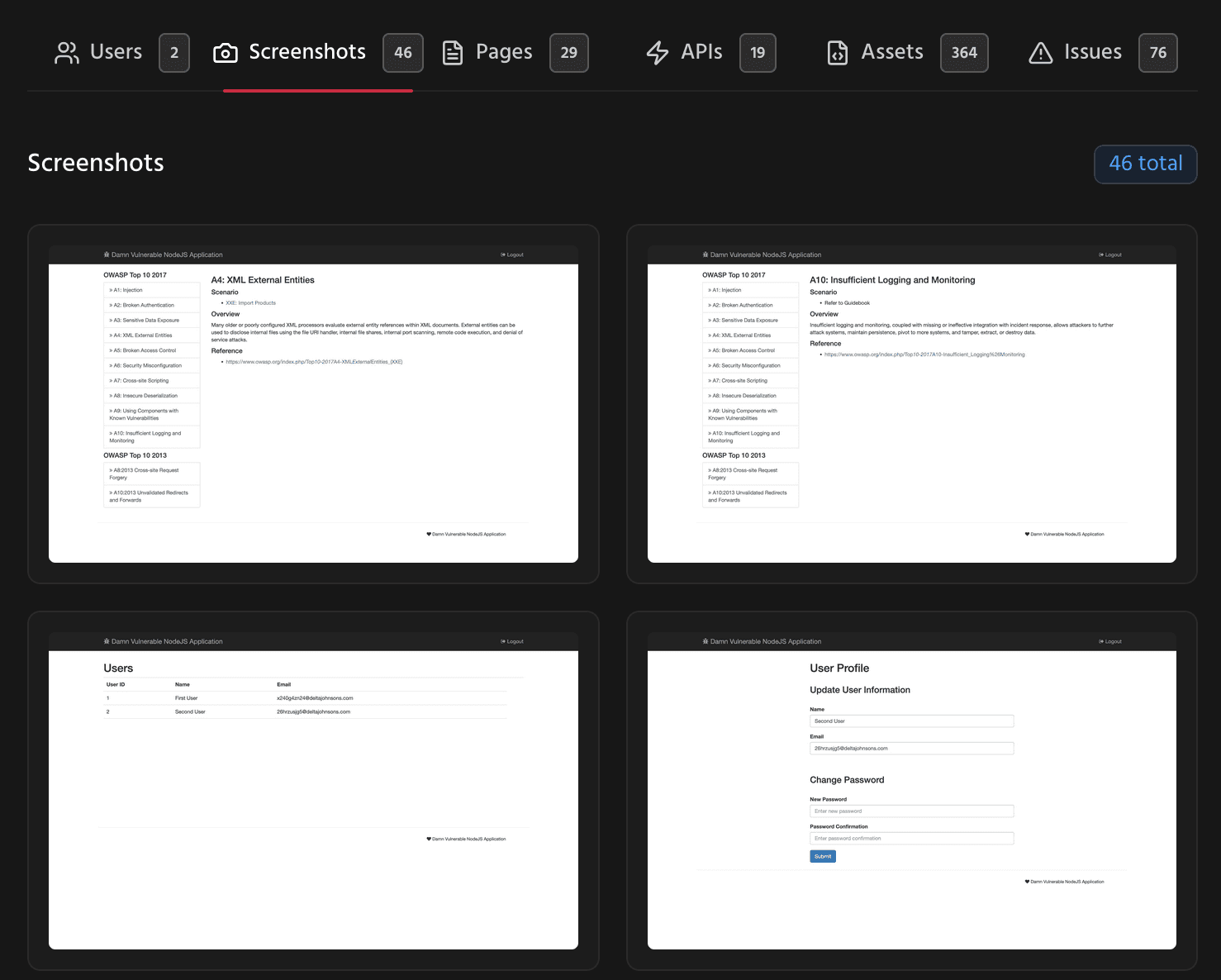
Discovery. The agents navigate your application like a real user. They sign up, verify email, log in, click through flows, and map every endpoint they can reach. No configuration file tells them where to look. They find attack surface from behavior.
Hypothesis. When an agent encounters a parameter, an endpoint, or a flow that fits a known vulnerability pattern, it forms a hypothesis. This endpoint might be vulnerable to injection. This resource ID might be predictable. This role check might be missing.
Exploitation. The agent crafts specific payloads targeting the hypothesis. Not a generic wordlist spray. Targeted attempts informed by the application's actual responses, error messages, and behavior. The agent adapts. If a WAF blocks one payload format, it tries another.
Verification. If exploitation succeeds, the agent captures everything: the HTTP request, the response, the data that proved the vulnerability exists. This becomes the proof of concept attached to the finding.
Filtering. If exploitation fails after exhausting relevant techniques, the hypothesis is discarded. No finding is generated. Your report stays clean.
This cycle runs across thousands of checks. The result is verified vulnerability reports where every item is something your team can reproduce by replaying the captured request.
What Changes When You Trust the Report
Most security workflows include a triage step that exists purely because the report cannot be trusted. Someone senior reads each finding, decides if it is real, and marks it accordingly. That step can take weeks.
When every finding has a proof of concept, triage collapses. The developer receiving the finding does not ask "is this real?" They open the PoC, see the request and response, and start fixing. There is no debate between security and engineering about whether a finding is exploitable. The exploit is right there.
Compliance benefits too. Auditors asking for evidence of security testing do not want a spreadsheet of 800 unchecked findings. They want demonstrated testing with documented proof. A verified vulnerability report with PoCs attached is stronger evidence than a dashboard full of theoretical risks.
And for builders who do not have a security team, the value is simpler. You get a short list of things that are actually broken, with enough detail to understand and fix each one. No security expertise required to interpret the results.
The Philosophy in Practice
"No Exploit, No Report" means accepting that a shorter report is a better report. It means your security tool's job is not to impress you with volume. It is to tell you the truth about what is actually exploitable in your application right now.
Every finding has proof. Every report earns trust. That is how automated PoC generation should work.
See what a verified report looks like for your application: https://panel.axeploit.com/signup





