If you are a startup founder, a business owner, or a “vibe coder,” you probably love automation. Tools like n8n have become the absolute backbone of the modern AI-integrated business. They let you connect APIs, string together AI models, and automate hours of manual labor in just a few clicks. It feels like magic.
But here is the hard truth of early 2026: the same tools that are saving you hours of work are now being used by cybercriminals to bypass your security systems.
Since October 2025, cybersecurity researchers at Cisco Talos have been tracking a disturbing trend. Hackers are actively abusing n8n webhooks to deliver dangerous malware and silently track users through phishing emails. And because n8n is a highly trusted platform, these attacks are slipping right past traditional spam filters and firewalls.
If you are running an AI-driven startup or integrating automated workflows into your business, this is not a technical glitch you can ignore. It is a direct threat to your infrastructure. Let's break down exactly how the attack works, and what you can do to protect your systems.
Why Automation is a Double-Edged Sword for Founders and Vibe Coders
When you set up an account on n8n's managed cloud service, the platform gives you a custom, legitimate-looking web address (something like yourstartup.app.n8n.cloud). Because this domain belongs to n8n, a trusted, legitimate software provider, email filters from Google, Microsoft, and corporate firewalls usually wave it right through.
Hackers realized that if they build their malicious systems on top of n8n, they get to borrow n8n’s excellent reputation.
What Exactly is an n8n Webhook?
Think of an API as a drive-through window: you ask for something, and the window hands it back. A webhook is the exact opposite; it’s like a delivery driver bringing the food directly to your door the moment it is ready. In technical terms, it is a “reverse API.”
In n8n, webhooks are essentially custom URLs waiting to receive data. When that URL gets a ping (like someone clicking a link), it triggers a workflow. If a hacker sends you that URL in an email and you click it, your web browser acts as the receiving application. The workflow triggers, and the hacker’s automated sequence begins.
The Attack Breakdown: How Hackers Use n8n to Sneak Past Security
According to the threat intelligence gathered up to early 2026, the volume of these malicious n8n emails spiked by a staggering 686% between January 2025 and March 2026. Attackers are primarily using two stealthy methods to compromise your networks.
Tactic 1: The “Trusted” Malware Delivery
This is the most common and dangerous attack. Here is how it plays out:
- The Bait: You receive an email that looks like a perfectly normal business request. It might claim to be a shared document from a colleague or a partner. The link inside the email points to an n8n webhook URL.
- The Illusion: Because the link goes to a .app.n8n.cloud domain, your email security software thinks, “Oh, this is just a trusted automation platform,” and lets it into your inbox.
- The Trap: You click the link. Instead of a document, you are taken to a web page displaying a standard CAPTCHA screen. This is a brilliant psychological trick, CAPTCHAs make us feel safe and secure.
- The Execution: The moment you solve the CAPTCHA, a hidden JavaScript code triggers the download of a malicious payload (an executable file or an MSI installer). Because this process happens entirely within the browser via n8n's domain, it looks completely legitimate to your computer's built-in defenses.
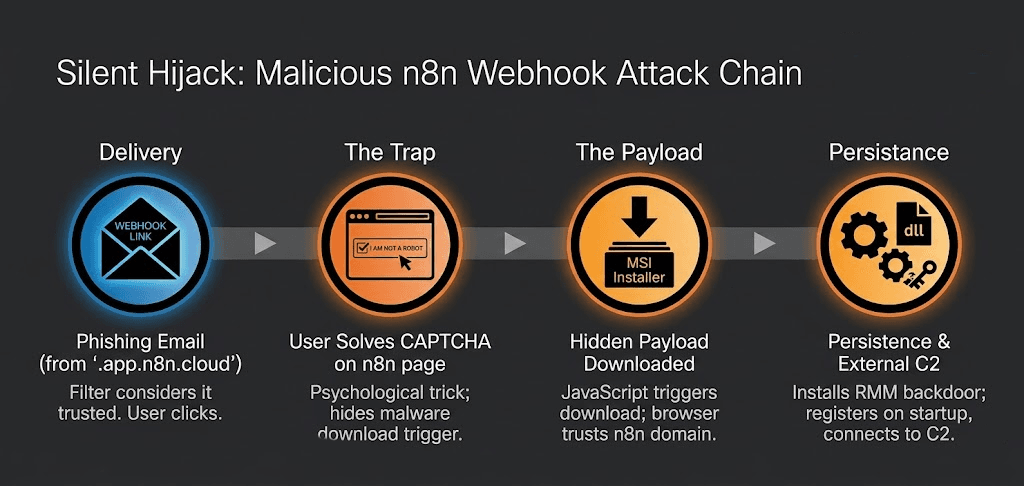
Once downloaded, the malware installs modified versions of legitimate remote IT management tools. Suddenly, hackers have a persistent, invisible backdoor into your system, allowing them to steal data or launch ransomware.
Tactic 2: Invisible Device Fingerprinting
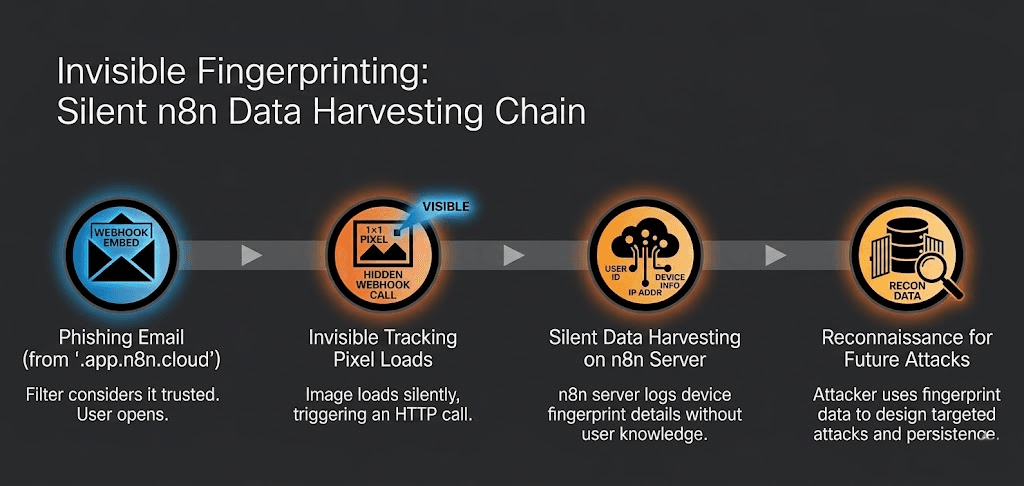
Not all attacks are trying to install malware immediately. Sometimes, hackers just want to map out your network.
In this tactic, hackers embed an invisible tracking pixel, a tiny 1x1 image into an email. That image is hosted on an n8n webhook. The second you open the email, the image loads. When it loads, it silently sends a request back to the hacker's n8n server, carrying your email address, your IP address, and details about your device.
This “fingerprinting” tells the hacker that your email is active, what kind of software you run, and exactly how to target you with a more sophisticated attack later.
Why Your Current Security Might Miss This
If you are a founder or a vibe coder, you likely rely on standard out-of-the-box security: basic email spam filters, default cloud settings, and whatever antivirus comes with your operating system.
But these legacy tools look for known bad things like shady domains or previously recognized virus signatures. They are not designed to catch hackers hiding inside known good things, like n8n workflows. Furthermore, testing your own systems for complex authentication and business logic flaws requires a deep understanding of cybersecurity. That is something most fast-moving startup teams simply do not have the time or resources for.
You need a security system that thinks like an AI and acts like a hacker.
Using AI-Powered Defense for Modern AI Workflows
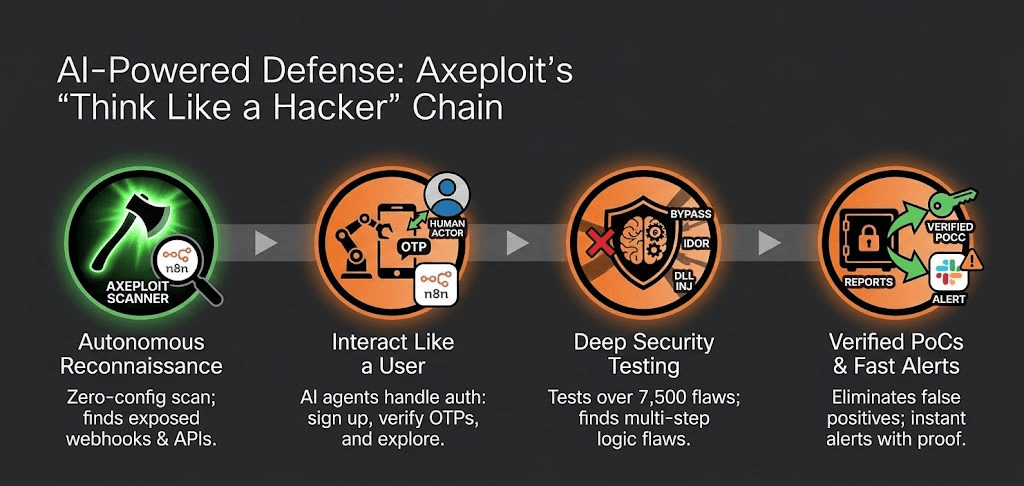
If hackers are using AI and automation to attack you, you need to use AI and automation to defend yourself. This is where Axeploit steps in.
Axeploit is a zero-config, AI-powered vulnerability scanner specifically built for the modern, fast-paced development era. Unlike clunky legacy security tools that require you to manually hand over user credentials or map out every single API integration, Axeploit handles everything autonomously.
Why Axeploit is the Perfect Fit for Vibe Coders and Founders
- It Acts Like a Real Human: Axeploit doesn’t just blindly scan your code; it interacts with your application. It signs up for your platform using a real mobile number and email address, receives OTPs (One Time Passwords), verifies its account, and logs in, just like a legitimate user. From there, it safely explores your application to find where the digital doors are left unlocked.
- Discovers Over 7,500 Vulnerabilities: Whether it is an authentication bypass, an IDOR (Insecure Direct Object Reference), or vulnerabilities linked to third-party integrations (like a poorly secured webhook), Axeploit’s massive database covers it. It continuously updates with the latest CVEs, empowering you to defend against zero-day threats.
- Catches What Legacy Tools Miss: Authentication flaws cause over 30% of all vulnerabilities. Traditional tools struggle here because they need you to record specific sessions. Axeploit’s powerful Large Language Model (LLM) engine automates authentication checks, easily identifying issues in email verification, weak tokens, and rogue APIs you might have forgotten you even exposed.
The 'No Setup, No Headaches' Approach of AI Threat Detection
When building at the speed of thought, there is no time to configure complex security software. Axeploit embodies a “no setup, no headaches” philosophy. You simply point the AI at your web application, and it figures out the rest. Its layout-aware intelligence adapts in real-time to front-end changes, so a UI update won't break your security scans. Plus, you get real-time alerts sent straight to your Slack channel the moment it flags a vulnerability.
Conclusion: Automate Safely, Secure Vigorously
The revelation that n8n webhooks are being actively abused by cybercriminals is a massive wake-up call for the AI ecosystem. We are no longer living in an era where hackers rely solely on poorly written code or obvious Nigerian Prince scams. They are hijacking the very automation platforms that run our modern businesses.
As a founder or a vibe coder, your superpower is speed. You shouldn't have to slow down your AI integrations out of fear. By understanding how these attacks happen like the fake CAPTCHAs and invisible tracking pixels, you are already one step ahead.
By integrating intelligent, autonomous security platforms like Axeploit into your workflow, you ensure that while your business scales effortlessly, your defenses scale with it. Keep building, keep automating, but make sure your digital doors are firmly locked.





