In September 2018, British Airways disclosed that approximately 380,000 customers had their payment card details stolen during a two-week window. The breach was not a database compromise, not a server-side vulnerability, not a network intrusion. It was 22 lines of JavaScript.
The Magecart group responsible for the attack had compromised a third-party script loaded on British Airways' payment page. The malicious code intercepted form submissions, extracted credit card numbers, expiration dates, and CVV codes, and sent them to a server the attackers controlled. The script was loaded from BA's own domain (it had been injected into a first-party script bundle that BA served from their CDN), but the supply chain compromise originated in a third-party component. The entire attack operated in the browser, below the visibility of BA's server-side security monitoring.
This incident was not unique. Magecart campaigns have targeted Ticketmaster (via a compromised Inbenta chatbot script), Newegg (via a skimmer injected into their checkout page), and hundreds of smaller e-commerce sites. The British Airways case was notable for its scale and the £20 million fine from the UK ICO, but the attack pattern , compromise a script that runs on a payment page, intercept form data in the browser , has been repeated thousands of times.
The Trust Model That Makes This Possible
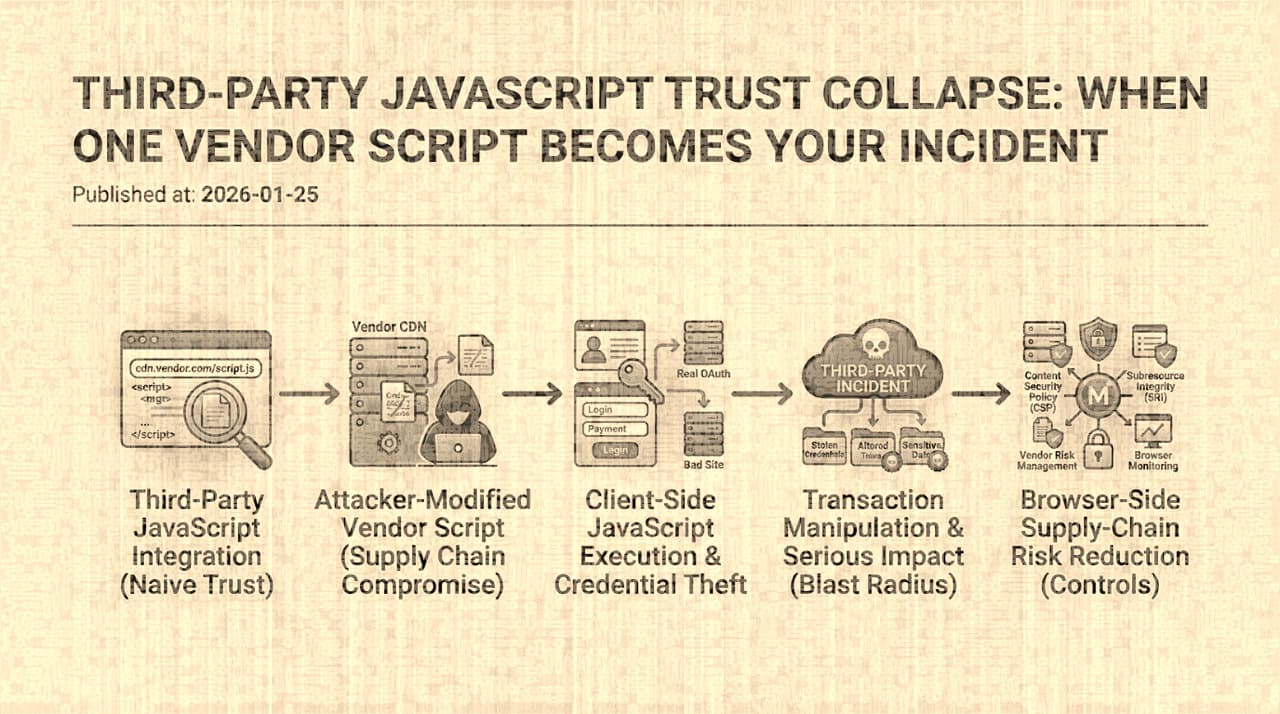
When a web page loads a third-party script , an analytics provider, a chat widget, an A/B testing tool, a tag manager, an advertising pixel , that script executes with the full privileges of the page. It can read the DOM, access cookies (unless they are HttpOnly), intercept form submissions, modify the page content, load additional remote scripts, and make network requests to any origin. There is no privilege separation between first-party and third-party JavaScript. The browser's same-origin policy protects against cross-origin access, but a third-party script loaded via a <script> tag runs in the first-party origin's context.
This means that adding a <script src="https://vendor.example/widget.js"> tag to your page is, from a security perspective, equivalent to granting the vendor deploy access to your production frontend. If the vendor's script is compromised , through an attack on the vendor's CDN, build pipeline, developer accounts, or hosting infrastructure , the malicious code executes in your users' sessions with your origin's authority.
The trust is transitive and recursive. The vendor's script may load additional scripts from other origins. Those scripts may load further scripts. Each layer adds another organization whose security posture you implicitly depend on. A tag manager that loads 30 third-party scripts creates a trust chain where a compromise of any one of those 30 vendors (or any of their sub-dependencies) can affect your users.
The Detection Gap
What makes browser supply chain attacks particularly dangerous is the detection gap between client-side compromise and server-side monitoring. Most security operations are server-centric: they monitor server logs, analyze network traffic at the infrastructure level, and alert on server-side anomalies. A browser-level attack that intercepts data before it is submitted to the server, or that modifies the page's behavior without changing the server's response, is invisible to these controls.
Consider the Magecart skimmer pattern:
The server receives a perfectly normal payment request. The transaction succeeds. The user sees a success page. The SOC dashboard shows no anomalies. Meanwhile, the payment data has been exfiltrated to a server the attacker controls, and nobody on the defending side knows until card fraud reports start arriving weeks later.
Beyond Card Skimming: The Full Attack Surface
Magecart-style payment skimming is the most publicized form of third-party JavaScript compromise, but the attack surface extends to every sensitive operation that occurs in the browser:
Credential harvesting. A compromised script can install a keylogger or form interceptor on login pages, capturing usernames and passwords before they are submitted. If the page uses client-side hashing or encryption before submission, the script can intercept the plaintext before the security measure is applied.
Session token theft. Cookies without the HttpOnly flag are accessible to JavaScript. A compromised script can read session cookies, authentication tokens stored in localStorage or sessionStorage, and JWT tokens used for API authentication. Even with HttpOnly cookies, a script can make authenticated API requests on behalf of the user (since the browser will attach cookies automatically) and exfiltrate the responses.
Transaction manipulation. A script running on a banking or e-commerce page can modify form fields before submission , changing the recipient of a transfer, the shipping address of an order, the amount of a payment , while displaying the original values to the user. The user sees their intended transaction. The server receives the modified one.
Content injection. A compromised script can overlay the page with phishing content , a fake login prompt, a "wallet verification" dialog, a "session expired" message that redirects to an attacker-controlled page. The content appears within the legitimate site's origin, inheriting all the visual trust signals (SSL indicator, domain name, page layout) that users rely on.
Defensive Architecture
The defenses against third-party JavaScript compromise operate at several layers, and no single control is sufficient.
Content Security Policy (CSP). CSP is the most important browser-level control for constraining script execution. A strict CSP that specifies exact script sources (not 'unsafe-inline', not 'unsafe-eval', not wildcard domains) limits which scripts can execute on the page. If a compromised vendor script attempts to load additional resources from an unapproved origin, CSP blocks the load. If a script is injected into the DOM (via a DOM XSS vulnerability), CSP with nonce-based script execution blocks it.
The challenge is that many third-party scripts are incompatible with strict CSP. They use eval(), they inject inline scripts, they load resources from multiple CDN domains, they dynamically create script elements. Deploying a strict CSP on a page that loads five third-party scripts often requires working with each vendor to ensure compatibility, which is a months-long process. This is a real cost, and it explains why many organizations deploy CSP in report-only mode (generating violation reports without blocking) or with overly-permissive policies that do not provide meaningful protection.
Subresource Integrity (SRI). SRI allows specifying a cryptographic hash for each script tag: <script src="..." integrity="sha384-...">. The browser verifies the hash before executing the script. If the vendor's CDN is compromised and serves a modified script, the hash check fails and the script is not executed.
SRI is effective when the script URL is stable and the content is versioned (e.g., vendor.v3.4.1.js). It is less effective when the vendor uses a single URL that always serves the latest version (e.g., vendor.js) , the hash would break every time the vendor updates, requiring the site operator to update the hash in sync with every vendor release. For vendors that deploy frequently, this operational burden often leads to SRI being abandoned.
Sandboxed iframes for high-risk widgets. Third-party content that does not need access to the parent page's DOM, cookies, or JavaScript context should be loaded in a sandboxed iframe with restrictive attributes: sandbox="allow-scripts allow-same-origin" (carefully chosen), allow with a minimal permissions list, and communication limited to postMessage with a strict protocol. This creates a genuine privilege boundary , the third-party code executes in an isolated origin and cannot access the parent page unless the parent explicitly receives and processes a message.
The trade-off is that sandboxed iframes constrain the vendor's functionality. A chat widget in an iframe cannot overlay the parent page's content. An A/B testing tool in an iframe cannot modify the parent page's DOM. Many third-party integrations exist precisely because they need first-party page access, which means iframe isolation is not applicable to them.
Client-side telemetry and behavioral monitoring. If you accept that some third-party scripts will run in first-party context (because the business requires their functionality), the fallback defense is monitoring their behavior at runtime. Client-side telemetry systems can detect anomalous behaviors: new outbound network connections to previously-unseen domains, unexpected DOM mutations on payment or authentication forms, script loads from origins not in the approved set, and mutation of transaction-critical fields.
This does not prevent the initial execution of malicious code, but it can detect the compromise quickly , reducing the window from weeks (waiting for fraud reports) to hours or minutes (detecting anomalous script behavior). The detection quality depends on the baseline: you need to know what normal script behavior looks like to identify deviations. This requires an initial investment in instrumenting the client side and building behavioral profiles for each approved script.
Vendor governance and kill-switch capability. At the organizational level, every third-party script should have a named owner, a documented business justification, a security assessment, and a kill-switch mechanism. If a vendor is suspected compromised, the team needs to be able to remove the vendor's script from all production pages within minutes, not hours. This requires that script loading is controlled through a configuration system (a tag manager, a feature flag, or a build-time configuration) rather than hardcoded in templates scattered across the codebase.
The Residual Risk
Even with CSP, SRI, iframe isolation, client-side monitoring, and vendor governance, third-party JavaScript remains a significant risk surface. The fundamental problem is that business requirements demand functionality (analytics, advertising, support, experimentation) that requires running untrusted code in the user's authenticated session. Every defense adds friction, operational cost, and potential for breakage. The perfectly-secured site that loads zero third-party scripts is not a site that most businesses can ship.
The pragmatic approach is to assume that vendor compromise will happen , it is a question of when, not if , and to design the defense stack so that the blast radius is bounded: CSP limits what the compromised script can load, SRI prevents tampering with version-pinned assets, iframe isolation constrains the script's access to sensitive context, client-side monitoring detects anomalous behavior, and the kill-switch allows rapid response.
The British Airways breach cost £20 million in fines and hundreds of millions in remediation and reputational damage, all from 22 lines of JavaScript on a payment page. The lesson is not that third-party JavaScript should be eliminated. It is that every <script> tag is a trust decision with quantifiable risk, and organizations that treat it as a routine frontend concern rather than a security architecture decision will eventually pay the price.