If you are a CISO, a modern developer, or a “vibe coder” moving at breakneck speed in early 2026, you are likely focused on one thing: shipping incredible features and maintaining momentum. You are spinning up cloud environments, integrating AI APIs, and pushing code daily.
But while you are focused on building the future, advanced cybercriminal syndicates are focused on tearing it down.
When we think of a ransomware attack, Hollywood has conditioned us to picture a lone hacker in a dark room violently typing on a keyboard until a red skull appears on a screen. The reality of the modern ransomware lifecycle is far less cinematic, but far more organized. Today’s ransomware attacks are not smash-and-grab robberies; they are highly structured corporate operations with supply chains, specialized contractors, and dedicated payrolls.
To defend your infrastructure, you cannot just wait for the alarms to sound. You have to understand how the enemy thinks. Here is a holistic, blue-team look at the modern hacker’s playbook, and how you can break their attack chain before it ever reaches your users.
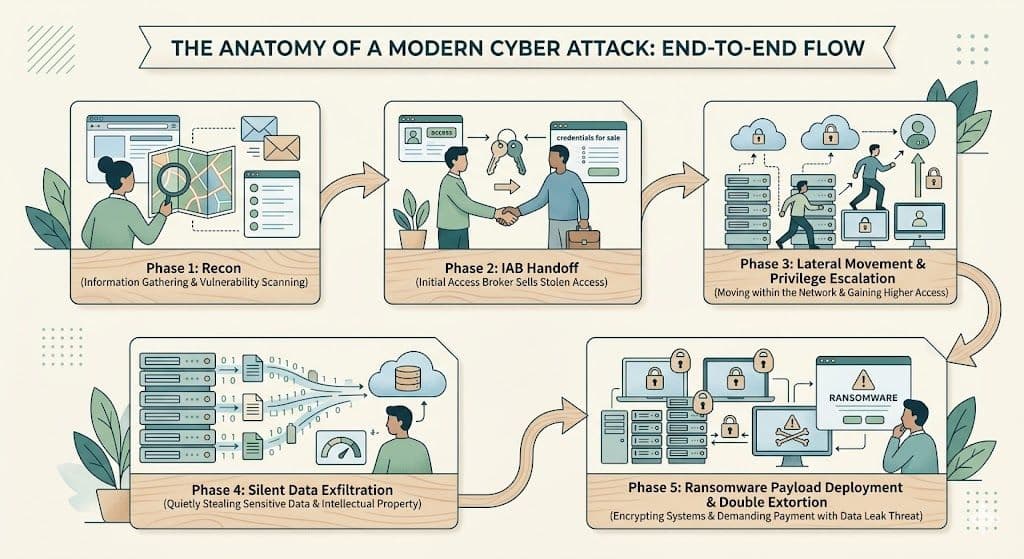
Phase 1: Reconnaissance (Finding the Forgotten Doors)
Hackers do not start an attack by throwing complex, noisy exploits at your front door. They start with silence.
The first stage of any targeted attack is reconnaissance. During this phase, attackers passively and actively map your entire digital footprint. They are looking for the forgotten, dusty corners of your infrastructure that your IT and security teams have lost track of.
Remember that forgotten staging server you spun up three years ago? Or the undocumented API endpoint from a deprecated mobile app? Attackers use automated tools to scan the internet for exactly these vulnerabilities. They hunt for exposed subdomains, misconfigured cloud storage buckets, and leaked AWS keys sitting in public GitHub repositories. In 2026, the attack surface for a rapidly growing tech company is massive, and attackers only need to find a single crack in the armor.
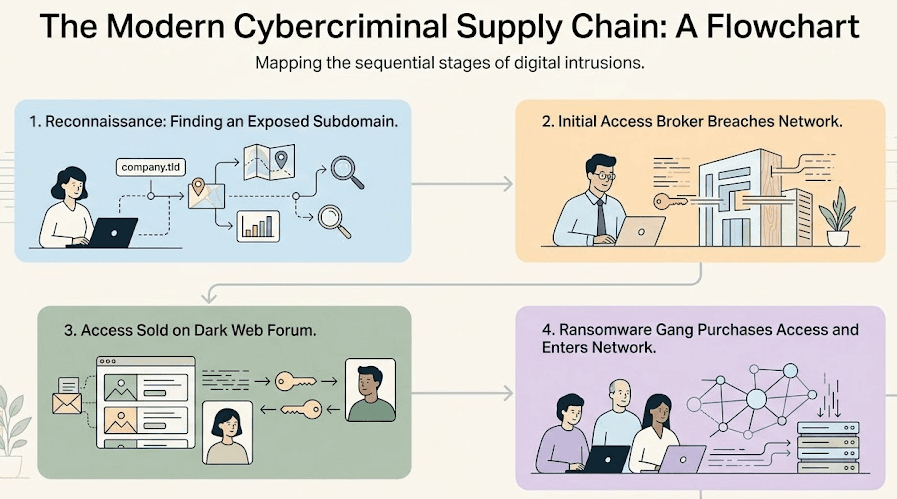
Phase 2: Initial Access Brokers (Buying the Keys)
Here is a reality check that often surprises developers: the hacker who deploys the ransomware is rarely the same hacker who broke into your network.
The cybercriminal underground has specialized. Enter the initial access brokers (IABs). IABs are elite hackers who specialize purely in breaking into corporate networks during the reconnaissance phase. Once they successfully compromise an environment, perhaps by exploiting an unpatched VPN or stealing a developer’s session token via a phishing email, they don't deploy malware.
Instead, they silently secure their backdoor, package the access credentials, and sell them on dark web forums to ransomware gangs. Think of IABs as the lockpickers who silently open the bank vault door, and the ransomware gangs as the robbers who walk in days later to clean it out.
Phase 3: Lateral Movement and Privilege Escalation (The Quiet Crawl)
Once the ransomware gang purchases access and enters your network, they do not immediately encrypt your files. If they bought access from an IAB who compromised a low-level marketing employee’s laptop, they don't have the permissions necessary to take down your company.
They need to move. This phase is called lateral movement. The attackers silently crawl through your network, jumping from server to server and identity to identity. They are hunting for misconfigured Active Directory settings, overly permissive CI/CD pipelines, and hardcoded database passwords.
Their goal is privilege escalation, turning that low-level marketing access into full, unrestricted “Domain Admin” or “Root” access. They want the master keys to your entire cloud infrastructure.
Phase 4: Data Exfiltration (The Double Extortion)
If you have a robust, offline backup strategy, you might think you are immune to ransomware. After all, if they lock your files, you can just wipe the servers and restore from yesterday's backup, right?
Hackers know this. That is why modern ransomware operations rely on “double extortion.” Before they lock a single file, they spend days, sometimes weeks, quietly siphoning your most sensitive data out of your network. They steal your proprietary source code, your customers' financial records, and your internal executive communications.
They exfiltrate this data to offshore servers. By the time the security team notices a spike in outbound network traffic, the damage is usually already done.
Phase 5: The Ransomware Deployment (Game Over)
Only after the attackers have mapped your network, secured root access, and stolen your data do they finally make some noise.
They deploy the ransomware payload across your entire infrastructure simultaneously. Servers go offline, databases are encrypted with unbreakable military-grade cryptography, and your internal communication tools go dark.
Then comes the ransom note. It is a dual threat: Pay us millions of dollars for the decryption key to get your business back online, AND pay us to prevent your stolen customer data from being leaked to the public internet.
Rewriting the Ending: Threat Intelligence and Incident Response
When the red screen appears, you are already too late. At Phase 5, your only options are a massive financial payout or a catastrophic business disruption.
To defeat modern ransomware, you have to stop the attack during Phases 1 through 3. This requires a proactive DevSecOps mindset and a reliance on actionable threat intelligence. You cannot just build a wall and hope it holds; you have to actively hunt for your own blind spots before the Initial Access Brokers find them.
A robust incident response plan is critical for minimizing damage when a breach occurs, but the ultimate goal is preventing the attackers from ever gaining a foothold.
How the Axeploit Changes the Game
Axeploit is designed to dismantle the hacker’s playbook at step one. Our automated vulnerability scanner does not just passively sit on your network; it actively attacks your live, running applications exactly how a malicious Initial Access Broker would.
- We find the forgotten doors: Axeploit continuously scans for shadow APIs, exposed subdomains, and unauthenticated endpoints that your team lost track of.
- We stop the pivot: If an attacker manages to get a foothold, our dynamic scanner identifies the overly permissive internal APIs and IAM misconfigurations they would use to escalate privileges.
We catch the vulnerabilities, flag them, and show you exactly how to patch them before your code goes live. By adopting continuous API discovery and active dynamic scanning, you can strip away the attacker's entry points and lateral pathways. The cybercriminal playbook relies on your team moving so fast that you leave doors unlocked.





