Imagine you’re building a high-tech vault. You hire a world-class architect to look at your blueprints. They check the math, ensure the steel is thick enough, and confirm the lock is a top-tier model. They give you a thumbs up.
But when the vault is actually built, the construction crew forgets to plug in the security cameras. They leave the back door propped open for a breeze. They even write the combination on a sticky note near the keypad.
The architect’s “code review” was perfect, but the vault is still wide open.
In the world of cybersecurity in 2026, this is exactly what happens when developers rely solely on Large Language Models (LLMs), like ChatGPT or Claude, to "check their code" for security. While these AI tools are brilliant at finding typos or logic errors in text, they are often blind to how a system actually lives and breathes in the real world.
That is why Axeploit has become the essential shield for modern businesses. It doesn't just look at the “blueprint” (the code); it tests the “entire building” while it’s standing.
The LLM Trap: Why Good Code Can Still Be Dangerous
When you paste a snippet of code into an LLM and ask, “Is this secure?” The AI looks at the syntax. It’s like a very smart spellchecker. It might find a common mistake, but it has no idea where that code is going or what it’s talking to.
1. The “Isolation” Problem
An LLM only sees what you show it. It doesn’t see your Environment Variables (the secret keys that connect your app to your database). It doesn’t see your Nginx setup (the “digital receptionist” that directs traffic to your server).
If your code is ”perfect” but your Nginx configuration allows anyone to bypass your login screen, the LLM will never know. You’re essentially asking a nutritionist to check a recipe for healthiness without telling them the kitchen is covered in salmonella.
2. The Deployment Layer
In 2026, most apps will run on Node.js. To be secure, a Node.js server needs more than just clean code. It needs:
- Properly mapped ports: So hackers can't sneak in through the “back windows.”
- SSL Certificates: To ensure data is encrypted.
- Regular CVE Updates: A “Most Wanted” list of digital vulnerabilities that changes every single day.
An LLM checking a file from last week has no idea that a new “Zero-Day” (a brand new, unpatched hole) was discovered this morning.
Lessons from the “React2Shell” Crisis (CVE-2025-55182)
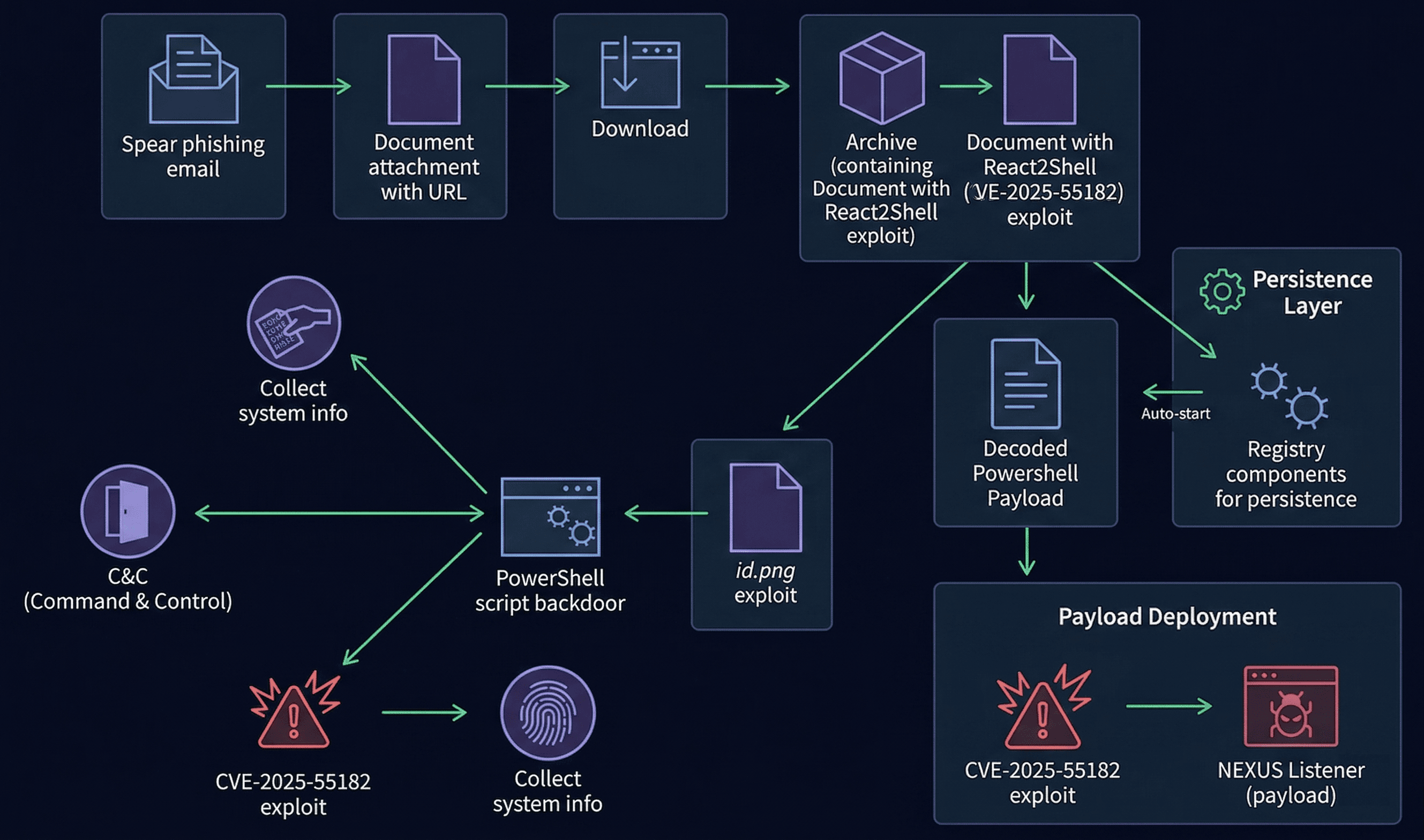
To understand why this distinction matters, we only have to look at the recent React2Shell vulnerability that rocked the tech world in April 2026.
This flaw (technically known as CVE-2025-55182) targeted websites built with Next.js and React. The “code” itself often looked fine to a human or an LLM. The problem wasn't a typo; it was how the React Flight protocol. The language the browser uses to talk to the server has handled specific types of data.
Hackers found that they could send a “confusing” message to the server that caused it to execute their commands. An LLM reviewing the code would see a standard data-handling function and think, “That looks like a normal way to receive data.” But Axeploit doesn't just “read” the function. It acts like a hacker. It sends those "confusing" messages to the live site to see if it breaks. It found the React2Shell vulnerability in minutes because it was testing the interaction, not just the text.
Why Axeploit is the “Security Guard,” Not Just the “Blueprint Reader”
Axeploit is fundamentally different from an LLM. While LLMs are built to generate and summarize, Axeploit is built to attack and defend.
Autonomous AI Agents vs. Static Checkers
Axeploit uses a fleet of autonomous AI agents. Think of these as a team of "friendly hackers" that you hire to try and break into your house every single day.
- They Sign Up: They actually create accounts on your site to test the registration flow.
- They Solve Challenges: They can handle mobile OTPs and email verifications.
- They Explore: They find hidden pages (subdomains) you forgot existed.
Zero-Config, Real-World Scanning
Most security tools require a PhD to set up. You have to tell them where every “door” and “window” is. Axeploit is “zero-config.” You give it a URL, and it figures out the rest. It identifies your APIs, your database connections, and your server setup automatically.
The Three Layers of Security an LLM Misses (But Axeploit Catches)
If you are running a Node.js server today, there are three critical areas where “clean code” isn't enough:
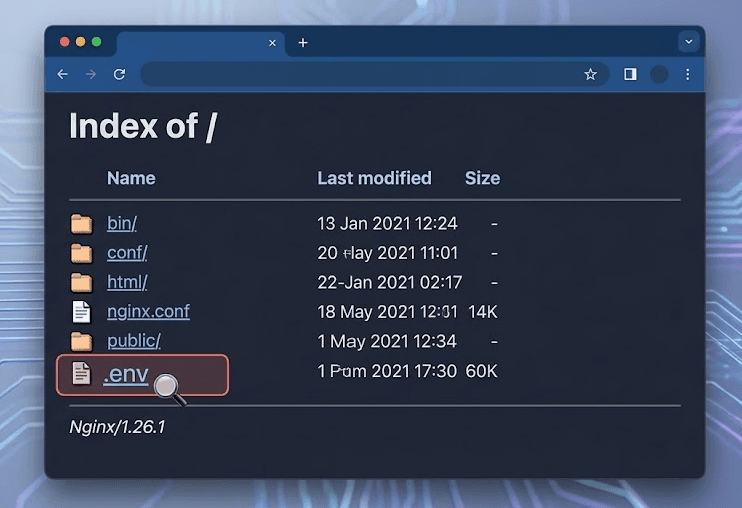
1. The Environment Variable (ENV) Leak
Developers often store their most sensitive keys (like Stripe for payments or AWS for storage) in an .env file. If your server is misconfigured, a hacker can sometimes trick the server into showing them that file. An LLM cannot “see” your server config, so it can’t warn you that your keys are sitting on the front porch. Axeploit tries to access those files from the outside, alerting you instantly if they are exposed.
2. The Nginx “Receptionist” Error
Nginx is the software that sits in front of your app to manage traffic. If it’s set up incorrectly, it might accidentally let people see your private administrative dashboard without a password. Axeploit’s “layout-aware” intelligence notices when a page that should be private is suddenly public.
3. The CVE “Treadmill”
New vulnerabilities are found constantly. In April 2026 alone, hundreds of new flaws were added to the global database. An LLM's knowledge is static, it only knows what it was trained on months ago. Axeploit stays on the “treadmill” for you, checking your system against a database of over 7,500 vulnerabilities that is updated in real-time.
Conclusion: Don't Bring a Spellchecker to a Cyber-War
LLMs are incredible tools for writing code faster, but they were never meant to be security experts. Using an LLM to secure your app is like using a dictionary to defend a fort. It might tell you the definition of “wall,” but it won't help you fill the gaps in one.
In an era where threat clusters like UAT-10608 are using automated bots to harvest digital keys from thousands of companies at once, you need a defense that is just as automated and just as smart.
By using Axeploit, you bridge the gap between “good code” and “secure deployment.” You ensure that your Node.js server, your Nginx setup, and your secret keys are all protected by an AI that knows how to think like the enemy, and stop them before they ever get close to the door.
Ready to see what the hackers see? Request access to Axeploit today and move beyond the blueprint.





