If you are a developer in early 2026, your primary goal is velocity. You want to write code, push your commits, and see your features live in production before your coffee gets cold. To achieve this, the modern “vibe coder” relies heavily on automation. You commit your code, and almost like magic, your build environment takes over testing, packaging, and deploying your application automatically.
But what happens when the very machinery you trust to build your application is compromised?
For years, the security community focused heavily on the code you write and the third-party libraries you import. But today, sophisticated attackers have shifted their crosshairs. They aren't just looking for a vulnerability in your code; they are actively targeting your CI/CD pipelines (Continuous Integration / Continuous Deployment).
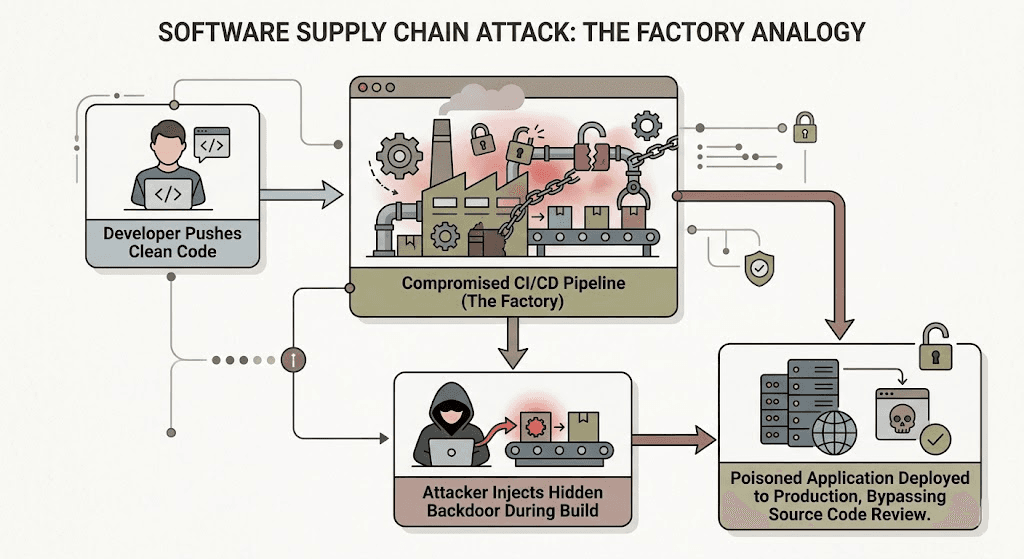
Welcome to the era of the next-generation supply chain attack, where hackers don't just poison the product, they poison the factory itself.
The Shift: From Bad Code to Compromised Build Environments
To understand this shift, let's use a simple analogy. Imagine your software application is a high-end sports car.
In a traditional attack scenario, a hacker might try to sneak a faulty brake pad into the factory's inventory. When the mechanics (your developers) build the car, they accidentally install the faulty part. In the software world, this is equivalent to accidentally installing malicious dependencies from a public registry like npm or PyPI.
However, the next-gen supply chain attack is far more insidious. Instead of sneaking in a bad part, the attacker breaks into the factory at night and reprograms the robotic assembly arms. The mechanics bring perfectly safe, pristine parts to the line, but the compromised robots secretly inject a tracking device into the car's chassis right before it rolls out the door.
In the digital world, your “factory” is your CI/CD pipeline, tools like GitHub Actions, Jenkins, or GitLab CI. If an attacker gains control of this environment, they can inject malicious code into your application during the build process, completely bypassing human code reviews and static analysis tools.
What is a CI/CD Pipeline Attack?
A CI/CD pipeline attack occurs when an unauthorized user gains the ability to manipulate the automated processes that build, test, and deploy your software. Because these pipelines are designed to have deep, privileged access to your production servers, cloud infrastructure, and secret keys, they represent a massive, glittering jackpot for cybercriminals.
How Attackers Exploit CI/CD Security
You might be wondering: How does a hacker actually break into an automated pipeline? It almost always comes down to misconfigurations, overly permissive access, and the unique ways these environments operate.
1. Exploiting GitHub Actions Vulnerabilities
One of the most popular CI/CD platforms today is GitHub Actions. While incredibly powerful, it is surprisingly easy to misconfigure. A common vector involves the pull_request_target trigger.
Normally, when a developer submits a pull request, the pipeline runs tests in a safe, isolated environment. But if misconfigured, the pipeline might execute the untrusted code submitted by a random internet user with the full permissions of your repository. The attacker simply submits a malicious pull request, the pipeline automatically runs it, and the attacker uses that execution to steal your environment's secrets or rewrite the build artifacts.
2. Leaking Pipeline Secrets
Your pipeline needs credentials to do its job. It needs database passwords for testing, AWS keys to provision servers, and API tokens to talk to other services. Often, these secrets are accidentally printed in pipeline logs or stored in plain text within the pipeline configuration files. Attackers scrape public and private repositories looking for these exact strings, using them to escalate their privileges and take over your infrastructure.
3. Compromised Third-Party Pipeline Tools
Just as your application relies on third-party libraries, your pipeline relies on third-party plugins. If you use an obscure or unverified GitHub Action from the marketplace to format your code, and that Action's creator gets hacked, the attacker can push a malicious update. The next time your pipeline runs, it pulls the poisoned plugin, compromising your entire build.
Locking Down Your Pipeline Security (Actionable DevSecOps)
Securing your build environment requires adopting a DevSecOps mindset—integrating security directly into the daily workflow rather than treating it as an afterthought. Here is how you can lock down your pipeline and prevent these devastating attacks.
Apply the Principle of Least Privilege
Your CI/CD pipeline should only have the exact permissions it needs to perform its specific task, and absolutely nothing more.
- Restrict Token Scopes: If a pipeline only needs to read a file, do not give it a token with write access to your entire repository.
- Isolate Environments: Use separate deployment environments. A pull request build should never have access to production database credentials.
Pin Your Actions and Dependencies
When you configure your pipeline to use a tool, you often specify a version (e.g., uses: actions/checkout@v4). However, tags like v4 can be moved by the maintainer to point to a compromised version.
- Use Commit Hashes: To guarantee pipeline security, pin your third-party actions to a specific, immutable cryptographic hash (e.g., uses: actions/checkout@a5ac7e5...). This ensures that even if the tool is hacked, your pipeline will only use the version you explicitly verified.
Protect and Rotate Your Secrets
Never hardcode secrets in your build scripts. Use dedicated secret management tools (like AWS Secrets Manager, HashiCorp Vault, or GitHub Secrets). Furthermore, ensure your CI/CD platform is configured to mask secrets in the build logs so they are never accidentally exposed to developers reading the terminal output.
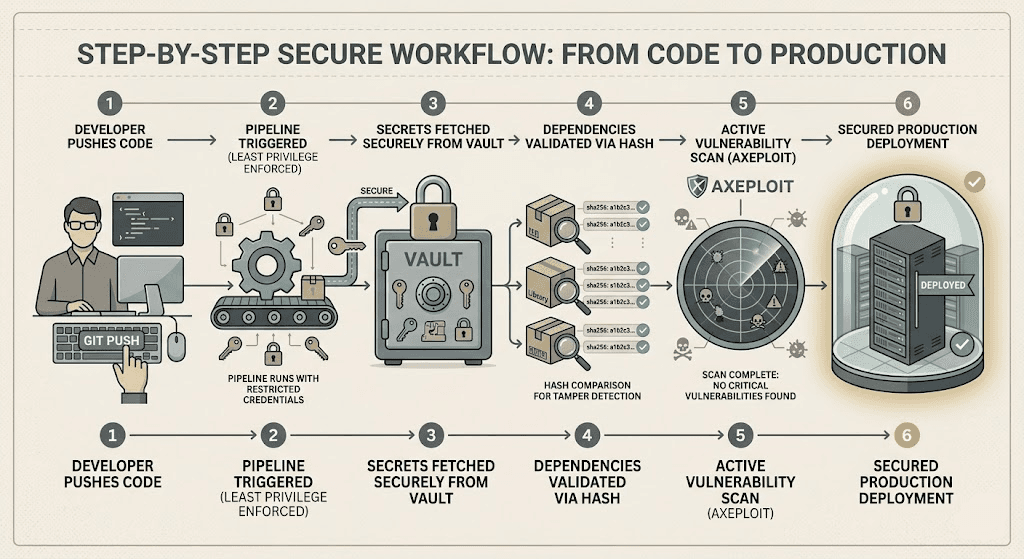
How Axeploit Fits into DevSecOps
Securing the pipeline is critical, but defense-in-depth means assuming that eventually, something might slip through. What happens if a sophisticated attacker manages to bypass your pipeline controls and injects a backdoor into your staging environment?
This is where traditional static analysis fails, because the malicious code was injected after the source code was checked. You need a tool that tests the final, assembled product.
Axeploit's automated vulnerability scanner is designed for this exact reality. While your pipeline handles the building, Axeploit acts as your final, active line of defense. Our automated scanner actively tests your live, running application. Instead of waiting for a breach, Axeploit safely attacks your app from the outside, exactly how a malicious hacker would.
If a compromised pipeline manages to deploy a hidden API endpoint or a hardcoded secret, Axeploit’s dynamic scanner will catch it, flag it, and show you exactly how to fix it before you go live.
Conclusion: Secure the Assembly Line
The speed at which we build software today is nothing short of incredible. But as the industry relies more heavily on automation, CI/CD security has become the new frontline of the cyber war.
Your application is only as secure as the environment that builds it. By locking down your pipeline permissions, managing your secrets rigorously, and adopting active testing tools like Axeploit to catch what slips through, you can ensure that your automated factory only produces secure, bulletproof code.





