In the early 2000s, building a secure website was like building a medieval castle. You put up a big wall (the firewall), you closed the portcullis (blocked all ports except 80 and 443), and you hired a guard to make sure no one was carrying a battering ram (SQL injection strings).
Today, we’ve gotten really good at building those walls. We have Web Application Firewalls (WAFs) that can spot a Cross-Site Scripting (XSS) payload from a mile away. We have rate limiters that shut down botnets before they can finish their first cup of coffee.
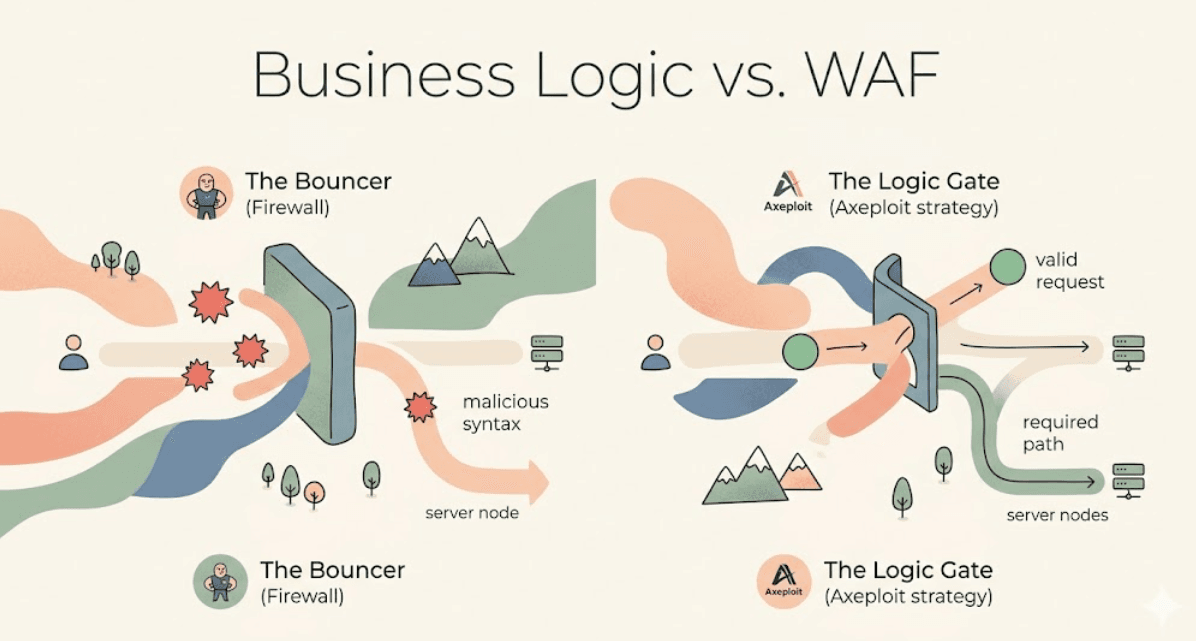
But there’s a problem. A WAF is a bouncer, not a private investigator.
A bouncer stands at the door of a club and checks for two things: Is your ID real? And are you carrying a weapon? If you have a valid ID and no weapon, you’re in. The bouncer doesn't follow you to the bar to see if you’re systematically tricking the bartender into giving you free drinks by exploiting a loophole in the "Buy 1 Get 1" promotion.
That is Business Logic Abuse. And it is currently the most dangerous "blind spot" in modern software.
At Axeploit, we don't just look for broken windows. We look for the ways an attacker can walk through the front door, say "hello" to the staff, and walk out with the safe all while following every single rule in your API documentation.
The Architecture of a Logic Flaw
Most security tools operate on Syntax. They look at the structure of a request.
- Does it contain
<script>? (Block) - Is it 50MB of garbage? (Block)
- Is it a valid JSON object? (Allow)
Business Logic Abuse operates on Semantics. It looks at the meaning and intent of the request. To a firewall, a request to delete your own profile looks exactly the same as a request to delete someone else’s profile. They are both "Valid JSON."
1. The "Infinite Discount" (Price Manipulation)
This is the classic example. A developer creates a checkout flow. The frontend calculates the total price and sends it to the backend.
POST /checkout{ "item_id": 404, "quantity": 1, "total_price": 500.00 }
The bouncer (WAF) sees a perfectly formatted JSON object. The numbers are numbers, the strings are strings.
But what happens when an attacker changes total_price to 0.01? If the backend trusts the frontend’s calculation, the attacker just bought a $500 item for a penny. The "logic" was that the server assumed the client was being honest. In security, "Assuming Honesty" is another way of saying "Giving Away Your Product."
2. The Step-Skipping Sprinter (Workflow Bypass)
Modern apps are state machines. You go from Step A (Login) to Step B (Payment) to Step C (Success). Firewalls are stateless. They see each request in a vacuum.
If an attacker knows the URL for Step C is /api/v1/download?file=premium_report.pdf, they might try to hit it directly without ever visiting Step B. If your code only checks "Is the user logged in?" but fails to check "Has the user actually paid for this specific file?", the firewall won't save you. It sees a logged-in user making a valid request.
3. The Race to the Bottom (Race Conditions)
Imagine you have a promo code that can only be used once.
- User submits code.
- Server checks DB: "Has this code been used?" (No)
- Server applies discount.
- Server updates DB: "Code is now used."
An attacker sends 50 requests at the exact same millisecond. Because of how databases and multi-threading work, requests 1 through 10 might all reach "Step 2" before the first request hits "Step 4." Suddenly, that "one-time" code has been applied ten times. Your rate limiter didn't trip because 10 requests in a second is "normal" behavior. The bouncer thought they were 10 different people; the private investigator would have noticed they were all the same person trying to jump the turnstile simultaneously.
The Axeploit Philosophy: Stop Trusting, Start Verifying
At Axeploit, we believe the only way to beat logic abuse is to build Context-Aware Applications. You cannot bolt this on with a third-party appliance. It has to be in the DNA of your code.
- Never Trust the Client: If the client provides a price, a user ID, or a permission level, ignore it. Recalculate it on the server using your source of truth (the database).
- Enforce State Integrity: Use "Flow Tokens" or server-side session state to ensure Step B cannot happen unless Step A was completed successfully.
- Atomic Operations: Use database transactions and locks to ensure that "Check-then-Act" sequences cannot be interrupted by a race condition.





