PostgreSQL is the default database for half the apps shipping today. If you're building with Supabase, Railway, Render, or spinning up a VPS, there's a good chance Postgres is what's running underneath.
It's also one of the most targeted databases on the internet. Right now, Shodan indexes over 187,000 PostgreSQL instances exposed on port 5432. That means 187,000 databases accepting connections from anyone who knows where to look. Some of them are probably yours.
And the problem goes deeper than an open port.
Four CVEs That Let Attackers Run Code on Your Database
In 2025 and early 2026, PostgreSQL disclosed a series of critical vulnerabilities. These aren't theoretical. They have severity scores between 8.1 and 8.8 out of 10, and they let attackers execute arbitrary code on your server.
CVE-2025-1094 is a SQL injection flaw in PostgreSQL's own escape functions. The functions you're supposed to use for sanitization, PQescapeLiteral() and PQescapeString(), don't properly handle certain multibyte character encodings. An attacker who can send crafted input through your application can bypass the sanitization entirely. CVSS 8.1.
CVE-2026-2005 is a heap buffer overflow in pgcrypto, the extension many apps use for hashing and encryption. If your app uses pgcrypto for password hashing or data encryption, a crafted query can overflow the buffer and execute code as the database OS user. That's not a database compromise. That's a server compromise. CVSS 8.8.
CVE-2026-2006 hits text processing. Missing validation of multibyte character lengths lets an attacker cause buffer overruns through crafted queries. Same result: arbitrary code execution. CVSS 8.8.
CVE-2025-8715 targets pg_dump, the tool you use for backups. A newline character injected into a database object name can execute arbitrary SQL when the dump is restored. If you're restoring backups from a compromised source, you're running attacker-controlled SQL on your production database. CVSS 8.8.
All of these have patches. Most haven't been applied.
The Default Config Problem
Even without CVEs, most Postgres installations ship with settings that make an attacker's job easier.
The pg_hba.conf file controls who can connect and how they authenticate. A fresh install on many cloud setups allows connections from 0.0.0.0/0 with md5 authentication. That means anyone on the internet can attempt to log in if they guess the credentials. And the default credentials for Postgres are postgres / postgres.
There's also the trust authentication method, which lets any connection through with no password at all. It shows up on local development setups constantly. It also shows up on production servers that were "just a dev box" until they weren't.
Then there's COPY FROM PROGRAM. This PostgreSQL feature lets you execute shell commands directly from a SQL query:
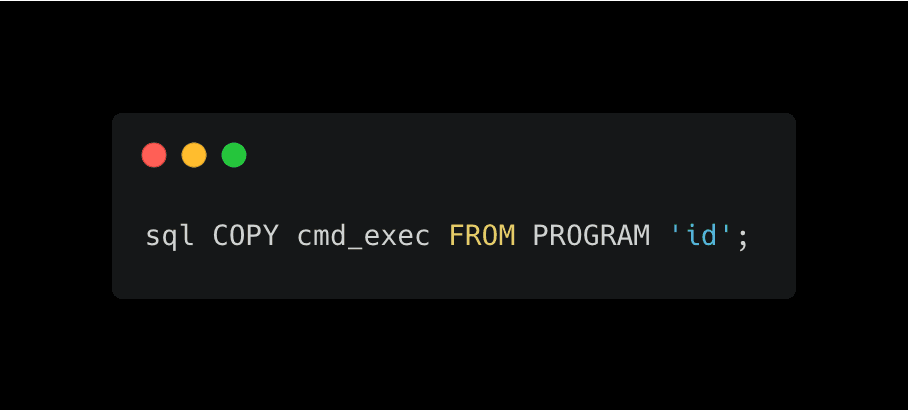
If an attacker gets database access with sufficient privileges, they can run operating system commands through SQL. No exploit needed. It's a built-in feature.
Combine an exposed port, default credentials, and COPY FROM PROGRAM, and an attacker goes from finding your database to owning your server in under a minute.
What to Check Right Now
If you're running Postgres, here's what matters most.
1. Check your version. Run SELECT version(); and compare it to the latest patched releases. If you're on PostgreSQL 17 before 17.8, 16 before 16.12, or 15 before 15.16, you're vulnerable to the 2026 CVEs. Update immediately.
2. Lock down `pg_hba.conf`. Replace 0.0.0.0/0 with specific IP ranges that actually need access. Never use trust authentication in production. Use scram-sha-256 instead of md5.
3. Don't expose port 5432. Put your database behind a firewall or private network. If your application server is the only thing that needs database access, the rest of the internet shouldn't be able to connect.
4. Revoke unnecessary privileges. Your application's database user shouldn't be a superuser. Remove SUPERUSER, CREATEDB, and CREATEROLE from application accounts. Restrict access to only the schemas and tables the app actually needs.
5. Disable extensions you don't use. If you're not using pgcrypto or pg_trgm, drop them. Every enabled extension widens your attack surface.
The Blind Spot
Axeploit's AI agents test your entire application for database-related vulnerabilities automatically. SQL injection, connection string exposure, default credentials, misconfigured access controls. No setup required. You give it a URL and it works the same way an attacker would, except you get the report instead of a breach.
Start your first scan: https://panel.axeploit.com/signup





