You are not slow. You are not waiting for a security team to green-light your release. You are shipping features while the idea still feels fresh, and that is exactly how products get traction.
The uncomfortable part is this: the same speed that gets you users also gets you holes. Auth flows that looked fine in the demo break under pressure. An endpoint your AI scaffolded never made it into the "official" API list, but it is live on the internet anyway. You are not careless. You are just moving faster than traditional security workflows were built for.
That gap is why we built Axeploit.
What Axeploit Is
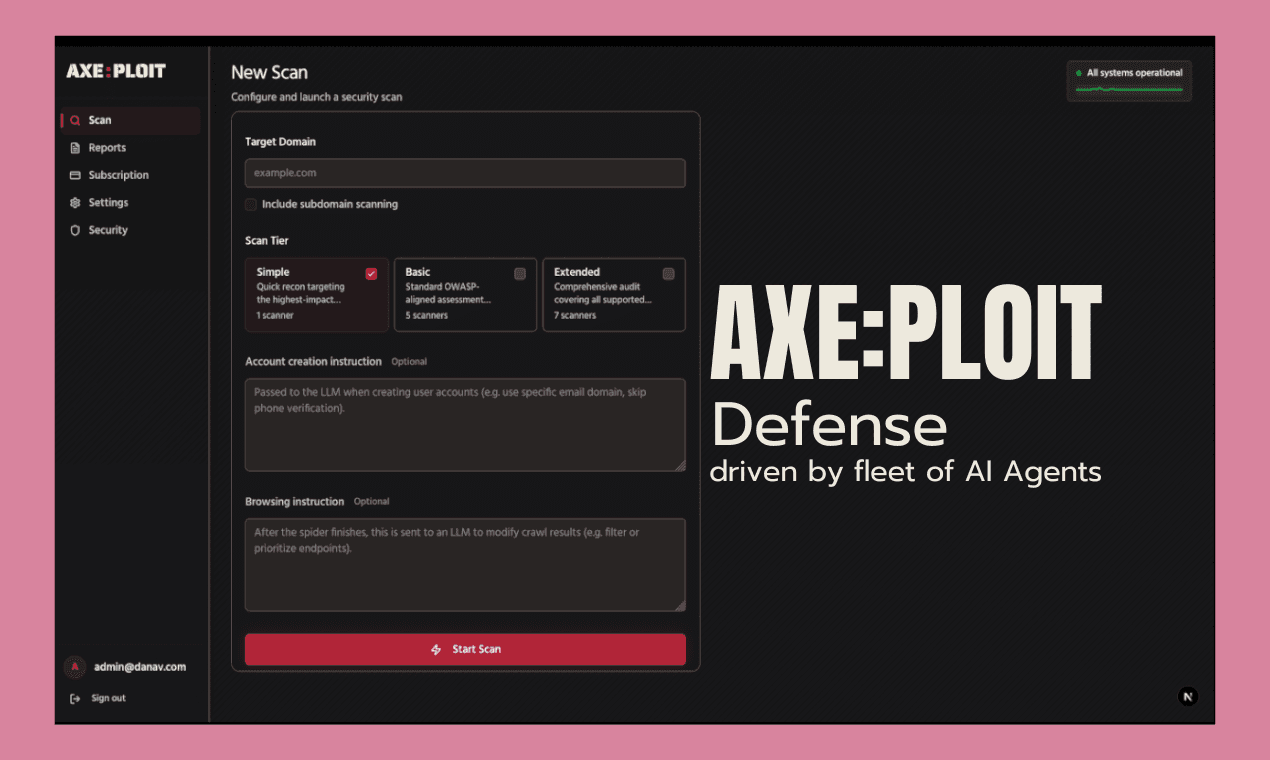
Axeploit is defense driven by a fleet of AI agents. You give us a URL. Our agents use your product the way a motivated attacker would: they sign up, they log in, they click through flows, they map what is actually exposed, and they run thousands of checks against what they find.
No YAML to write. No crawl rules to tune. No week-long onboarding call where someone asks for your architecture diagram. If it is reachable from that URL, it is in scope for the test.
We built it around a simple belief: security is a fundamental right, not a privilege. World-class auditing should not require a world-class security budget or a full-time hire you do not have yet.
Why Vibe Coders Specifically
"Vibe coding" is not a slur. It is a description of how software gets made now. You describe intent, tools generate structure, and you iterate until it works. The output is real businesses, real users, and real data.
The old playbook assumed a different world. It assumed someone owned the threat model, maintained the asset inventory, and scheduled the quarterly pen test. If you are solo or on a tiny team, that playbook is fiction. What you need is signal without ceremony: did someone who understands attacks actually poke at this thing, and can I read the answer in plain English?
Axeploit is built for that person. You already know you are not an expert in every OWASP category. You should still know whether your login, your APIs, and your file uploads are standing up to scrutiny.
What Makes It Different
Most scanners want you to configure reality before they can simulate it. Endpoints, credentials, scopes, policies. That is fine if you have time. It is friction if you do not.
Axeploit takes a different path:
- Autonomous exploration. Agents navigate your application and discover attack surface from behavior, not from a form you filled out last month.
- Real auth testing. When your app needs email or phone verification, our stack includes LLM-controlled accounts so flows that matter get exercised, not skipped.
- Decisions, not scripts. The agents choose what to try next based on what they learn. Static checklists miss custom logic. This approach is built to chase it.
- Breadth you can feel. Authentication mistakes, injection classes, broken access control, CSRF, CVEs in server software, vulnerable JavaScript libraries in what you actually serve: over 7,500 checks feed into what you see.
When you change your app tomorrow, the next run sees the new paths. You are not maintaining a shadow specification of your own product just to keep a scanner honest.
What You Get Back
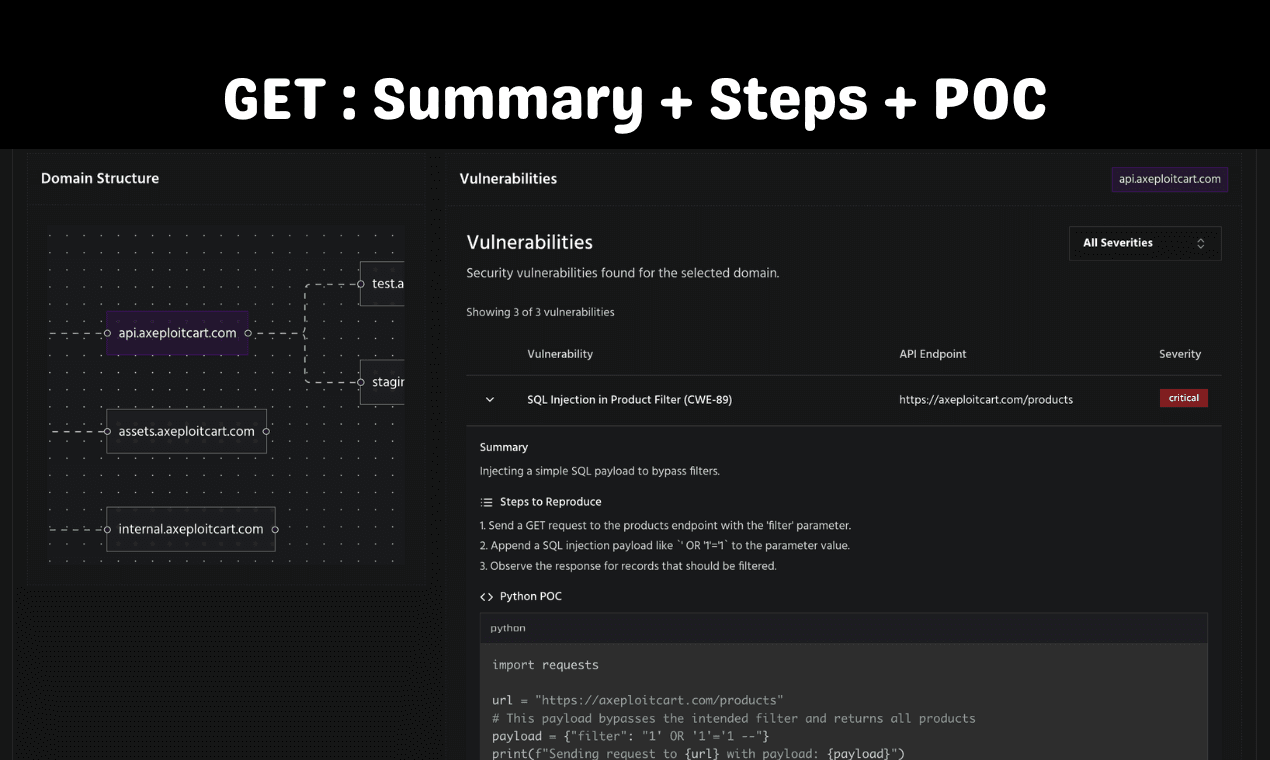
A report should answer three questions: what is wrong, how bad is it, and what do I do next. Axeploit is built around actionable findings, not a PDF that sits in a folder until someone asks for SOC 2.
You see issues tied to real paths and behaviors, not abstract IDs that send you hunting through logs. Severity is there so you can triage when everything feels urgent. When the finding is about a known CVE in something you are actually running, you get identifiers you can look up and verify for yourself.
This is not a replacement for every kind of review. If you need a human-led engagement with legal scope letters and a named lead tester, that still exists, and it still has its place. Axeploit is : continuous, affordable, and honest about what hackers can see from the outside.
Pricing That Matches How You Grow
We keep pricing fair and transparent because hesitation is how issues stay in production.
- $99 for a one-time audit when you need answers before a launch, a fundraise, or a nervous Tuesday night.
- Monthly plans from $199 to $499 when you want continuous coverage while you ship every week.
No minimum target bundles. No multi-year lock-in just to get a dashboard.
What You Do Next
If you build fast and you are tired of guessing whether your app can take a punch, stop treating security like a future project. Treat it like part of shipping.
Sign up and run your first audit: https://panel.axeploit.com/signup
One URL. Zero configuration. Proof you can act on. That is Axeploit.





