When you first learn about databases, they look a lot like giant Excel spreadsheets. And just like a spreadsheet, you need a way to keep track of every single row of information without getting things mixed up.
Enter the database key.
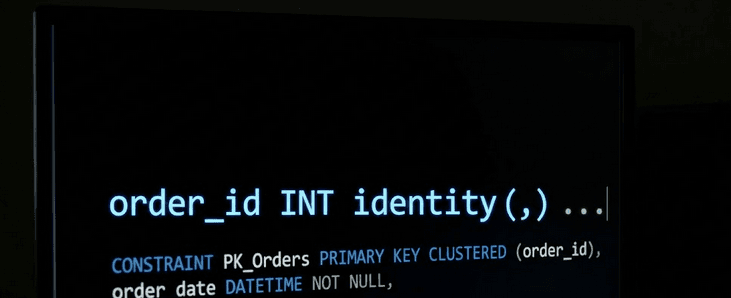
If you ask a beginner how to set up a database key, they’ll probably say, "Just add an 'ID' column, set it to count up automatically (1, 2, 3...), and you're done." But if you want your software to be fast, secure, and crash-proof as your business grows, there is actually a fascinating, hidden world behind how you choose and use these keys.
Here is a plain-English, beginner-friendly breakdown of what database keys are, the different types you can use, and the secret rules developers use to keep your data safe.
The Basics: Understanding Database Keys
Before diving into the complex security rules, we first need to define what a key actually does inside your system.
What Exactly is a Database Key?
Imagine you are at a massive coat check. You hand the attendant your jacket, and they hand you back a little numbered ticket. That ticket is a "key." When you return, you don't describe your jacket; you just hand them the ticket, and they instantly find exactly what belongs to you.
In a database, a primary key does the exact same thing. It is a unique identifier for a specific row of data. It ensures that out of millions of customers, products, or orders, the computer can instantly find the exact one it needs without getting confused.
The Two Flavors of Keys: Natural vs. Surrogate
When you are deciding what to use as your digital coat-check ticket, you generally have two choices:
1. Natural Keys (The Real-World Identifiers)
A natural key is a piece of data that already exists in the real world and has actual meaning to a human being.
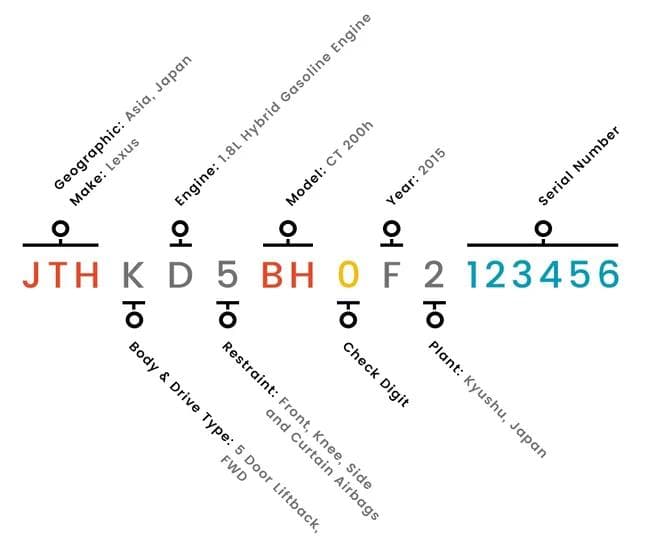
Because these are naturally unique to each person or item, they seem like the perfect choice for a database key.
2. Surrogate Keys (The "Made-Up" Identifiers)
A surrogate key is completely artificial. It is a random number or code generated by the database itself.
The Case for Artificial Identifiers
It might seem easier to just use a user’s email address as their database key (a natural key). But veteran developers almost always prefer to generate artificial surrogate keys. Here is why:
Why "Made-Up" (Surrogate) Keys Almost Always Win
- Real-world data changes: People get married and change their names. They lose access to old email addresses. If your entire database is linked together by an email address, and that email changes, your system has to frantically rewrite thousands of interconnected records. A surrogate key never changes.
- Real-world data is messy: What if a customer refuses to give you their email? What if a vintage car doesn't have a modern VIN? If your database strictly requires this real-world info to create a key, the system breaks.
- Real-world data is slow: Computers process simple numbers much, much faster than long strings of text. Searching a database for "ID: 459" is blazingly fast compared to searching for "john.smith_business_account@email.com".
The Hidden Danger of Counting (1, 2, 3...)
So, if artificial surrogate keys are the best, how do we make them?
The most common method is having the database automatically count up. The first customer is ID 1, the second is ID 2, and so on. But this creates a massive privacy and security issue.
Imagine you buy something from a new online store and your receipt says "Order #100." You buy something else a week later and the receipt says "Order #120." You now know exactly how many sales that store made that week. Worse, if a hacker sees that their user ID is 405, they know they can probably guess user ID 404 and 406 to try and steal data.
The UUID Solution: Universally Unique Identifiers
To fix this predictability, developers often use something called a UUID. Instead of a simple counting number, the database generates a long, crazy string of characters that looks like this: 123e4567-e89b-12d3-a456-426614174000.
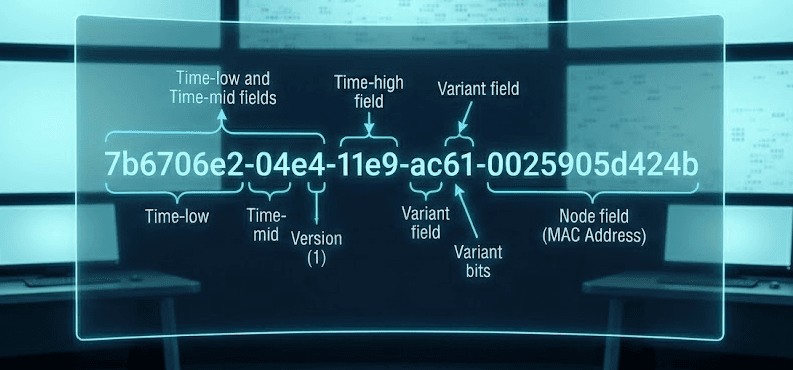
There are so many possible combinations in a UUID that it is mathematically impossible for the system to ever accidentally generate the same one twice. It is entirely random, meaning hackers can't guess the next one, and competitors can't track your sales volume.
(Note: UUIDs are incredibly secure, but because they are so long, they take up more storage space and can slow down very large databases. It's always a tradeoff!)
Advanced Security and Best Practices
Once you have chosen your keys, you have to protect them.
The Golden Rule: Keep Your Keys a Secret
The absolute best way to protect your database keys? Never let your users see them.
The magic of a surrogate key is that it is completely isolated from the outside world. The moment you put an internal database key on a public dashboard, a printed invoice, or a customized URL, it becomes part of the real world.
Once users start seeing and relying on that key, you lose the ability to easily upgrade, merge, or change your database behind the scenes without breaking their experience.
The Bottom Line
Database keys might seem like a minor technical detail left to the IT department, but they are the foundational glue that holds your entire business system together.
By using artificial (surrogate) keys, keeping them totally hidden from the outside world, and ensuring they aren't easily guessable by hackers, you ensure your software remains fast, flexible, and completely secure—no matter how much data you collect. Collecting data is one part of the equation; protecting it is another. Sometimes AI agents compromise your network and there are 5 ways to secure them. Check out Axeploit’s blog for such a helpful guide.





