REST APIs have a useful security property that is so fundamental it rarely gets discussed: the server defines the response shape. When a client calls GET /api/users/123, the server decides which fields to include. If the server's handler does not include the user's social security number in the response, the client cannot request it. The authorization boundary and the data boundary are the same thing , the server endpoint.
GraphQL inverts this. The client sends a query specifying exactly which fields it wants, and the server resolves them. If the schema includes a socialSecurityNumber field on the User type, any client that can query a User can request it. The server must enforce authorization at the field level, for every field, on every type, across every possible query path. If it misses even one, the field is accessible.
This inversion is not a bug in GraphQL. It is the core design choice that makes GraphQL powerful: clients get exactly the data they need, no more and no less, in a single request. But the security consequence is that authorization becomes a pervasive, fine-grained responsibility distributed across hundreds or thousands of resolvers, rather than a coarse-grained responsibility concentrated in a handful of REST endpoints. And organizations that adopt GraphQL for its developer experience often discover, too late, that their authorization model was designed for the coarser REST paradigm and does not survive the transition.
Introspection: Handing Over the Blueprint
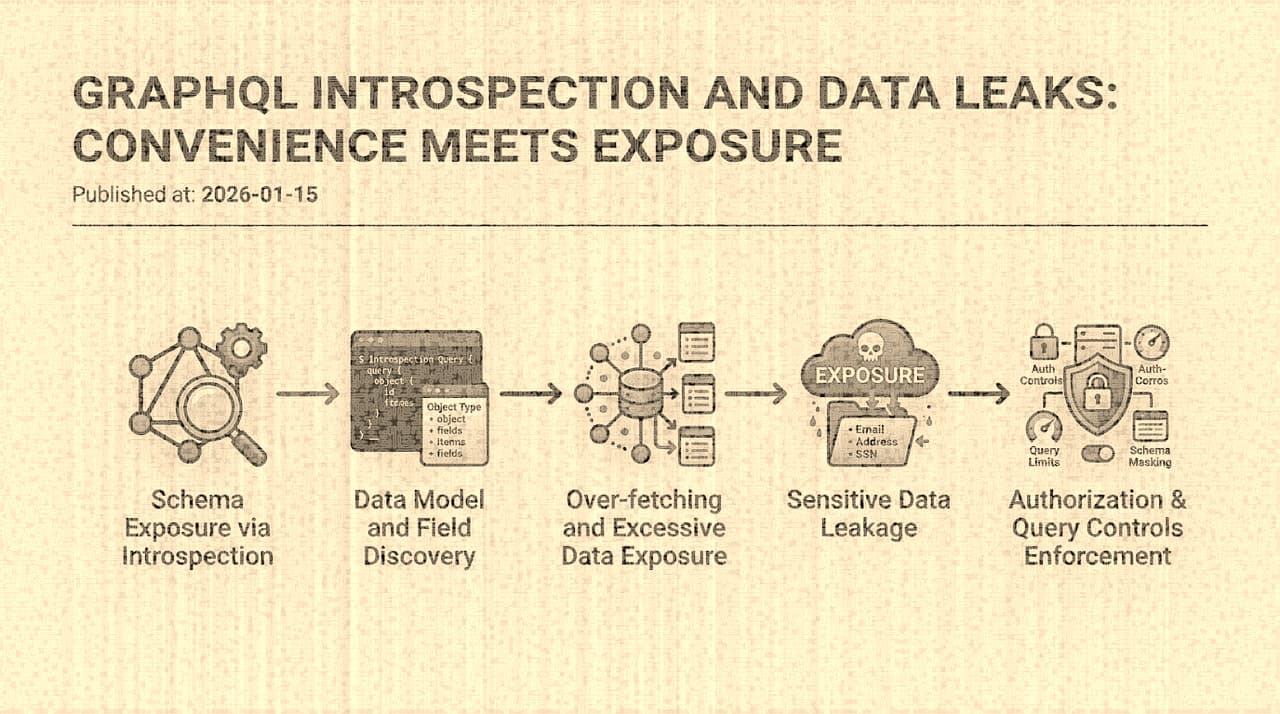
GraphQL's introspection system compounds the authorization challenge by giving attackers precise intelligence about the data model before they attempt any exploitation.
A standard introspection query , { __schema { types { name fields { name type { name } } } } } , returns the complete schema: every type, every field, every relationship, every mutation, every input type. In a REST API, an attacker would need to discover endpoints through documentation, brute-forcing, or traffic analysis. In a GraphQL API with introspection enabled, they get the equivalent of the full API documentation in a single request.
The intelligence value of introspection goes beyond simple endpoint discovery. The schema reveals:
-
Data model relationships that suggest access control boundaries. If
Userhas apaymentsfield that returns[Payment], andPaymenthas abankAccountfield that returnsBankAccount, the attacker can see the full traversal path from user to bank account and probe each relationship for authorization gaps. -
Mutation signatures that reveal privileged operations. A mutation named
updateUserRole(userId: ID!, role: Role!)tells the attacker that role management is exposed through the API, and the input types tell them exactly how to construct the request. -
Internal naming conventions that leak implementation details. Field names like
_debugInfo,internalNotes,legacyPassword, orisAdminreveal both the existence of sensitive data and the organization's naming patterns. -
Deprecation markers that identify legacy code paths. Deprecated fields often have weaker authorization because they are maintained for backward compatibility but excluded from recent security reviews.
In many organizations, disabling introspection in production is the single highest-leverage security improvement for their GraphQL API. It does not fix authorization bugs, but it dramatically slows down the attacker's reconnaissance phase. The counterargument , that developers need introspection for tooling , is valid, but the solution is to enable introspection only for authenticated internal clients or in development environments, not to expose it to the internet.
Where Authorization Breaks in Practice
The authorization failures in GraphQL APIs follow predictable patterns, and they are almost all consequences of the same root cause: resolver-level authorization being incomplete.
Nested object authorization gaps. The most common pattern. The top-level query enforces authorization , a user can only query their own profile. But the nested resolver for the profile's orders does not re-check authorization; it simply returns all orders associated with the profile. If the attacker can bypass the top-level check (through an IDOR in the user ID, or through a different query path that reaches the same type), the nested data is exposed without further checks.
Consider this query:
query {
user(id: "other-users-id") {
email
orders {
id
total
shippingAddress {
street
city
zipCode
}
}
}
}If the user resolver checks that the requesting user can access the target user, this is blocked. But what if the Order type is also reachable through a different path , say, a search query that returns [SearchResult], and SearchResult is a union type that includes Order? The search resolver might not apply the same ownership check that the user resolver does, because the search feature was built by a different team that did not know about the authorization model on the user path.
Field-level over-exposure. GraphQL schemas frequently include fields that were added for internal tooling and never removed. A User type might include passwordHash, mfaSecret, internalId, or lastLoginIp because the backend service exposes these fields and the schema was auto-generated from the data model. If field-level authorization is not enforced, these fields are queryable by any client.
Mutation authorization inconsistency. An organization carefully secures its updateUser mutation to ensure users can only modify their own profiles. But the adminUpdateUser mutation, which was built for internal tooling, has a weaker check , perhaps it only verifies that the caller has an admin role, but the role check is based on a JWT claim that is not properly validated. Or the mutation's authorization is implemented in middleware that was not applied to the admin routes because "admin routes are internal."
Batching and aliasing abuse. GraphQL allows sending multiple operations in a single request and aliasing fields to avoid name collisions. An attacker can use this to enumerate resources efficiently:
query {
a: user(id: "1") { email }
b: user(id: "2") { email }
c: user(id: "3") { email }
# ... hundreds more aliases
}If the API rate-limits by request rather than by operation, this single request retrieves data for hundreds of users while counting as one request against rate limits. Combined with a weak IDOR (sequential user IDs, no per-user authorization on the query), this enables rapid data enumeration.
Query Cost: The Denial-of-Wallet Problem
Beyond data exfiltration, GraphQL's query flexibility creates a distinct category of abuse: resource exhaustion through expensive queries. Because the client controls the query shape, a malicious client can construct queries that are syntactically valid but computationally catastrophic:
query ExpensiveQuery {
users(first: 1000) {
orders(first: 1000) {
items(first: 1000) {
product {
reviews(first: 1000) {
author {
orders(first: 1000) {
# Deep nesting continues...
}
}
}
}
}
}
}
}Depending on the backend's resolver implementation, this query could trigger millions of database queries. Depth limiting is the most common mitigation, but it is crude , it blocks deep queries regardless of their actual cost. A shallow query that fans out across a large collection (users(first: 100000) { email }) can be just as expensive as a deep one.
Query cost analysis , assigning a cost to each field based on its backend complexity and enforcing a per-query cost budget , is a more accurate approach but significantly harder to implement. It requires understanding the computational cost of each resolver, which depends on the backend implementation, the data distribution, and the query arguments. Most organizations that implement cost analysis do so imprecisely and iteratively, tuning budgets based on observed production query patterns.
Architectural Changes That Actually Help
The GraphQL security challenges described above are not amenable to simple fixes. They are consequences of the system's design, and addressing them requires architectural decisions:
Persisted queries for external clients. Instead of allowing arbitrary queries, register a set of approved queries at deployment time and only allow clients to reference queries by hash or ID. This eliminates the entire class of query-shape attacks , introspection-driven reconnaissance, expensive query construction, enumeration via aliasing , because the client cannot construct novel queries. Internal developer tooling can retain ad-hoc query access with appropriate authentication. This is the single most effective GraphQL security control for public-facing APIs, but it requires a deployment pipeline that extracts queries from client code and registers them.
Authorization at the data access layer, not the resolver layer. If authorization is implemented in each resolver function, it will inevitably be inconsistent. A more robust pattern is to enforce authorization at the data access layer , the ORM or database query layer , so that every data fetch, regardless of which resolver triggered it, applies the same access control policy. This is harder to implement because it requires the data layer to be aware of the requesting user's context, but it eliminates the "different resolver, different authorization" failure mode.
Schema design as security design. The schema should not be auto-generated from the data model. It should be deliberately designed to expose only the fields that external clients need, with sensitive fields explicitly excluded. Internal fields that are needed for admin tooling should be on separate types or behind a separate schema (a pattern sometimes called "schema stitching" or "federated schemas") with different authentication requirements.
The honest summary is that GraphQL is a powerful technology that shifts a significant security burden from the API design phase (where REST naturally constrains it) to the implementation phase (where every resolver must be independently correct). Organizations that adopt GraphQL without recognizing this shift , treating it as "just another API layer" , consistently discover authorization gaps the hard way. The schema is expressive. The resolvers are numerous. If even one is permissive where it should be restrictive, the attacker has access.