In today's fast-paced digital world, our smartphones are an extension of ourselves. We use them to chat with loved ones, manage our bank accounts, and store our most private thoughts. But what happens when the device you trust the most starts keeping secrets from you?
If you think deleting an app or erasing a message means it's gone forever, you might want to think again. A recent cybersecurity discovery in early 2026 has sent shockwaves through the tech community, revealing a hidden loophole that allowed the FBI to track and read private messages even after the user had completely deleted the app.
As an average phone user, you might feel overwhelmed by the technical jargon surrounding cybersecurity. But understanding how your phone can be used to track you, why it is deeply concerning, and exactly how you can stop it is more crucial now than ever.
The Silent Threat: How the FBI Tracks Your Phone
When we hear the phrase “phone tracking,” most of us picture dramatic movie scenes with GPS dots on a map or secret agents listening in on phone calls. The reality, however, is much quieter and far more sneaky.
Recently, cybersecurity experts uncovered a critical flaw in Apple's iPhone operating system (officially tracked as CVE-2026-28950). This flaw didn't involve planting a physical bug or breaking complex encryption. Instead, it exploited something we all ignore hundreds of times a day: push notifications.
https://x.com/signalapp/status/2047070518776356996?s=20
The Notification Loophole
Think about what happens when your friend sends you a text. Your phone screen lights up, and a small banner appears with a preview of the message. This is a notification.
Usually, once you read the message or clear the banner, you assume that notification is gone. However, due to a flaw in how Apple's system handled these alerts, the device was actually keeping a hidden, permanent log of these message previews. Even if you deleted the message or uninstalled the app entirely, the text from that notification was still buried deep within your phone's memory.
Even “Secure” Apps Weren't Safe
This tracking method became public when it was revealed that the FBI used this exact loophole to read messages from an app called Signal during a criminal investigation.
This is a massive deal because Signal is widely considered the absolute gold standard for private, encrypted messaging. The app itself is incredibly secure, but the FBI realized they didn't need to break into the app. They just needed to look at the phone's hidden notification logs. By doing so, they could piece together entire conversations that the user firmly believed were long gone.
Why This Kind of Tracking is Deeply Concerning
You might be thinking, “I'm not a criminal, and I have nothing to hide. Why should I care if the FBI can read my deleted notifications?”
It is a common mindset, but allowing this level of tracking sets a dangerous precedent for everyone. Here is why you should absolutely care.
The Illusion of Deletion
The most concerning aspect of this flaw is the violation of trust. When you tap “delete” on a sensitive message whether it's a password reset link, a private photo, or a confidential medical update, you expect it to vanish. If the software we rely on doesn't actually delete what we tell it to, we lose complete control over our own digital footprints.
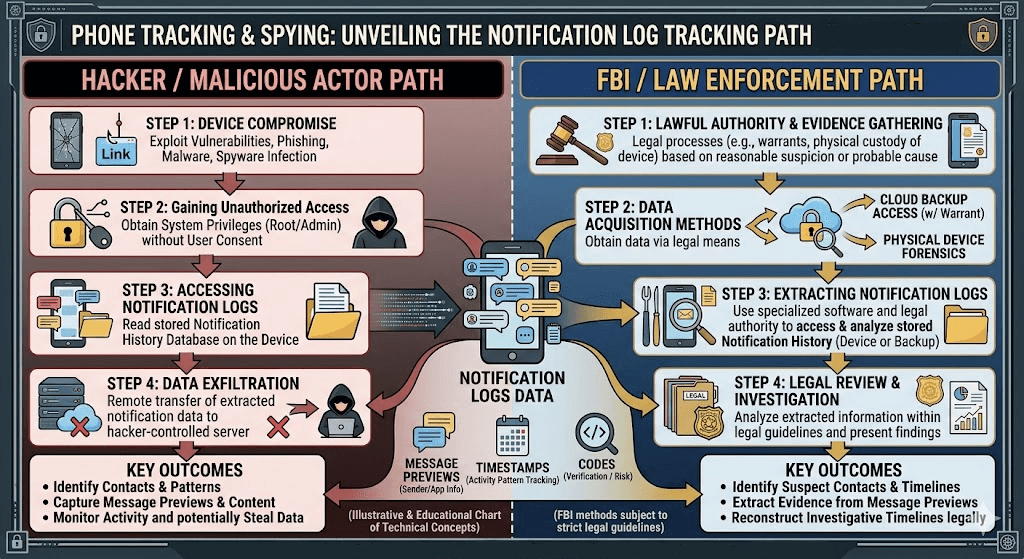
A Playground for Hackers
This isn't just about law enforcement. In the world of cybersecurity, there is a golden rule: if the good guys can find a backdoor, the bad guys will find it too. The same loophole that the FBI used to extract deleted messages is a dream come true for malicious hackers, identity thieves, and cybercriminals.
If a hacker gains access to your phone or infects it with spyware, they could potentially read months' worth of private notification logs. They could intercept banking codes, read intimate conversations, and steal personal information without you ever knowing. This is not a concern because hackers get access to your phone, but the FBI does, too. They use your information against you. The same information they unlawfully got by invading your privacy and hacking your phone. Both hackers and law are there to exploit you. It is up to you how you stay safe and protected.
Step-by-Step Guide: How to Stay Safe From Phone Tracking
The good news is that you don't have to be a computer genius to protect yourself. Hackers and tracking programs often rely on users being careless or outdated. By following these simple, actionable steps, you can secure your device and keep your private life exactly that, private.
Step 1: Update Your Phone Immediately
The absolute best defense against the notification tracking flaw is to update your device. On April 22, 2026, Apple released a patch specifically designed to fix this loophole and automatically clear out any old, lingering notification data.
- What to do: Grab your iPhone or iPad, go to Settings, tap General, and select Software Update. If you see version iOS 26.4.2 (or iPadOS 26.4.2), download and install it right away.
Step 2: Manage Your Notification Settings
If a notification doesn't show the content of your message, it can't be logged and read by snoops. Hiding your notification previews ensures that even if someone gets their hands on your phone, they can't read your incoming texts.
- What to do: Go to Settings, tap Notifications, and select Show Previews. Change the setting to When Unlocked or Never.
Step 3: Use Auto-Delete Features Wisely
While the recent Apple bug temporarily bypassed some of these features, updating your phone restores their effectiveness. If you are discussing sensitive information, use apps that offer self-destructing messages.
- What to do: In secure messaging apps like Signal or WhatsApp, look for the “Disappearing Messages” feature in the chat settings and set a timer for your messages to vanish automatically after they are read.
Step 4: Regularly Audit Your Apps
The more apps you have on your phone, the more chances there are for a privacy leak. Many apps track your background activity and send notifications you don't even need.
- What to do: Scroll through your phone once a month. If you haven't used an app in the last 60 days, delete it. This removes their access to your data and cleans up your device's memory.
Step 5: Restart Your Device Regularly
It sounds almost too simple, but turning your phone off and back on again is a powerful security tool. Restarting your phone clears out temporary memory caches and can actively disrupt certain types of hidden spyware that hackers use to track devices.
- What to do: Hold down the power button and volume button, slide to power off, wait a full minute, and turn it back on. Make this a weekly habit.
Conclusion: Taking Back Your Privacy
In an era where our data is constantly being harvested, understanding how the FBI tracks phones, and how hackers exploit those same methods, is your first line of defense.
The recent Apple notification flaw of 2026 serves as a harsh reminder that “deleted” doesn't always mean “gone.” However, by staying informed, keeping your devices updated, and taking control of your settings, you can shut the door on unwanted surveillance. You have a fundamental right to your privacy; make sure you are taking the easy steps to protect it. We recommend checking out Axeploit’s Blog for such helpful guides and resources on staying safe digitally.





