We’ve all heard the advice: “Enable MFA (Multi-Factor Authentication) to stay safe.” It’s the digital equivalent of adding a deadbolt to your front door. You enter your password (the first lock), and then you get a code on your phone (the second lock). For years, this was enough to keep 99% of hackers out.
But it’s early 2026, and the digital landscape has shifted. Hackers aren't just trying to pick your locks anymore; they are focused on stealing the actual keys while you’re using them. According to recent security trends, when an attacker already has your “session keys,” that fancy MFA isn't a barrier but it’s just another door they’ve already found the key for.
In this guide, we’re going to break down how these modern attacks work and, more importantly, how you can use advanced tools like Axeploit to ensure your system isn't the next one to fall.
The Illusion of the “Second Lock”
To understand why MFA is failing, we first need to understand what hackers are actually after. They don’t necessarily want your password. They want your Session Token.
Imagine you walk into a high-security building. You show your ID at the front desk (MFA), and they give you a “Guest Badge” (the Session Token). As long as you are wearing that badge, you can walk through any door in the building without showing your ID again.
If a thief steals your ID, they still have to pass the front desk. But if they steal your Guest Badge, they can bypass the front desk entirely and walk right in. In 2026, hackers perfected the art of “Badge Snatching” through a method called Adversary-in-the-Middle (AiTM).
What is an Adversary-in-the-Middle (AiTM) Attack?
In simple terms, an AiTM attack is like a “fake mirror.”
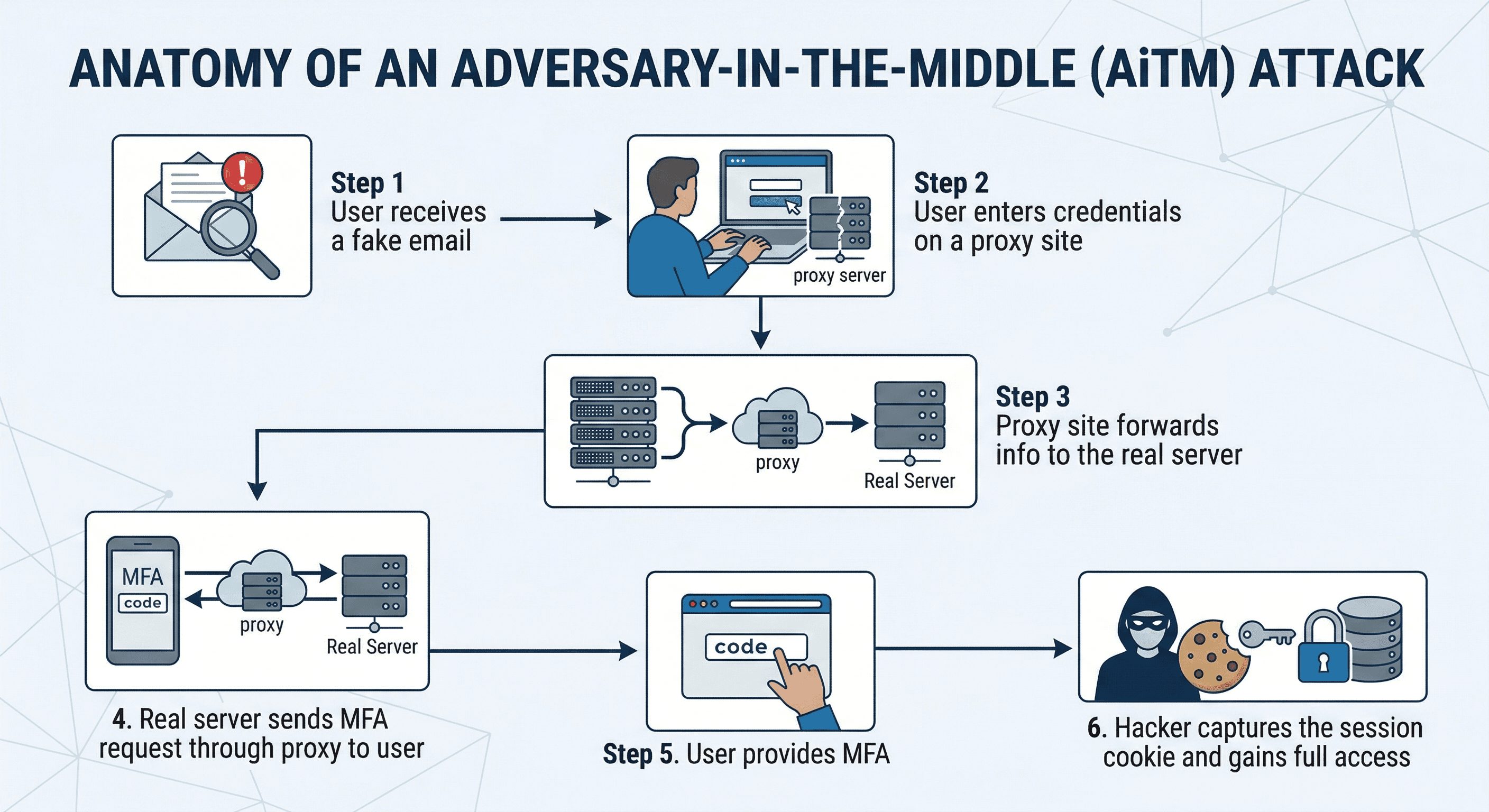
- A hacker sends you a phishing email that looks exactly like a login page for Microsoft, Google, or your bank.
- When you enter your password on the fake site, the hacker’s server passes that information to the real site in real-time.
- The real site asks for your MFA code. You enter it into the hacker’s fake site.
- The hacker passes that code to the real site.
- The real site logs the hacker in and issues a session token (the Guest Badge).
- The hacker steals that badge, and now they are “you” for as long as that session lasts.
Why Traditional Defense is Falling Behind
The problem with traditional security is that it’s often “static.” It looks for things that are already known to be bad. But in 2026, attackers are using AI-driven automation to create unique, one-of-a-kind phishing sites that don't appear on any “bad list” yet.
Furthermore, many businesses have “blind spots.” They might secure their main login page but forget about a secondary API or a sub-domain that doesn't require the same level of MFA. Hackers love these “side doors.” Once they get in through a weak point, they can move sideways through your network until they find the “keys to the kingdom.”
The Rise of Session Hijacking
Once a hacker has your session token, they don't need your password or your phone. They can bypass MFA because the system thinks the “multi-factor” part has already happened. This is why we are seeing a massive spike in corporate account takeovers, even in companies that pride themselves on having 100% MFA adoption.
How to Fight Back: Proactive Security with Axeploit
If hackers are using AI and automation to find your weaknesses, you need a tool that does the same to protect you. This is where Axeploit comes in.
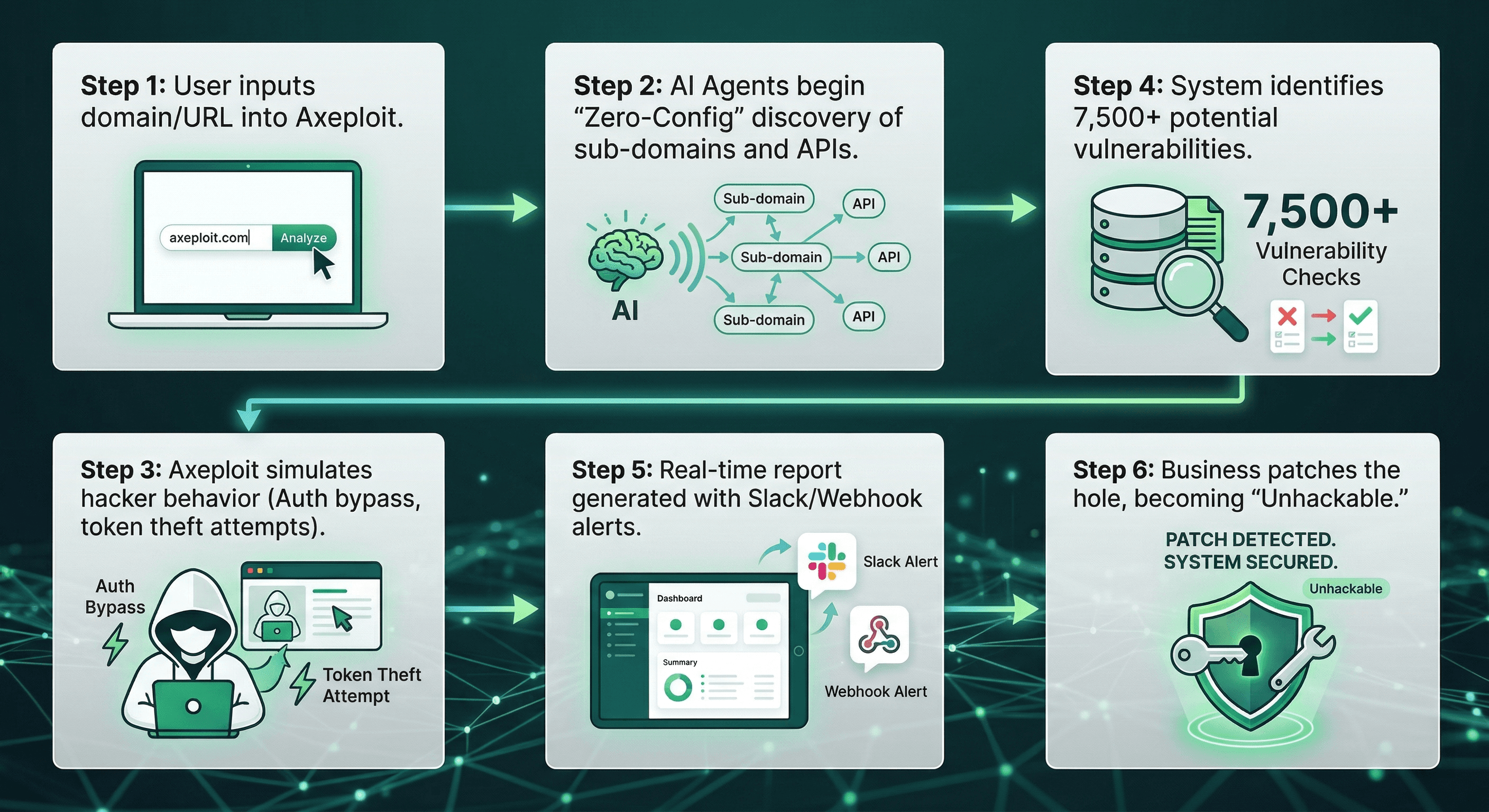
Axeploit is a next-generation, zero-config vulnerability scanner that identifies the exact holes hackers use to steal your “keys.” While most tools just tell you that your password is weak, Axeploit looks at the entire structure of your network and applications to find the “side doors” hackers love.
Why Axeploit is Essential for 2026 Security
Unlike older scanners that require a team of experts to set up, Axeploit is built for the modern, fast-paced world. Here is how it helps you detect and prevent the theft of your digital keys:
- 7,500+ Vulnerability Checks: It doesn’t just look for one thing. It scans for thousands of known flaws, including those that allow hackers to bypass authentication or steal session tokens.
- AI-Driven Agents: Axeploit uses specialized AI agents that “think” like a hacker. They can navigate through your website, sign up for accounts, and even solve mobile OTP (One-Time Password) challenges to see if your system can be tricked.
- Sub-Domain & API Scanning: As we mentioned, hackers love side doors. Axeploit automatically finds your sub-domains and hidden APIs, ensuring every single entrance to your digital house is locked tight.
- Business Logic Flaw Detection: Sometimes, a system isn't “broken,” but its logic is flawed. For example, if a user can see another user’s data just by changing a number in the URL (an IDOR attack), Axeploit will find it and alert you before a hacker does.
How to Stay Safe: A 2026 Checklist
Beyond using a powerful tool like Axeploit, here are the steps every user and business should take:
- Use Token-Based MFA: Move away from SMS-based codes. Use physical security keys (like YubiKeys) or “Passkeys.” These are much harder for AiTM attacks to intercept.
- Shorten Session Durations: Don't let "Guest Badges" last for weeks. Force users to re-authenticate more frequently, especially when accessing sensitive data.
- Monitor for Unusual Logins: If “you” log in from New York and then again from London five minutes later, your system should automatically kill that session.
- Run Regular Scans: Security isn't a “one and don” task. Use Axeploit to run continuous scans so you catch new vulnerabilities (Zero-Days) the moment they appear.
Conclusion: Don't Just Lock the Door Instead Watch the Keys
Multi-Factor Authentication is still a vital part of your security, but it is no longer a magic shield. In 2026, the battle moved from the “lock” to the “key.” Hackers are smarter, faster, and more automated than ever before.
By understanding that MFA can be bypassed through session theft and AiTM attacks, you’ve already taken the first step in protecting yourself. The second step is moving from a "reactive" mindset to a “proactive” one. Tools like Axeploit give you the upper hand by finding your weaknesses before the hackers do.
Don't wait for your keys to be stolen. Secure your network, identify your flaws, and stay one step ahead of the shadows. With Axeploit, see where your side doors are and start your zero-config vulnerability scan today.





