In 2002, Mitja Kolsek at Acros Security published a paper that gave a name to something pen-testers had been exploiting informally for years: session fixation. The core observation was disarmingly simple. If an attacker can cause a victim to authenticate using a session identifier the attacker already knows, then the attacker inherits the authenticated session without ever touching the victim's credentials. No brute-force. No phishing for passwords. No interception of tokens in transit. The victim does all the work of logging in, and the attacker walks in through a door that was never closed.
Twenty-four years later, this technique still works in production systems with alarming regularity. Not because developers are ignorant of it, but because the web's session model carries a structural tension that frameworks have never fully resolved: the tension between continuity and security at trust boundaries.
The Fundamental Problem: Sessions as Containers vs. Sessions as Credentials
HTTP is stateless. Everyone knows this. The entire purpose of the session layer , cookies, tokens, server-side stores , is to paper over that statelessness and give users a continuous experience. Add items to a cart before logging in, and they should still be there after. Start a multi-step form anonymously, and your progress should survive authentication.
This expectation of continuity creates a design assumption that is deeply embedded in web frameworks: the session is a container of user state, and authentication is just one attribute added to that container. The session ID is a handle to the container. Why would you throw away the container , and everything in it , just because the user proved who they are?
The answer, of course, is that the session ID is not merely a container handle. It is a bearer credential. Anyone who possesses it gains whatever authority the session currently carries. When the session transitions from "anonymous visitor" to "authenticated user," the authority associated with that identifier changes categorically. If the identifier itself does not change, then anyone who obtained it in the low-trust phase retains access through the high-trust phase.
This is the entire vulnerability. It is not a bug in any specific line of code. It is an architectural failure to treat trust transitions as requiring credential rotation.
How Fixation Attacks Actually Work
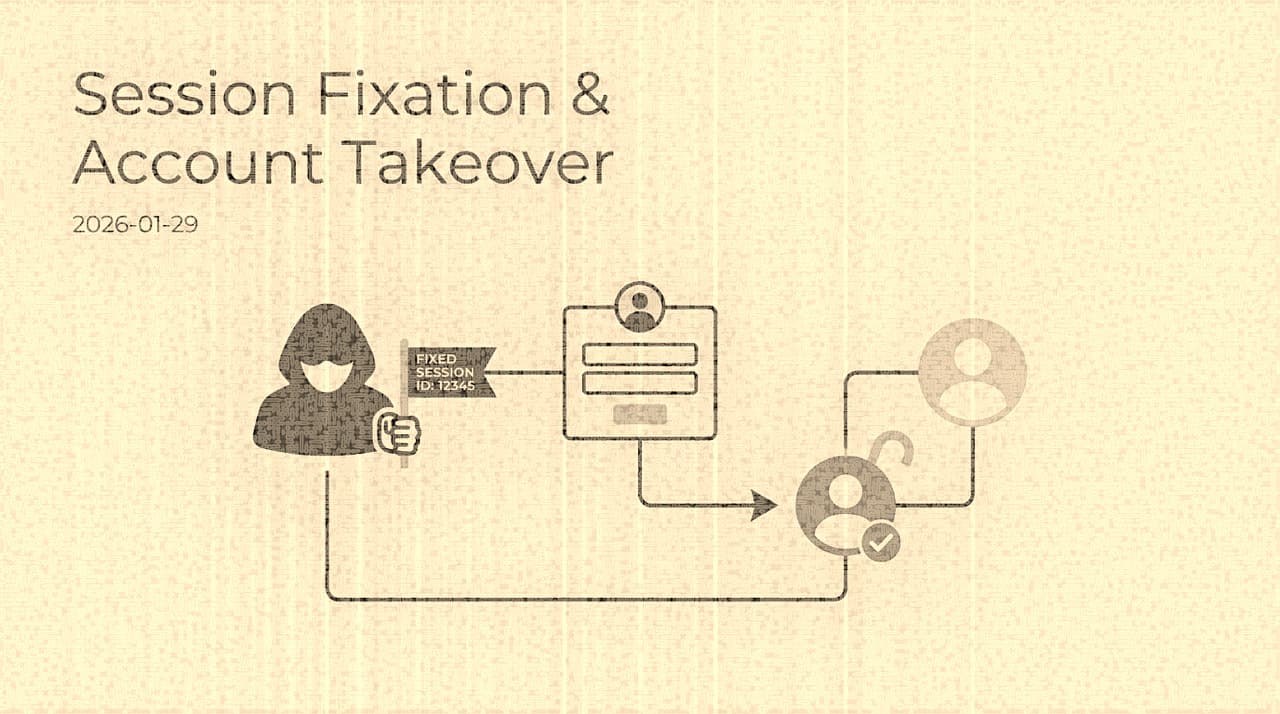
The mechanics vary by delivery method, but the pattern is consistent:
The critical moment is the server's decision at login: does it issue a new session identifier, or does it simply promote the existing one? If it promotes, the attacker's pre-existing copy of the identifier is now a valid authenticated credential.
Delivery of the known session ID to the victim can happen through several channels. The most common historically was URL-based session IDs (the JSESSIONID in Java servlet URLs, or PHP's PHPSESSID query parameter when session.use_only_cookies was off). Modern frameworks have largely closed that vector, but subdomain cookie injection remains viable in many architectures: if an attacker controls evil.example.com, they can set a cookie scoped to .example.com that the main application at app.example.com will happily accept. Cross-site scripting on any subdomain achieves the same result. And in some configurations, HTTP response header injection or meta-tag-based cookie setting can deliver the payload without any user interaction beyond clicking a link.
Why Frameworks Keep Getting This Wrong
You might expect that after two decades, every major web framework would rotate session identifiers on authentication by default. Some do. Django has called cycle_key() internally on login since its earliest stable releases. Rails regenerates the session in reset_session and Devise calls it automatically. Spring Security's SessionFixationProtectionStrategy has been available since Spring Security 2.0.
But "available" and "applied consistently across all authentication paths" are different things. The recurring failure pattern is not that the primary login form lacks rotation , it usually has it. The failures cluster at the edges:
SSO and federated callbacks. When authentication completes via an OAuth2 redirect or SAML assertion, the session rotation often happens in the IdP callback handler. But if the application has a fallback local-login path, or if the callback handler was written by a different team, or if a custom middleware intercepts the response before the framework's session rotation fires, the rotation may be skipped. The application works correctly for users , they are authenticated , so the omission is invisible in functional testing.
Remember-me and session rehydration. Persistent login tokens that restore a session from a cookie or database record frequently reconstruct the old session rather than creating a new one. If the remember-me token references a session ID rather than generating a fresh one, the original fixation attack may survive across browser restarts.
Step-up authentication. Applications that implement multi-factor authentication as a separate step after initial password verification sometimes treat the MFA completion as a session attribute change rather than a full trust transition. The session ID persists through the step-up, and if it was fixed before the first factor, the attacker inherits the fully-authenticated session after the victim completes both factors.
API and mobile auth flows. Token-based authentication in SPAs and mobile applications often coexists with cookie-based sessions. If the backend issues a JWT or API token but also maintains a server-side session (for CSRF protection, for audit logging, for feature flags), the session ID may not rotate when the API token is issued. The session becomes a shadow authentication credential that nobody explicitly manages.
The Subdomain Problem Deserves Special Attention
In organizations with complex subdomain architectures , which is to say, most organizations beyond a certain scale , cookie scoping is a persistent source of session fixation exposure. The browser's cookie model is generous: a cookie set for .example.com is sent to every subdomain. This means that the least-secure subdomain in the organization determines the session fixation exposure for the most-secure one.
Consider a typical enterprise with app.example.com (production application), staging.example.com (staging environment with relaxed security), blog.example.com (WordPress instance managed by marketing), and status.example.com (third-party status page with a custom domain). If any of these subdomains has a cross-site scripting vulnerability, an attacker can inject a session cookie scoped to .example.com that the production application will accept. The production app may have flawless session rotation on its own login form, but if it accepts a pre-existing session cookie from a subdomain it does not control, fixation is still possible.
This is why the __Host- cookie prefix (which requires Secure, Path=/, and no Domain attribute) is a meaningful security improvement. It prevents subdomain cookie injection entirely. But adoption remains low because it breaks legitimate cross-subdomain session sharing, which many applications rely on.
Detection and Forensics
Session fixation is difficult to detect after the fact because the attack produces a completely normal-looking authentication event. The victim entered valid credentials. The server issued a valid session. The session was used from... well, from a different IP or device, but that alone is not anomalous in a world of mobile networks, VPNs, and browser syncing.
The most reliable detection signal is dual concurrent use of a single session identifier from distinct network contexts. If session abc123 is active from IP A (the victim) and then immediately active from IP B (the attacker) without a logout or session expiry in between, that is suspicious. But this requires session-level telemetry that most applications do not collect. Standard web server logs capture request-level information, not session-continuity information.
A stronger signal is identifying sessions that were created significantly before the authentication event. In normal usage, the time between session creation (first visit) and authentication (login) is short , seconds to minutes. In a fixation attack, the attacker may create the session hours or days before the victim authenticates. A detection rule that flags authentication events on sessions older than a threshold can catch this pattern, though it requires recording session creation timestamps in the session store.
Remediation That Actually Holds
The primary remediation is simple to state and surprisingly difficult to implement comprehensively: regenerate the session identifier at every trust-level transition. Not just at login. At every point where the session's authority changes:
- Anonymous to authenticated
- Authenticated to MFA-verified
- Standard user to elevated privilege (admin impersonation, support mode)
- Pre-consent to post-consent in OAuth flows
- Before and after account recovery
The implementation must invalidate the old identifier server-side, not merely issue a new one. If the server generates a new session ID but keeps the old one valid (a "session aliasing" pattern some frameworks use for graceful rotation), the fixation vector remains open.
For the cookie itself, the minimum viable flags are well-established but still inconsistently applied:
Set-Cookie: sid=NEW_RANDOM_VALUE; HttpOnly; Secure; SameSite=Lax; Path=/HttpOnly prevents JavaScript access (mitigating XSS-based theft, though not fixation via subdomain injection). Secure prevents transmission over plain HTTP. SameSite=Lax prevents cross-site request attachment in most scenarios. Omitting the Domain attribute , or using the __Host- prefix , prevents subdomain scoping.
Beyond the cookie mechanics, the session store itself should bind sessions to context signals that make stolen or fixed sessions difficult to reuse. Hard-binding to IP addresses is too brittle for mobile networks, but softer signals , ASN, rough geolocation, TLS fingerprint, device characteristics , can feed a risk score. When the risk score for a session changes sharply (suggesting the session has moved to a different environment), the application should require step-up authentication rather than silently accepting the session.
The Broader Lesson
Session fixation persists not because it is technically exotic, but because it falls into an organizational gap. Authentication is a security concern, so security teams review it. Session management is an infrastructure concern, so platform teams own it. The vulnerability lives at the intersection , at the moment authentication state changes but the infrastructure handle does not , and that intersection is nobody's primary responsibility.
The fix is not a checklist item. It requires treating session lifecycle as a security primitive, with the same rigor applied to session transitions as to password hashing or TLS configuration. Until frameworks enforce rotation at trust boundaries by default , with no opt-out, across all authentication paths , this twenty-year-old technique will continue to work in production systems that are, by every other measure, well-defended.
Authentication proves who logged in. Session governance determines who remains in control. They are not the same problem, and they cannot be solved by the same team working in isolation.