If you know a little about cyber attacks, you likely know that no system is entirely foolproof. But when a major foundational pillar of the modern internet takes a hit, it sends shockwaves across the tech community.
In mid-April 2026, Vercel, a massive cloud platform that powers countless websites, confirmed a significant data breach. Hackers managed to slip past their defenses, steal sensitive internal data, and are now allegedly holding it for a massive $2 million ransom while attempting to sell it on underground forums.
But what exactly is Vercel? How did the hackers pull this off? And more importantly, how do cybercriminals use this kind of stolen data to exploit everyday internet users?
In this comprehensive guide, we are going to break down the Vercel data breach into simple terms. We will explore the mechanics of the attack, the domino effect it creates, and provide you with an actionable, step-by-step guide to detecting malware and keeping your own systems locked down.
Understanding the Target: What is Vercel?
Before diving into the hack, it helps to understand the victim. Think of Vercel as the digital landlord and construction crew for modern websites. It is a highly popular cloud development platform that allows software engineers to build, host, and deploy web applications quickly. They are famous for creating Next.js, a framework used by some of the biggest brands in the world to make their websites load incredibly fast.
Because Vercel hosts the underlying code and infrastructure for so many companies, breaching them is like stealing the master keys to an entire apartment complex.
The Anatomy of the Attack: How Hackers Broke In
You might assume that hacking a tech giant involves writing millions of lines of complex code in a dark room. The reality of the 2026 Vercel breach is much more relatable and frightening. It all started with a trusted third-party application.
The Weakest Link: Third-Party AI Tools
According to Vercel's CEO, the initial break-in didn't actually happen on Vercel's main servers. Instead, the hackers compromised a third-party artificial intelligence platform called Context.ai.
A Vercel employee had connected their Google Workspace account to this AI tool using something called an “OAuth application.” In simple terms, OAuth is a digital handshake. It allows two apps to share information without you having to give out your actual password (like when you click “Log in with Google” on a new website).
When the hackers breached Context.ai, they manipulated this digital handshake to hijack the Vercel employee's Google account.
Stealing the “Sticky Notes” of the Internet
Once inside the employee's account, the attackers escalated their privileges to access Vercel's internal environments. Here, they hunted for Environment Variables.
Think of environment variables as digital sticky notes that developers use to store important configuration data, things like database passwords, API keys, and server names. Vercel states that they encrypt (scramble and lock) all highly sensitive customer variables. However, they allowed developers to label certain variables as “non-sensitive,” meaning they weren't locked up as tightly.
The hackers found a way to read these unlocked, “non-sensitive” sticky notes. While they weren't the master passwords, these notes contained enough structural information for the attackers to map out Vercel's internal network and steal source code, access keys, and employee data.
The Fallout: How Hackers Exploit Stolen Cloud Data
The threat actor claiming responsibility goes by the moniker “ShinyHunters” (though some in the cybersecurity community dispute their true identity). They quickly took to hacking forums, boasting about their loot: 580 employee records, internal access keys, source code, and NPM/GitHub tokens.
But how does this affect regular people?
When hackers steal “API keys” and “source code” from a cloud provider, they aren't just looking to embarrass the company. They use these tools to launch supply chain attacks.
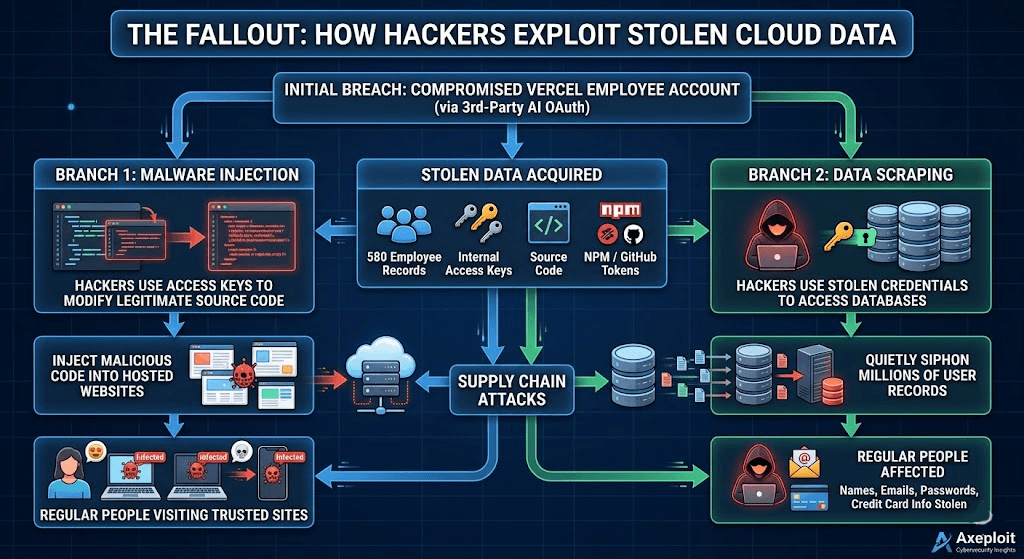
- Malware Injection: With the right keys, hackers can silently insert malicious code into legitimate websites hosted on the platform. When everyday users visit these trusted sites, their devices can be infected with malware without them ever knowing.
- Data Scraping: Stolen database credentials can be used to quietly siphon millions of user records including emails, passwords, and credit card numbers, which are later used for identity theft and phishing scams.
Step-by-Step Guide: How to Detect Malware and Keep Your System Safe
As we've seen with the Vercel incident, a single compromised third-party app can lead to a massive breach. Whether you are a developer hosting a site or an everyday user browsing the web, you need a proactive defense strategy.
Here is a step-by-step guide to detecting hidden malware and securing your digital environment against similar cyber threats.
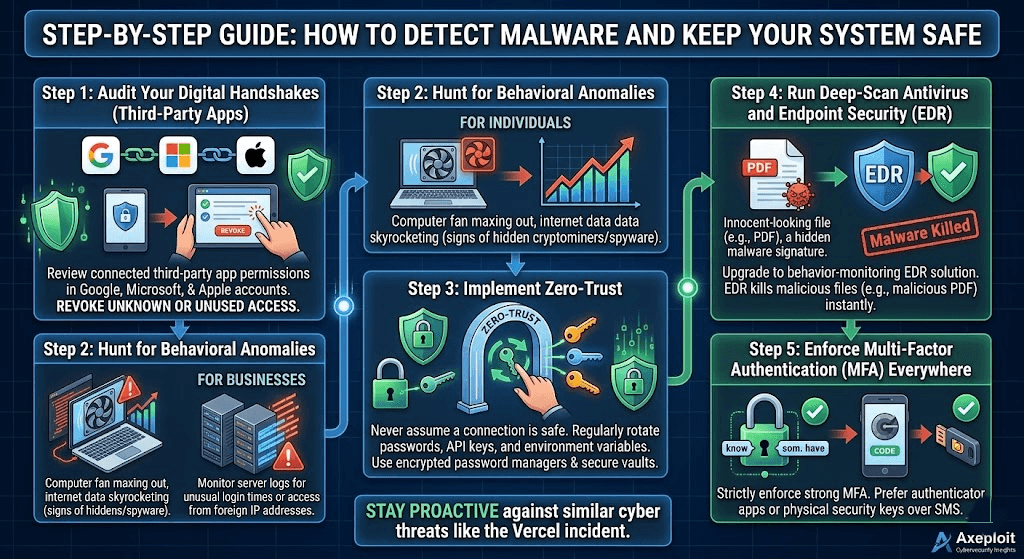
Step 1: Audit Your Digital Handshakes (Third-Party Apps)
The Vercel breach started through a connected AI app. You must regularly review what applications have access to your primary email and work accounts.
- Go to your Google, Microsoft, or Apple account security settings.
- Look for “Third-party apps with account access.”
- Immediately revoke access for any application you no longer use or don't recognize.
Step 2: Hunt for Behavioral Anomalies
Malware and unauthorized users often leave subtle footprints. You don't need to be a coder to spot them.
- For individuals: Is your computer fan running at maximum speed when you have no apps open? Is your internet data usage suddenly skyrocketing? These are classic signs of hidden malware (like cryptominers or spyware) running in the background.
- For businesses: Monitor your server logs for unusual login times or access requests coming from foreign IP addresses.
Step 3: Implement Zero-Trust and Rotate Your Keys
In the cybersecurity world, “Zero Trust” means never assuming a connection is safe.
- If you manage a website, regularly rotate (change) your passwords, API keys, and environment variables.
- Never leave sensitive data stored in plaintext. Use encrypted password managers and secure cloud vaults. If a hacker breaches your perimeter, you want to ensure all the internal doors are locked.
Step 4: Run Deep-Scan Antivirus and Endpoint Security
Basic antivirus is no longer enough to stop modern malware injected via supply chain attacks.
- Upgrade to an Endpoint Detection and Response (EDR) solution. Unlike old scanners that just look for known viruses, EDR monitors the behavior of the files on your computer. If an innocent-looking PDF suddenly tries to modify your system registry, the EDR will kill the process and quarantine the malware instantly.
Step 5: Enforce Multi-Factor Authentication (MFA) Everywhere
If the Vercel employee's account had strictly enforced, hardware-based MFA for internal lateral movement, the attackers might have been stopped dead in their tracks. Always use an authenticator app (or a physical security key) rather than SMS text messages, as text messages can easily be intercepted by hackers.
Conclusion
The April 2026 Vercel data breach serves as a stark reminder that the cloud is just somebody else's computer, and it is only as secure as its weakest link. A simple third-party integration failure cascaded into a multi-million dollar extortion event, proving that cybercriminals are constantly evolving their tactics to bypass traditional security perimeters.
While Vercel has since updated its dashboard and forced encryption on previously non-sensitive environment variables, the responsibility of digital safety is shared. By auditing your third-party apps, monitoring for malware, and locking down your credentials, you can ensure that you don't become the next victim of a supply chain exploit.
Stay vigilant, stay secure, and keep checking back at Axeploit for the latest updates on the ever-changing cybersecurity landscape.





