As a startup founder or business owner, your daily bandwidth is already maxed out. You are focused on customer acquisition, scaling your product, and managing your team. If you see a headline about “State-Sponsored Threat Actors” or “Zero-Day Exploits.” it is tempting to scroll right past it. After all, those sound like problems for massive, multinational banks with entire floors dedicated to IT security, right?
Unfortunately, that assumption is becoming the biggest vulnerability for growing businesses in 2026.
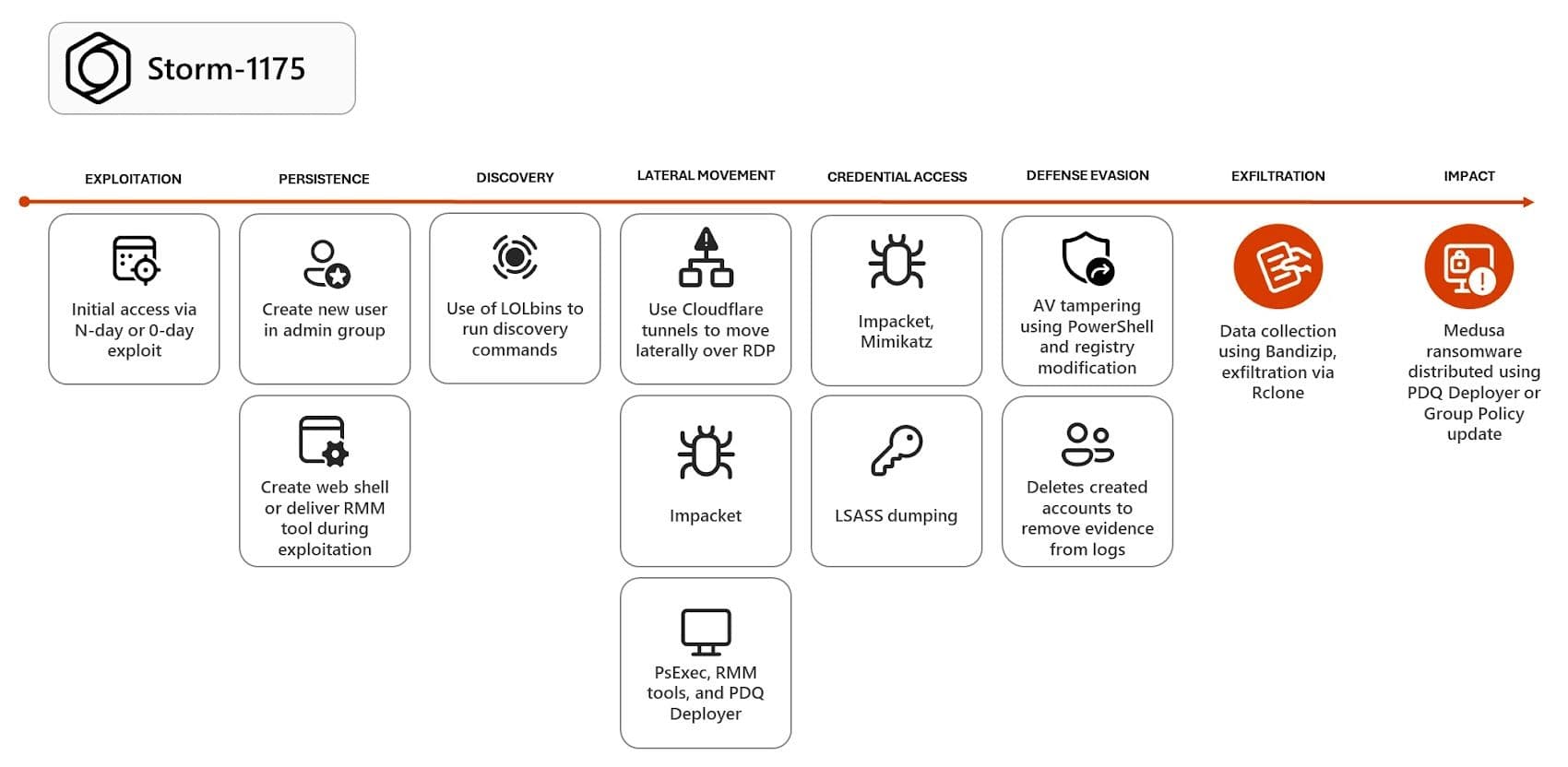
Recent cybersecurity intelligence from early 2026 has exposed a massive surge in cyberattacks orchestrated by a highly organized, China-linked hacking group known in the industry as Storm-1175. Their weapon of choice is something called Medusa Ransomware, and they are aggressively targeting mid-sized businesses, healthcare clinics, educational platforms, and professional services across the US, UK, and Australia.
If the terms “ransomware,” “zero-days,” and “lateral movement” sound like a foreign language, don't worry. This guide will decode exactly what is happening, how these modern hackers actually break into systems, and the simple, automated steps you can take to keep your hard work completely off their radar.
What is Medusa Malware? (And Who is Storm-1175?)
To understand the threat, we need to separate the tool from the people using it.
The Tool: Medusa Ransomware
Think of ransomware as a digital hostage situation. When Medusa malware infects your computer network, it rapidly scrambles (encrypts) all of your company's data, your customer records, your financial documents, your software code. Suddenly, you cannot open any files or run your business. The hackers then leave a digital ransom note demanding a massive payment (usually in cryptocurrency) in exchange for the “key” to unscramble your data.
The Hackers: Storm-1175
Storm-1175 is the codename for a specific, highly proficient group of cybercriminals based in China. What makes them so dangerous in 2026 is their sheer speed and their "high operational tempo." They do not waste time guessing passwords. Instead, they actively hunt for structural flaws in the software that businesses use every day.
How Do Hackers Actually Break In? (Decoding the Playbook)
Hollywood movies have conditioned us to believe that hacking involves a guy in a dark hoodie furiously typing on a keyboard until an “ACCESS GRANTED” screen pops up. The reality of how Storm-1175 operates is much quieter, much faster, and much more systematic.
1. The “Unlocked Window” Strategy (Zero-Days)
Imagine your business's digital network is a massive office building. You have locked the front doors (using passwords and basic security). However, Storm-1175 looks for “Zero-Days.”
A Zero-Day vulnerability is essentially a hidden, unlocked window in a piece of software that the software maker doesn't even know exists yet (hence, they have had “zero days” to fix it). In 2026, Storm-1175 was caught exploiting these hidden windows in popular business software, firewalls, and remote-work tools. Because no one knows the window is unlocked, the hackers slip right in, completely unnoticed by standard security guards.
2. Sneaking Through the Lobby (Lateral Movement)
Once Storm-1175 climbs through that unlocked digital window, they don't immediately set off the alarms. Instead, they use a technique called “living off the land.”
This means they use your computer's normal, built-in tools against you. They might hijack the legitimate remote-IT software your tech support team uses (like AnyDesk or ConnectWise) to quietly move from the receptionist's computer, to the sales server, and eventually into your core database. Because they are using “approved” tools, basic antivirus programs assume they are just normal employees doing their jobs.
3. The 24-Hour Countdown
In the past, hackers might lurk in a system for months. Storm-1175 is financially motivated and ruthless. Security researchers have noted that once they gain a foothold, they can steal your sensitive data and trigger the Medusa ransomware in just a few days, and in some terrifying cases, in less than 24 hours.
Why Your Basic Antivirus Won't Stop Them
This is the hardest pill to swallow for many non-technical founders: Your laptop's antivirus does not protect your cloud infrastructure or your web applications. An antivirus is essentially a digital bouncer that checks a list of “known bad guys.” If a file isn't on the bad guy list, it gets let in. But because Storm-1175 exploits brand-new flaws (Zero-Days) and uses your own legitimate software to move around, they don't look like bad guys to a traditional antivirus.
To stop a threat like Medusa, you cannot wait for the hackers to attack. You have to actively hunt for the “unlocked windows” in your own building before Storm-1175 finds them.
Axeploit: Your Automated AI Security Guard
As a lean startup or a growing business, you likely don't have the budget to hire a $150,000/year ethical hacker to constantly test your software for hidden flaws. This is where Axeploit changes the game.
Axeploit is not an antivirus; it is an advanced, proactive network and system security platform designed specifically for fast-moving businesses. It acts like an automated fleet of friendly hackers that patrol your business 24/7, actively looking for the exact vulnerabilities that groups like Storm-1175 exploit.
Here is how Axeploit keeps your startup safe from advanced malware and ransomware breaches:
1. Continuous “Unlocked Window” Detection
While hackers use automated scanners to find vulnerabilities to attack, Axeploit uses a continuous 7,500+ vulnerability scanner to find those holes so you can fix them. Axeploit constantly updates its CVE (Common Vulnerabilities and Exposures) intelligence database. This means the moment a new threat or flaw is discovered globally, Axeploit is already checking your systems to ensure you aren't exposed.
2. AI That Thinks Like a Human (Zero Configuration)
Traditional security tools are a nightmare to set up. They require complex coding and manual integration. Axeploit operates with Zero Configuration. It uses a powerful AI engine that actually interacts with your web application the way a real human would.
Axeploit can independently sign up for an account on your website, receive and input mobile OTPs (One Time Passwords), and navigate your dashboards. By doing this, it tests the deep, hidden logic of your application, finding flaws in how you authenticate users, which is exactly how hackers sneak past the front door.
3. Real-Time Fixes, Not Just Alarms
If Axeploit finds a vulnerability, like an exposed database or a broken access control, it doesn't just send a confusing technical report. It sends a real-time Slack alert detailing exactly where the hole is and provides plain-English guidance on how your developers can patch it immediately.
By using Axeploit, you are effectively closing every window, locking every side door, and ensuring that when automated threats like Medusa come knocking, they find an impenetrable fortress.
Conclusion: Securing Your Growth in 2026
Building a business is hard enough without worrying about international hacking syndicates holding your life's work for ransom. The rise of Storm-1175 and the Medusa malware proves that relying on outdated “checkbox” security like just having strong passwords and a basic antivirus is no longer viable.
The attackers are using automation to find your weaknesses. You must use automation to defend them. By adopting a proactive security mindset and leveraging AI-driven tools, you ensure that your startup's growth isn't derailed by a single, unseen flaw.
Don't wait to read about a new zero-day exploit in the news to wonder if your business is safe. Take control of your perimeter, find your vulnerabilities before the bad guys do, and get back to building your empire with peace of mind.





