Your scanner found 12 SQL injection attempts, a missing Content-Security-Policy header, and an outdated jQuery version. It missed the flaw where any logged-in user can view, edit, and delete every other user's account data by changing a single ID parameter.
That's a business logic flaw. Your scanner will never find it. Not because it's misconfigured. Because it was never designed to look.

What Business Logic Flaws Actually Are
A business logic flaw is a vulnerability that lives in how your application makes decisions, not in how it handles input. There's no malicious payload. No injection. No malformed request. The attacker uses your application exactly as designed, just in a way you didn't anticipate.
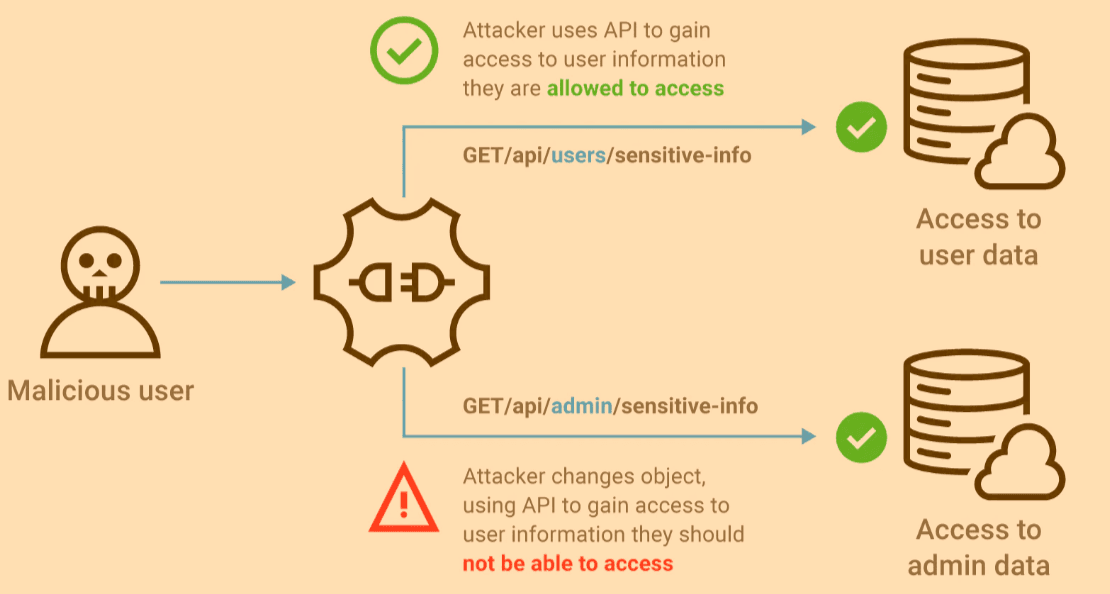
BOLA (Broken Object Level Authorization) is the clearest example. Your API serves user profiles at /api/users/142. The logged-in user is user 142. They change the URL to /api/users/143 and get someone else's profile back. The request is syntactically valid. The server responds with a clean 200. The only problem is the application never checked whether user 142 should have access to user 143's data.
OWASP has ranked BOLA as the number-one API security risk for three consecutive years. Not because it's technically sophisticated. Because it's everywhere and almost nothing detects it automatically.
Other logic flaws follow the same pattern. An e-commerce checkout that accepts negative quantities, dropping the total below zero. A subscription API that lets users upgrade their plan by replaying a modified request without payment. A multi-tenant SaaS where swapping a tenant ID in a request leaks data across organizations.
None of these involve injecting anything. They all require reasoning about what the application should allow versus what it actually allows.
Why Signature-Based Scanning Misses the Entire Category
A traditional DAST scanner like ZAP operates on a straightforward model: send known attack payloads, observe responses, match patterns.
SQL injection? The scanner sends ' OR 1=1 -- and checks if the response changes. XSS? It injects a script tag and looks for reflection. Path traversal? It tries ../../etc/passwd and searches for root in the output.
Each test has a payload and an expected result. The scanner doesn't need to understand what the application does. It just needs to know what exploitation looks like.
Business logic flaws don't have payloads. There is no signature for "this user shouldn't be able to see that data." The request that triggers BOLA is a perfectly normal GET request with a valid parameter. The response is a perfectly normal 200 with valid JSON. Nothing in the HTTP exchange, taken in isolation, looks wrong.
To detect BOLA, you need to know three things at once: who the current user is, what objects they own, and whether the requested object belongs to someone else. That requires maintaining state across multiple requests, understanding identity boundaries, and reasoning about authorization rules the application enforces or fails to enforce.
ZAP can't do that. Its architecture replays attacks from a database. Business logic security testing requires forming a hypothesis about how the application should behave and then designing an experiment to check whether it does.
That gap isn't a missing plugin or a configuration toggle. It's a category mismatch. You're asking a pattern matcher to do a reasoning task.
What an Autonomous Reasoning Engine Does Differently
An agentic AI scanner doesn't start with a payload database. It starts with the application itself.
The agent creates its own accounts, logs in as different users, and maps what each identity can access. It observes that user A owns objects 1, 2, and 3. User B owns objects 4, 5, and 6. Then it forms a hypothesis: can user A access object 4?
That's not a signature lookup. It's a reasoning chain. The agent identified a resource boundary, understood ownership, and built a test to verify whether the boundary holds.
The same logic applies across every category of stateful flaw. The agent spots a checkout flow where quantity is set client-side and tests what happens with a negative value. It notices a role parameter in a request body and checks whether a standard user can escalate to admin by modifying it. It finds a multi-step process and tests whether steps can be skipped or replayed out of order.
Each test is generated on the fly, specific to your application's behavior. No predefined payload. No pattern match. A hypothesis, an experiment, and a result.
When the agent confirms a logic flaw, it captures everything: the authenticated sessions used, the requests that crossed the boundary, and the server responses proving unauthorized access occurred. That's not a theoretical finding. It's a proof-of-concept your developer can reproduce in five minutes.
The Blind Spot in Your Current Stack
If you're running traditional DAST, you have coverage for injection attacks, known CVEs, and server misconfiguration. That coverage is real and worth keeping.
But it leaves business logic completely unaddressed. The vulnerabilities behind the largest data breaches in 2025 and 2026 aren't exotic zero-days. They're authorization flaws in APIs that any authenticated user can exploit with a browser's developer tools. The kind of flaw that a signature-based scanner is architecturally incapable of finding.
Closing that gap takes a tool that reasons about your application, not one that replays attacks against it.
Try autonomous logic testing: https://panel.axeploit.com/signup





