Imagine you’ve just installed a high-tech security system for your home. It’s got the best locks, cameras, and a doorbell that talks to your phone. But there’s a tiny, invisible flaw: if someone knocks on the door in a very specific rhythm, the lock simply vanishes. No alarms go off, no windows break, the intruder just walks right in.
In the world of cybersecurity, that’s essentially what has happened with a massive new vulnerability called CVE-2025-55182, often nicknamed “React2Shell.”
As of April 2026, this flaw has become one of the most significant threats to modern websites. If you’re a developer, a business owner, or even just someone who uses the web (which is all of us!), understanding how these attacks work, and how to stop them is no longer optional.
The Bug That Broke the Modern Web
To understand React2Shell, we first need to look at the tools builders use to make the websites we love. Many modern sites are built using a framework called Next.js and a technology called React Server Components (RSC). These tools are like the pre-fabricated parts of a modern house; they make building fast, beautiful, and efficient.
What exactly is CVE-2025-55182?
At its heart, this is a “Remote Code Execution” (RCE) flaw. In plain English: it allows a stranger on the internet to run their own software on your server without needing a password.
Most hacks require a "key,” a stolen password or a trick to get you to click a bad link. React2Shell is different. It’s “pre-authentication,” meaning the hacker doesn't need to log in. They just send a specifically crafted message to the website, and the website's own code accidentally lets them take control.
The “React Flight” Problem
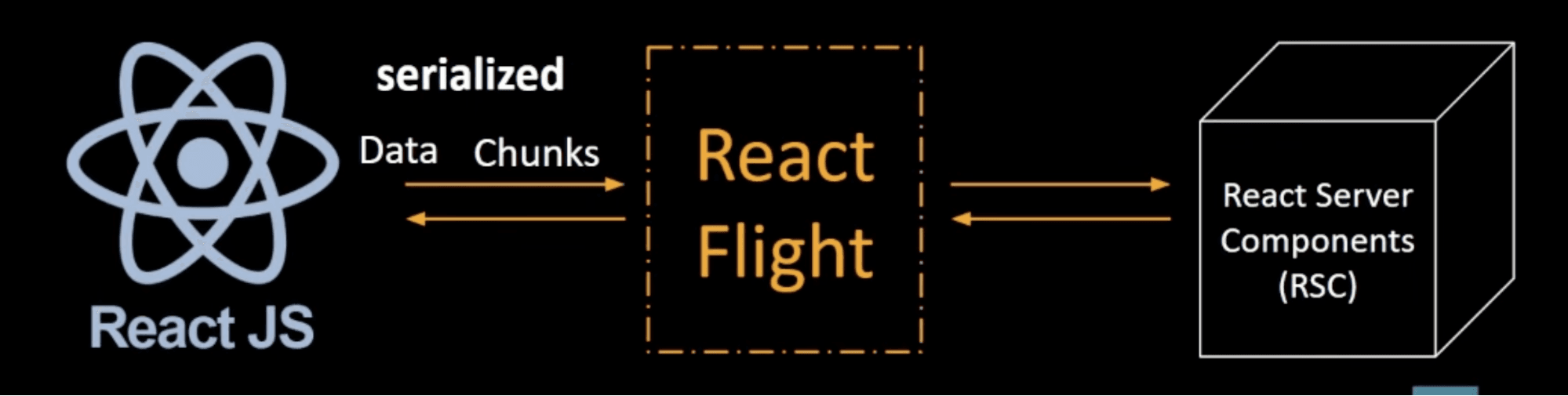
Modern websites “talk” to servers using a language called the React Flight protocol. Think of it like a shipping manifest. When you click a button, your browser sends a list of instructions to the server.
The vulnerability lives in how the server reads that manifest. Hackers figured out that if they “misspell” certain instructions or add hidden loops in the data, they can trick the server into getting confused. During this confusion, the server stops following its own rules and starts following the hacker's rules instead.
Meet UAT-10608: The Hackers Harvesting Your Digital Life
Security researchers (specifically the team at Cisco Talos) have been tracking a group they’ve named UAT-10608. This isn't just one bored person in a basement; it’s a highly organized “threat cluster” using automated bots to scan the entire internet for vulnerable sites.
As of early April 2026, they have successfully breached over 766 hosts. And they aren't just looking for fun, they are looking for your “digital keys.”
What is the “NEXUS Listener”?
Once these hackers get inside a system using the React2Shell bug, they drop a tool called the NEXUS Listener. Imagine a digital vacuum cleaner. This tool sits quietly in the background and sucks up every piece of sensitive information it can find:
- API Keys: These are the “master keys” that allow apps to talk to services like Stripe (for payments) or OpenAI (for AI features).
- SSH Keys: These allow hackers to log into other parts of a company’s network.
- Cloud Credentials: Access codes for AWS, Google Cloud, and Azure.
The NEXUS Listener even has a fancy dashboard (like a twisted version of Google Analytics) where the hackers can see exactly how many “keys” they’ve stolen and which companies they’ve compromised.
Why your data is at risk
Even if you don't run a website, this matters to you. If a service you use like a fitness app, a shopping site, or a work tool is built on Next.js and hasn't been patched, your personal data could be sitting in a hacker’s “NEXUS: dashboard right now. This intelligence is then sold to other criminals or used for identity theft and corporate espionage.
Why Traditional Security is Failing in 2026
For years, we’ve relied on “firewalls” and “antivirus” software. But in 2026, the game has changed. Hackers are now using AI-powered scanners that can find a single vulnerable line of code among millions in seconds.
Traditional security tools often require a human to tell them what to look for. But vulnerabilities like React2Shell move too fast. By the time a human security expert writes a “rule” to block the attack, the hackers have already moved on to 500 other targets.
Staying Safe: The Axeploit Shield for Your Network
This brings us to the most important question: How do we fight back? If hackers are using AI to attack us, we need to use AI to defend ourselves. This is where tools like Axeploit are changing the landscape. Unlike old-school scanners that require hours of setup and “manual tuning,” Axeploit is designed for the high-speed world of 2026.
Autonomous AI: Your New Security Guard
Axeploit uses a fleet of autonomous AI agents. Instead of just following a static checklist, these agents act like “friendly hackers.” They navigate your website just like a real user, they can even sign up for accounts, solve mobile OTP (One-Time Password) challenges, and test your login pages without any help from you.
Because Axeploit is “zero-config,” you don't have to be a cybersecurity genius to use it. You simply point it at your app, and its AI agents begin hunting for over 7,500 known vulnerabilities, including complex flaws like React2Shell.
Detecting the Undetectable
The magic of Axeploit lies in its ability to detect “business logic” flaws. Many traditional tools miss vulnerabilities because they don't understand how an app is supposed to work. Axeploit’s AI understands the context. It can detect:
- Authentication Bypasses: Finding ways to skip the login screen (exactly what React2Shell does).
- IDOR Attacks: Where one user can sneak a peek at another user's private data.
- Real-Time CVE Intelligence: As soon as a new bug like CVE-2025-55182 is discovered, Axeploit’s database is updated, and its agents start scanning for it immediately.
By integrating Axeploit into your workflow, you’re not just putting up a fence; you’re hiring a 24/7 security team that never sleeps, never gets tired, and is always one step ahead of the bad guys.
Conclusion: Building a Safer Digital Future
The “React2Shell” exploit is a wake-up call. It reminds us that as our web technology becomes more powerful and complex, the ways people can break it become more sophisticated too.
However, we aren't helpless. The key to staying safe in 2026 is proactivity. If you run a website:
- Patch Immediately: Ensure your Next.js and React packages are up to date.
- Rotate Your Secrets: If you think you might have been exposed, change your API keys and passwords.
- Automate Your Defense: Use modern, AI-driven tools like Axeploit to find the cracks before the hackers do.
Cybersecurity can feel overwhelming, but it doesn't have to be. With the right tools and a little bit of knowledge, we can keep our digital homes and our data safe from the shadows.





