If you are building software in early 2026, your workflow is all about momentum. You are spinning up containers, orchestrating microservices, and utilizing AI coding assistants to turn ideas into deployed applications faster than ever before. As a modern “vibe coder,” your ultimate goal is to stay in that frictionless flow state and ship value to your users.
But while we’ve completely modernized how we write and deploy code, many developers are still clinging to a dangerously outdated mental model of network architecture. We assume that if our code is tucked safely behind a firewall, it's secure.
It’s time to shatter that illusion and talk about Zero Trust.
You have probably heard the term thrown around by security teams or seen it on vendor billboards, making it sound like an expensive enterprise product. It isn't. Zero Trust is a fundamental design philosophy.
The Fall of the Castle-and-Moat Architecture
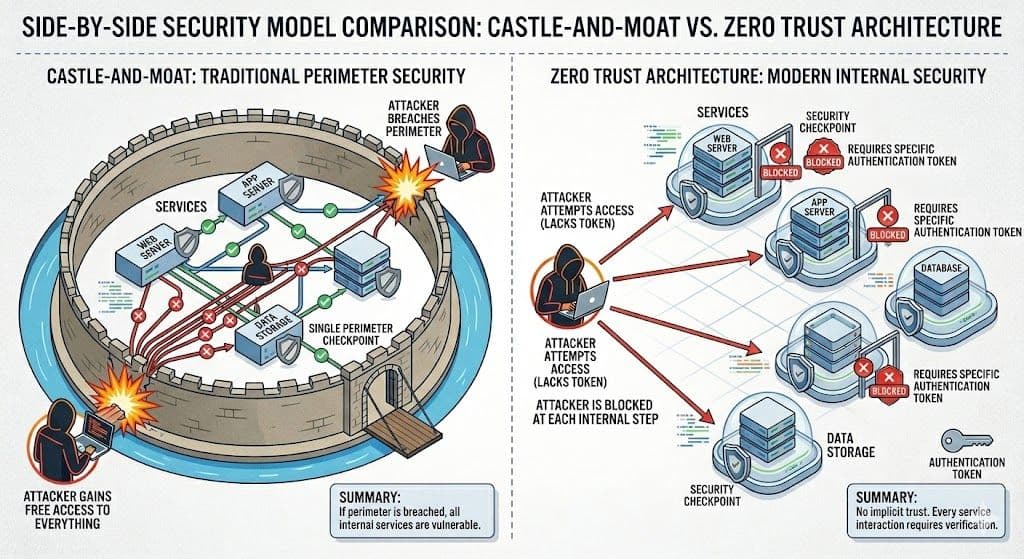
To understand Zero Trust, you first have to understand what it replaces: the “castle-and-moat” model.
For decades, network security relied on building a massive, fortified wall (the firewall) around your application (the castle). The assumption was simple: any traffic originating from the outside internet was hostile, but any traffic already inside the castle walls was trusted. If your Frontend Web Service wanted to pull data from your Internal Payment API, the connection was automatically allowed because they were on the same internal network.
Today, that perimeter has completely dissolved. We use cloud-native architectures, third-party integrations, remote workspaces, and highly distributed microservices. If an attacker manages to compromise just one low-level container, perhaps through a malicious open-source dependency or a phished credential, they are instantly inside your “castle.” In the old model, once they cross the moat, they have free rein to move laterally across your systems, escalating their privileges and stealing your data.
Demystifying the Buzzword: What is Zero Trust?
At its core, Zero Trust means exactly what it sounds like: Never trust, always verify.
For a developer, this translates to a very pragmatic rule: You must design every single service and API assuming the network it runs on has already been breached. You can no longer implicitly trust a request just because it comes from an internal IP address. Every request, whether it originates from a user halfway across the world or a microservice sitting on the exact same server rack, must be strictly authenticated and authorized before it is processed.
Core Principles of Zero Trust for the Modern Coder
Implementing Zero Trust doesn't mean slowing down your development cycle. It simply means adopting a few core principles into your daily engineering habits to prioritize developer security.
1. Service-to-Service Authentication
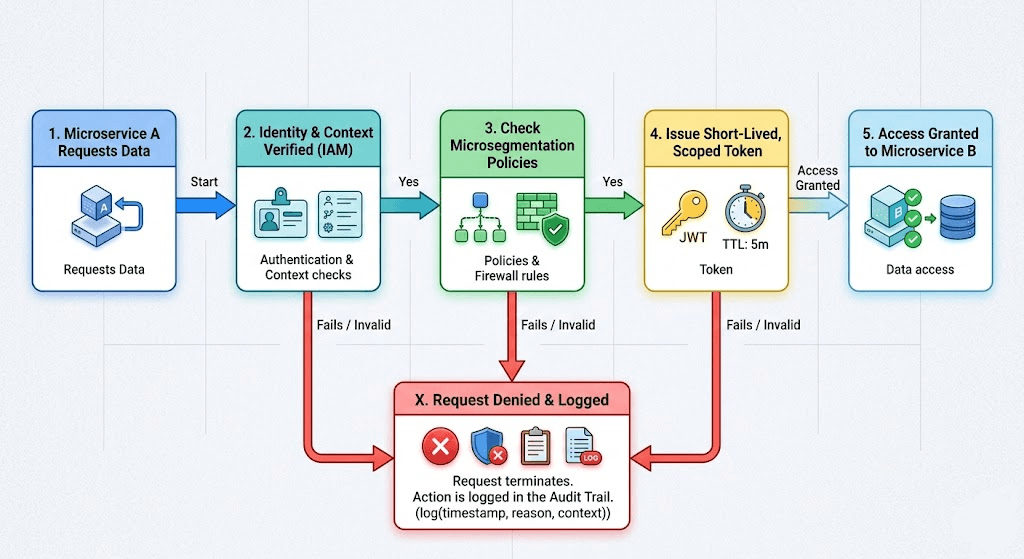
In a Zero Trust environment, microservices do not inherently trust each other. If Service A needs to talk to Service B, Service B must verify Service A's identity.
This is where robust identity and access management (IAM) comes into play. IAM is no longer just for human users logging into a dashboard; it is for machines, scripts, and containers. When your frontend requests data from your backend, it should present a cryptographically signed identity credential (like a mutual TLS certificate or an internal JSON Web Token). If the identity cannot be verified, the connection is instantly dropped, regardless of where the request came from.
2. Microsegmentation (The Watertight Compartments)
Think of your application like a modern submarine. A submarine isn't just one giant hollow tube; it is divided into multiple watertight compartments. If the hull is breached and one section floods, the doors lock, containing the water so the entire ship doesn't sink.
In software, this is called microsegmentation. Instead of a flat internal network, you segment your application into tiny, isolated zones. A marketing microservice should have absolutely no network path to your secure database unless it is explicitly required for a specific function. By compartmentalizing your architecture, you severely limit the “blast radius” of a hack.
3. Least Privilege Access and Secure Token Management
“Least Privilege” is the golden rule of Zero Trust. A user, service, or pipeline should only be given the absolute minimum level of access necessary to perform its specific job and only for the duration needed.
If your reporting service only needs to read data from a table, do not hand it a database token with global read/write/delete permissions. Use short-lived, tightly scoped access tokens. If an attacker compromises your reporting service and steals that token, they will find themselves trapped, unable to alter the database or use the token to access other parts of your infrastructure.
Building with Paranoia: A Pragmatic Workflow
As a vibe coder, your instinct is to remove friction. Zero Trust might sound like adding friction, but modern cloud providers and service meshes (like Istio or Linkerd) handle most of the heavy lifting. Your job is to adopt the mindset:
- Stop hardcoding secrets: Never embed API keys or internal database passwords in your code. Use a secure secrets manager.
- Validate everything: Never assume internal traffic is clean. Sanitize inputs and outputs even if the request is coming from your own backend.
- Log aggressively: In a Zero Trust world, anomalies are your best early warning system. Monitor failed authentication attempts between your internal services.
How Axeploit Fits into Your Zero Trust Strategy
Designing a Zero Trust architecture is the first step, but how do you know if you actually built it correctly? Misconfigurations are the enemy of security. A developer might accidentally leave an internal API endpoint unauthenticated during a late-night debugging session, effectively punching a hole right through your Zero Trust policies.
This is where traditional static code analysis falls short, and where the Axeploit API Security Checker becomes your ultimate safety net.
Zero Trust requires you to assume the network is compromised. Axeploit physically tests that assumption. Our automated vulnerability scanner doesn't just read your code; it actively attacks your live, running application from the outside, mimicking the exact behavior of a malicious hacker.
If you have a microservice that is bypassing your IAM controls, or an internal API endpoint that was accidentally exposed to the public internet without requiring a token, Axeploit’s dynamic scanner will catch it. It flags the vulnerability and shows you exactly how to patch it before you go live.
Conclusion: Trust Nothing, Ship Everything
The era of the protected internal network is over. By embracing Zero Trust, you aren't just locking down your infrastructure, you are empowering yourself to build faster and more resilient applications. When you know every service is verifying every request, you can confidently deploy code without worrying that one small mistake will bring down the entire castle.
Adopt the Zero Trust mindset, enforce least privilege, and Axeploit will continuously scan your blind spots. Keep building fast, and stay secure.





