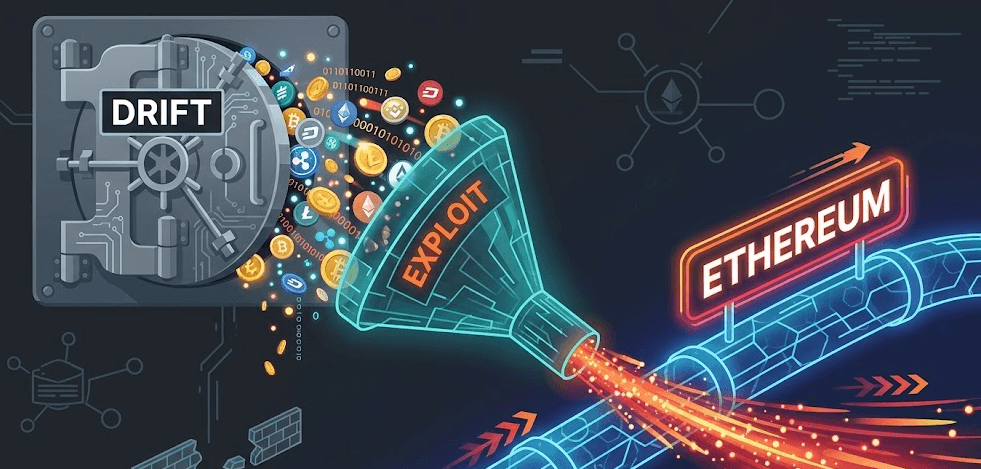
On April 1, 2026, the decentralized finance (DeFi) world received a shock that was definitely not an April Fool’s joke. Drift Protocol, a massive cryptocurrency trading platform built on the Solana network, was suddenly drained of an estimated $285 million.
But here is the scariest part: the hackers didn't break through a firewall, and they didn't find a hidden math flaw in Drift’s smart contract code. Instead, they used a combination of patience, human psychology, and a blockchain feature called a “durable nonce.”
If you don't know what a durable nonce is, or how someone can steal millions without actually “hacking” the code, keep reading. We are breaking down exactly what happened, how the money vanished, and what this structural weakness means for your own digital security.
How the Hackers Got Inside: The Setup
Usually, when you hear about a major cyberattack, it involves a genius coder breaking the system. Not this time. This was a highly sophisticated inside job executed from the outside, relying almost entirely on “social engineering,” the art of tricking humans rather than computers.
The “Durable Nonce" Loophole Explained
To understand how they got in, we have to talk about Solana's “durable nonces.”
In simple terms, a standard blockchain transaction is like a digital bus ticket: it expires very quickly if it isn't used right away. A durable nonce, however, is different. It is basically a pre-signed, undated blank check. It allows users to sign a transaction now, but hold onto it and execute it whenever they want in the future.
The hackers spent weeks preparing for this attack. They targeted the administrators (the digital “bank managers”) of Drift Protocol. Through deceptive tactics, such as disguising malicious files or commands as routine administrative paperwork, the hackers tricked these administrators into signing these “blank check” transactions.
Because the administrators thought they were signing normal protocol updates, the platform's security alarms stayed completely silent.
Creating the Phony Collateral
About three weeks before the main attack, the hackers created a totally worthless, fake cryptocurrency token called CarbonVote Token ($CVT). They artificially traded this token back and forth with themselves (a process known as wash-trading) to manipulate the data, making it look like their fake token had hundreds of millions of dollars in real value.
The Execution: How Drift Lost Millions in Minutes
With the pre-signed “blank checks” in hand, the hackers waited until the perfect moment on April 1st to cash them in.
Because they had tricked the administrators into signing away their rights, the hackers were able to essentially promote themselves to VIP status inside Drift Protocol. With just two lightning-fast transactions, they accomplished the impossible:
- They altered the rules: They used their stolen administrative power to approve their worthless $CVT token as legitimate, high-value collateral.
- They turned off the alarms: They disabled the platform's withdrawal protection limits.
- They took the money and ran: Using their worthless token as a guarantee, they “borrowed” and withdrew $285 million in real, valuable assets (like USDC stablecoins and Solana).
By the time the Drift team realized what was happening and hit the emergency brakes, the money was already gone. The hackers quickly converted the stolen funds into Ethereum and scattered it across multiple anonymous digital wallets to avoid tracking and detection.
The Contagion: Why This Matters to You (and Your System)
You might be thinking, “I don't use Drift Protocol, so why should I care?”
The 2026 Drift exploit is a massive wake-up call for everyone on the internet, whether you trade cryptocurrency, manage a corporate network, or just use online banking. It proves a terrifying reality: Your technical security is only as strong as the humans operating it.
The hackers didn't break Drift's code; they broke the people running it. This is a structural weakness that affects every company, app, and individual user. If you can be tricked into handing over your password, or authorizing a transaction you don't fully understand, even the world's most advanced security software cannot protect you.
Simple Steps to Protect Your Digital Assets
As cybercriminals realize that “hacking humans” is faster and more profitable than hacking code, you need to upgrade your personal security mindset:
- Never “Blind Sign” Anything: Whether it is a software update popup, an email attachment, or a crypto wallet approval, never click “Approve” unless you understand exactly what permissions you are giving away. If it looks confusing, stop.
- Beware of Urgent Requests: Hackers rely on panic. If you receive a message saying your account will be locked unless you click a link or sign a document right now, take a breath. Verify the request through official channels before taking any action.
- Isolate Your Wealth: If you manage high-value assets (like cryptocurrency or business bank accounts), consider doing so on a dedicated, clean device that you do not use for casual web browsing, downloading apps, or opening emails.
The $285 million Drift hack proves that in 2026, the biggest vulnerability in any computer system isn't the software, it's the person sitting in front of the screen. Stay skeptical, stay secure, and guard your network like it's the key to your bank account, because it is.





